
2021 is the second year we have spent living and working in the pandemic. By 2021 everyone got used to pandemic limitations – industrial organization employees and IT security professionals and threat actors. If we compare the numbers from 2020 and 2021, we see that 2021 looks more stable, particularly in H2.
H2 2021 Report at a glance
The full report is available on the Kaspersky ICS CERT website.
Percentage of ICS computers on which malicious objects were blocked
The percentage of ICS computers on which malicious objects were blocked in 2021 increased by 1 percentage point from 2020 – from 38.6% to 39.6%.
In H2 2021 this percentage decreased by 1.4 p.p. for the first time in 1.5 years.

>Percentage of ICS computers on which malicious objects were blocked (download)
As we can see from the graph depicting the monthly dynamics of the percentage of attacked ICS computers, the numbers in H2 2021 were more stable than in H1 – the numbers were lower and there were no sharp fluctuations.

Percentage of ICS computers on which malicious objects were blocked, January – December 2018 – 2021 (download)
It is also worth noting that in 2021 the vectors of monthly fluctuations (increases and decreases) are the same as those in 2019 and, particularly, in 2018 more often than in 2020. Specifically, we can see decreases in July and August that we believe are due to the traditional vacation periods. However, compared to 2018 and 2019, the summer decrease in the percentage of ICS computers on which malicious objects were blocked was less pronounced in 2021.
Selected industries

Percentage of ICS computers on which malicious objects were blocked in selected industries (download)
Malicious objects
In H2 2021 Kaspersky security solutions blocked over 20,000 malware variants from 5,230 families on ICS computers.

Number of malware families blocked on ICS computers (download)

Number of malware variants blocked on ICS computers (download)
The results of our analysis revealed the following estimated percentages of ICS computers on which the activity of malicious objects from different categories had been prevented:

Percentage of ICS computers on which malicious objects from various categories were blocked (download)
Since H1 2020, we have seen increases in the percentages of ICS computers on which the following types of objects were blocked:
Spyware – by a factor of 1.4 — from 5.6% to 8.1%.

Percentage of ICS computers on which spyware was blocked (download)
Malicious scripts and phishing pages – by a factor of 1.4 – from 6.5% to 9.3%.

