
New programs targeting mobile devices rarely hit the headlines anymore; we’ve got used to smartphone malware. But occasionally something comes along that stands out a bit: right now, it’s Trojan-SMS.WinCE.Sejweek.a, a new program designed to send SMS messages from an infected device. What makes it different from other SMS Trojans? Let’s take a look.
Most malware which sends SMS messages to premium-rate numbers use a number and a message text which are coded into the malware itself. Sejweek is a bit different though – when run, the Trojan tries to download an XML file to the smartphone from http://today*******.cn/*****/*****/get.php. At the time of writing, the file looked like this:
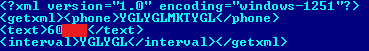
This file contains the premium-rate number (surrounded by the <phone> tag); the SMS text (<text>); and how long should elapse between each SMS message being sent (<interval>). Putting the number in a separate file, rather than in the malware itself, makes it easy to change the number if the first one gets blocked, extending the whole money-making cycle and maximizing profits.
If the XML file gets downloaded correctly, the malware decrypts “YGLYGLMKTYGL” and “YGLYGL” (i.e. the number SMSs get sent to, and the time between SMSs) and gets “1151” and “11”. In other words, messages saying 60*** are sent to the 1151 premium-rate number with an interval of 11 seconds between messages. With one SMS sent to 1151 costing around 40 roubles (a bit over $1) owners of infected devices will quickly start counting their losses!






















Trojan-SMS.WinCE.Sejweek