
If you’re looking for Internet security software online, you’ll see we’re right up there in the ratings. And it seems that we’re №1 with spammers too.
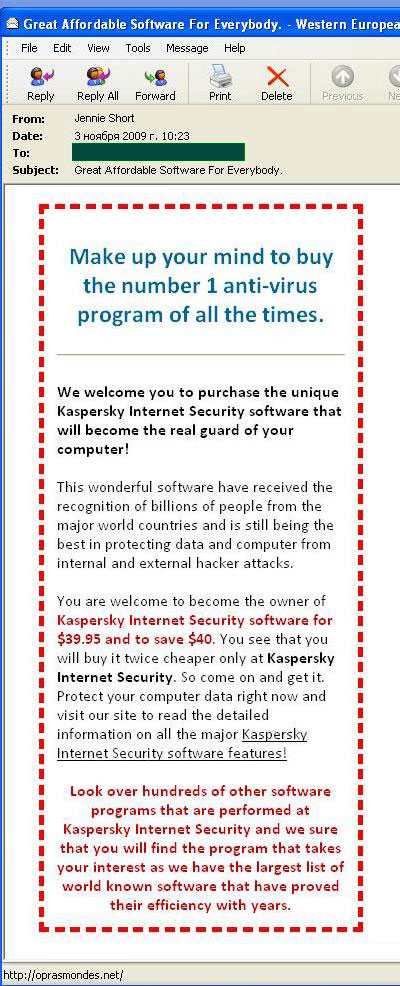
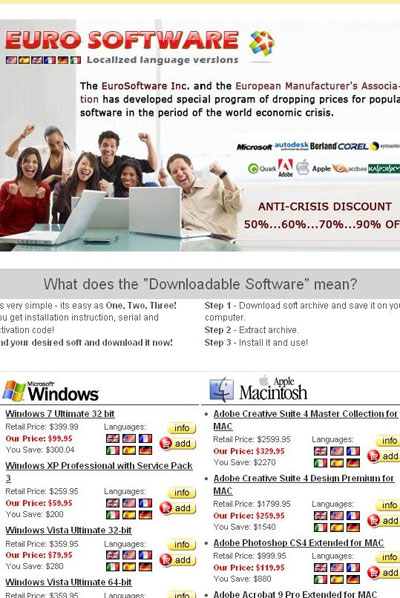
You might think we’d be happy to have our name all over this spam – pretty good advertising. But because we’re in the security business, we take a dim view of this type of thing: spam is criminal, spreads malware and hogs bandwidth. The link leads to a site selling all sorts of cheap (i.e. pirate) software:
This is advertising we don’t need. Sure, we want people to buy our product, because we know it’s good. And on a more banal note, yes, our product is our bread and butter.
You might save money buying a pirate version, but think of the consequences. You get a product which won’t work properly (leaving your computer at risk) and you’ll be egging the cybercriminals, malware writers and spammers on to new heights.






















Who’s №1?