Percentage of ICS computers on which malicious scripts and phishing pages (JS and HTML) were blocked (download)
Cryptocurrency miners (Windows executable files) – more than doubled – from 0.9% to 2.1%.
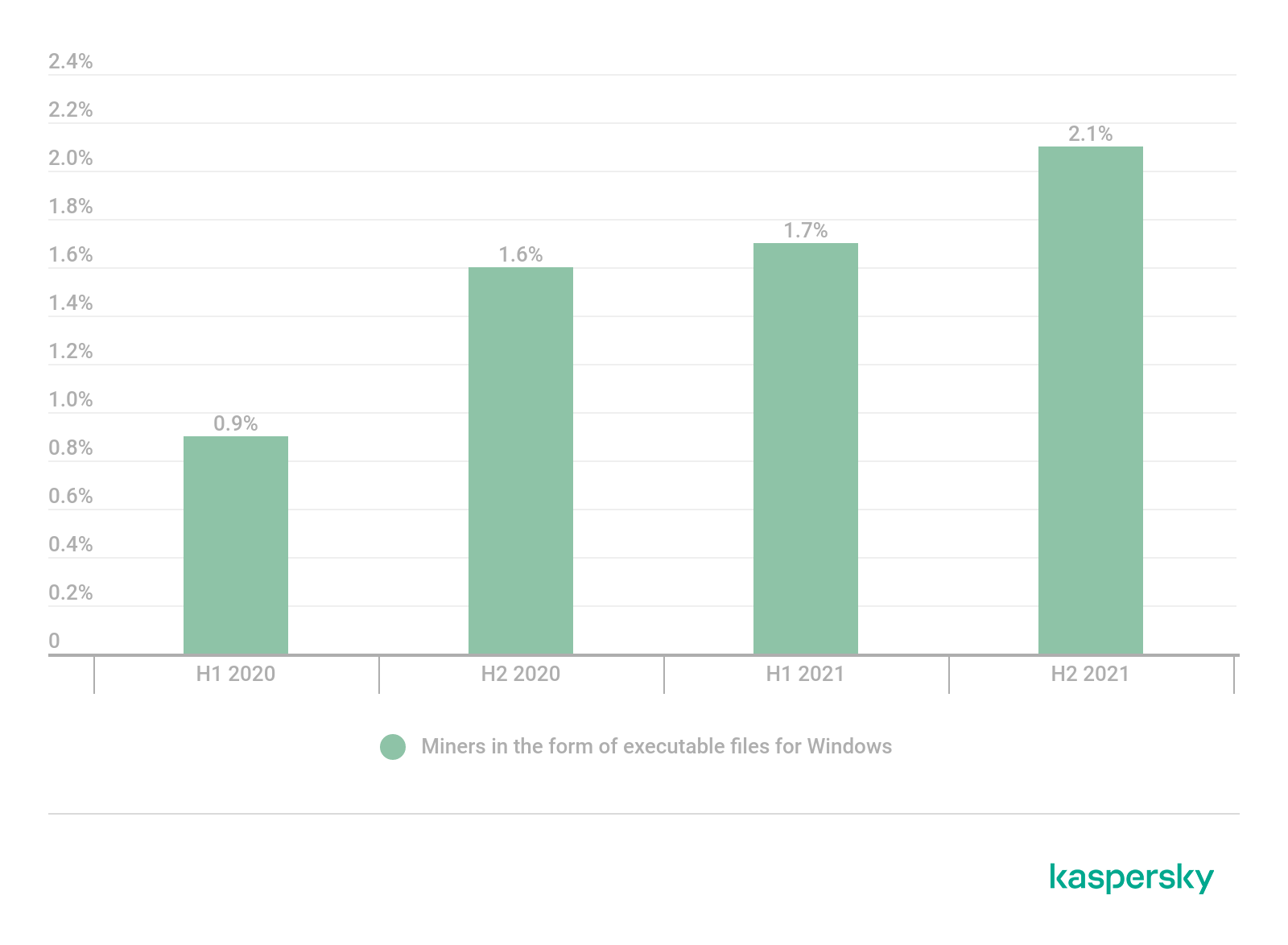
Percentage of ICS computers on which cryptocurrency miners were blocked (download)
Ransomware
In H2 2021 ransomware was blocked on 0.50% of ICS computers.
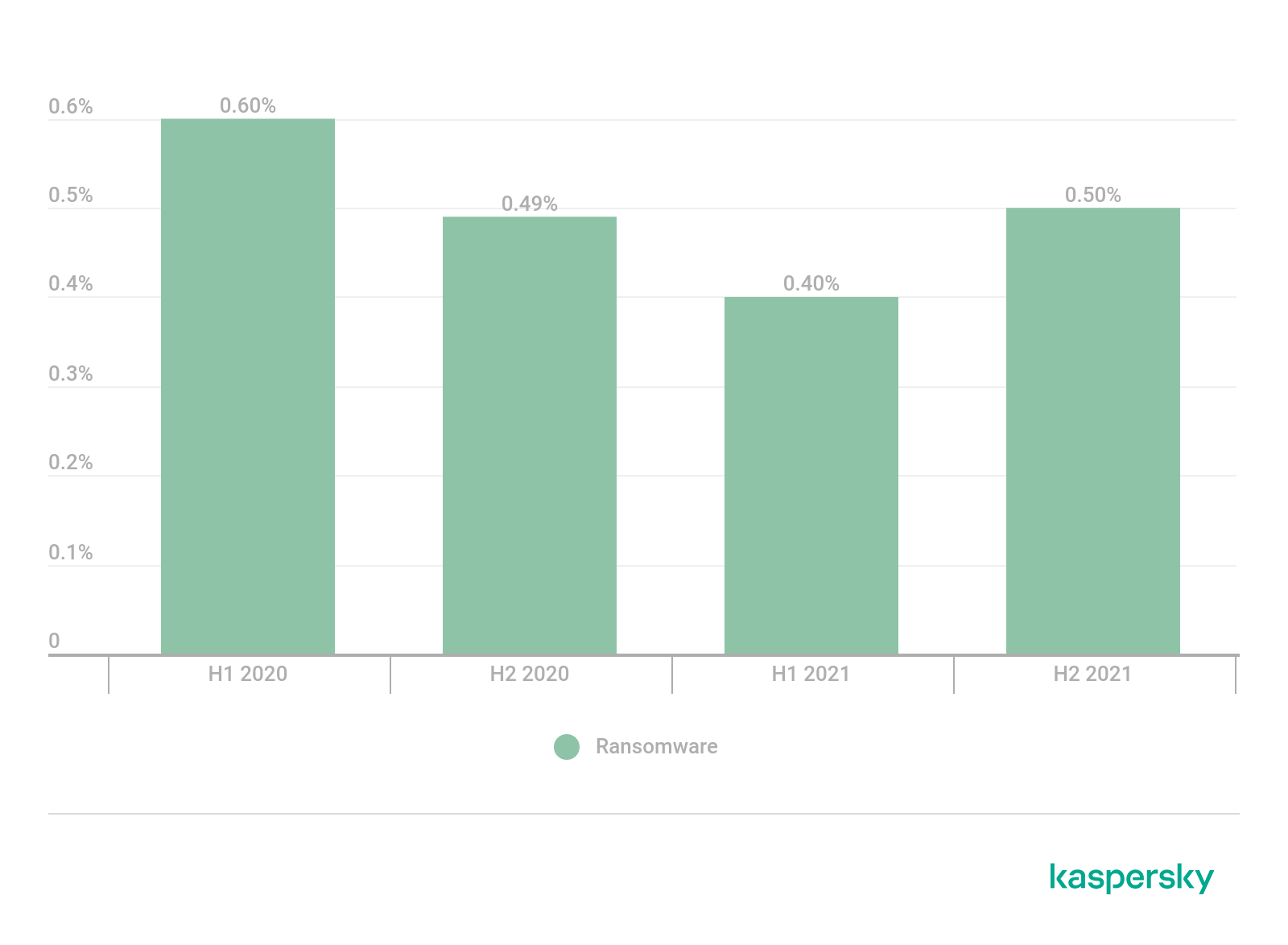
Percentage of ICS computers on which ransomware was blocked (download)
The percentage of ICS computers attacked by ransomware increased in half of the world’s regions. The most significant increases were recorded in Southeast Asia, East Asia and Africa, which are thus the leaders in this ranking.

