
I blogged a week ago about a Trojan for mobile devices called Sejweek. We’ve just detected a new version – what’s changed in the course of a week?
First, the URL has changed: Sejweek.b (the latest variant) downloads an XML file from http://unique*****.com/*****/get.php, which is a different URL from the one used by the previous version.
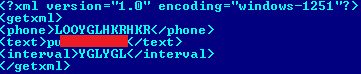
Second, the XML file which the link leads to has been modified – now the file looks like this:
And third, although Sejweek still sends SMS message to a short, premium-pay number, it’s now sending them to 7122 (a different number to that used by the previous variant), and each SMS costs $10.
The one thing that hasn’t changed is that Sejweek will still send SMS messages every 11 seconds, so there’ll still be a severe impact on your account balance. And finally, do be careful: Sejweel disguises itself as a whole range of applications, so don’t download anything unless you’re sure you know what you’re getting.






















Trojan.Sejweek: a new variant