Why You Shouldn’t Completely Trust Files Signed with Digital Certificates
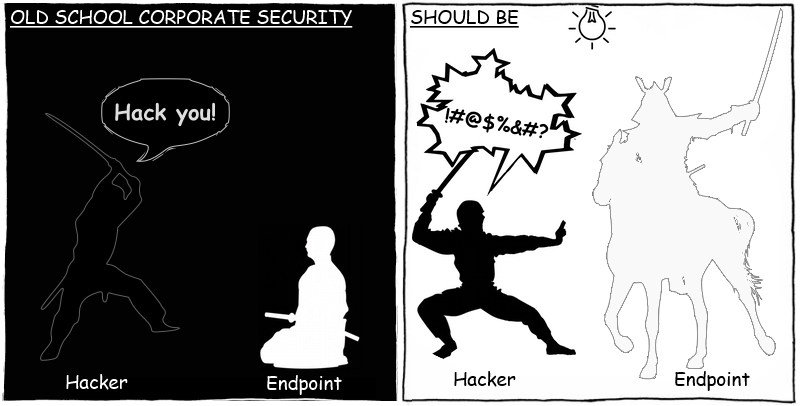
Users trust files signed with digital certificates, so cybercriminals are always keen to attach these certificates to their malicious files. This article explores the main threats associated with signed files, and proposes practical ways of minimizing the risks associated with launching them.