
On the eve of major holidays such as Christmas and New Year, mail and delivery services face a dramatic increase in the amount of shipments they have to handle. People are buying far more goods online than usual, looking for bargains in the sales, and sending gifts by mail – both nationally and internationally – to friends and relatives. To ease their customers’ nerves, delivery services send email notifications and provide shipment tracking systems. However, this type of communication also creates the ideal conditions for cybercriminals to send phishing messages in the name of major delivery services, and we end up with an increase in the number of these messages.
The fraudsters have a clear aim: to trick unwitting users into downloading a malicious program or entering their confidential data on a phishing site. For example, one scam message detected by Kaspersky Lab asked the user to fill in and sign a delivery form in order to receive a shipment. The message had a DOC file attached to it containing the exploit Exploit.MSWord.Agent.gg, which allowed the cybercriminal to, among other things, gain remote access to the infected computer.
Phishing message containing Exploit.MSWord.Agent.gg
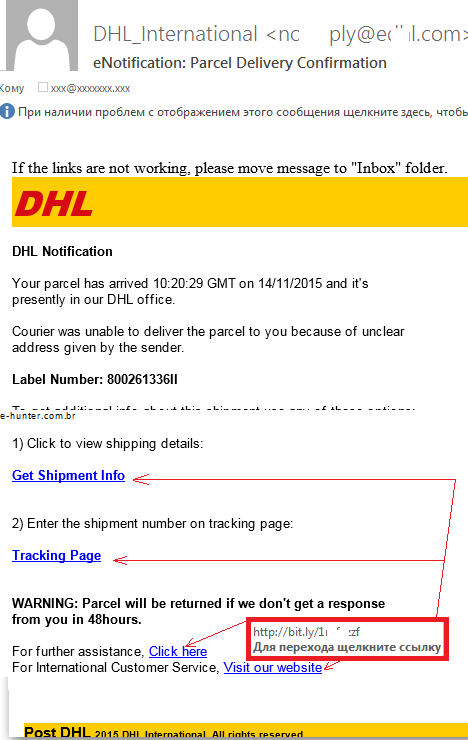
In another scam message the fraudsters write that the shipment is already at a DHL office, but the courier cannot deliver it because the delivery address is unclear. The recipient is asked to follow a link within 48 hours and enter the shipment number on the tracking page; otherwise, the shipment will be returned to the sender.
A closer inspection reveals that none of the links in the message lead to the DHL site; instead they all point to the same URL packed with the help of a URL shortening service. Another typical fraudster trick is also used in the email – the victim is warned there is a limited amount of time to react (in this case, 48 hours). If the user fails to follow the link in time, the shipment will be returned to the sender. The plan is simple – distract users with warnings about the urgency of doing something quickly rather than giving them time to think things through logically.
If unwitting users follow the link, they are taken to a specially crafted site in the corporate style of DHL, and are prompted to type in their login credentials to enter the shipment tracking system.
The data entered on sites like this is certain to end up in the hands of cybercriminals. The user will receive a message such as “Your account has been successfully updated”, and will be taken to the official DHL site, which will convince the victim that the operation was legitimate.
A similar situation exists around FedEx, another large delivery service provider. Kaspersky Lab has detected multiple phishing messages sent in the name of this company.
A fraudulent message sent in the name of FedEx
There’s nothing new about this scheme – the victim enters account credentials on a crafted site in order to view information about a shipment.
Phishing site masquerading as the FedEx site
The fact that this site is fraudulent and has nothing to do with FedEx is clear from the URL in the browser address bar.
The conclusion that can be made from the examples given above is that you shouldn’t be too trusting or inattentive while you are online. Never follow links in email messages; it’s safer if you manually type the URL of the required site in your browser address bar. Whenever a page prompts you to enter confidential data, always check the URL in the address bar first. If anything looks suspicious in the URL or in the website design, think twice before entering any personal data.
Last but not least, always keep your security software up to date; it should also include an anti-phishing tool that will help you keep your data confidential, and your money safe. That way, you will be in a good mood for the holidays.
























Tis the season for shipping and phishing