Regions ranked by percentage of ICS computers on which ransomware was blocked, H2 2021 (download)
Main threat sources
The internet, removable devices and email continue to be the main sources of threats for computers in the OT infrastructures of companies and organizations.

Percentage of ICS computers on which malicious objects from various sources were blocked (download)
Shared network folders are one of the minor threat sources. Only on 0.57% of attacked ICS computers malicious objects were blocked in network shares in H2 2021. However, this percentage is slowly growing and is over 1% in a few countries and territories.

Percentage of ICS computers on which malicious objects were blocked in shared network folders (download)

Countries and territories with the largest percentage of ICS computers on which malicious objects were blocked in shared network folders in H2 2021 (download)
2021 in numbers
| Indicator | H1 2021 | H2 2021 | 2021 |
| Percentage of attacked ICS computers in the world | 33.8% | 31.4% | 39.6% |
| Percentage of attacked ICS computers by region | |||
| Northern Europe | 11.1% | 10.4% | 12.1% |
| United States and Canada | 16.5% | 17.2% | 19.7% |
| Western Europe | 15.3% | 15.8% | 20.2% |
| Australia and New Zealand | 23.7% | 21.4% | 26.5% |
| Eastern Europe | 29.5% | 28.4% | 32.4% |
| Southern Europe | 29.4% | 25.1% | 33.0% |
| Latin America | 32.8% | 32.5% | 38.7% |
| South Asia | 35.2% | 35.6% | 41.0% |
| Middle East | 37.3% | 34.3% | 42.0% |
| Russia | 39.4% | 30.0% | 42.3% |
| Central Asia | 42.0% | 37.9% | 44.7% |
| East Asia | 43.2% | 40.5% | 48.1% |
| Africa | 46.1% | 43.4% | 50.9% |
| Southeast Asia | 44.2% | 47.6% | 51.2% |
| Main threat sources globally | |||
| Internet | 18.3% | 16.5% | 22.2% |
| Removable devices | 5.2% | 4.8% | 6.7% |
| Email clients | 3.5% | 3.7% | 4.2% |
| Network folders | 0.52% | 0.57% | 0.75% |
For more information, visit the Kaspersky ICS CERT website
















Threat landscape for industrial automation systems, H2 2021