
A new Twitter XSS exploit was identified in the wild as it started to be used by cybercriminals overnight.
The malicious JavaScript payload that’s being distributed is rather simple. It uses an XSS (Cross-Site Scripting) vulnerability to steal the cookie of the Twitter user, which is transferred to two specific servers. Essentially, any account which clicked on the malicious links is compromised.
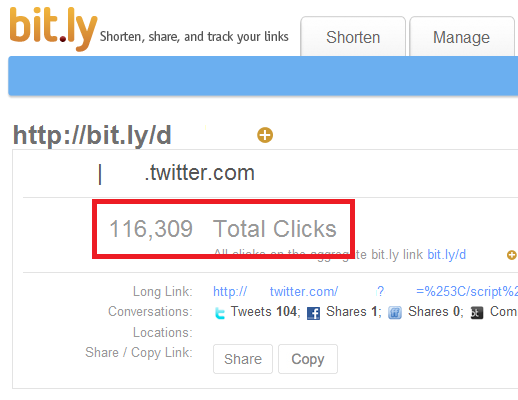
But how many people clicked the link? The bit.ly statistics for one of the malicious links are more than worrying, showing an alarming number: more than 100.000.
All clues point to Brazil as the originating country for this attack. First, the 2 domain names used to get the stolen cookies are registered under Brazilian names. More than that, one of them is actually also hosted in Brazil. Last, but not least, just take a look at the tweet used in distributing this malicious payload:
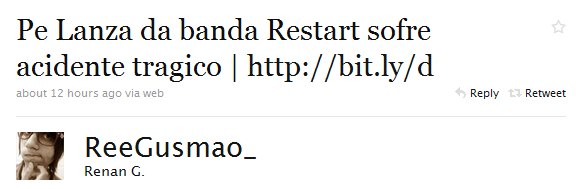
Pe Lanza da banda Restart sofre acidente tragico – it’s a short tweet in Portugese about the Brazilian pop band Restart suffering a “tragic accident”. I’d say there’s not much doubt about the origins of this attack.
We’ve added detection for the malicious scripts as Exploit.JS.Twetti.a and also made sure the URLs used in this attack are denylisted. We are currently working on taking down the malicious URLs and minimizing the damage as much as possible. Twitter along with other significant industry peers have of course been notified.
UPDATE: Twitter has confirmed the vulnerability is fixed now.






















Twitter XSS in the wild