
While I was reading the Wired article on how Alberto Gonzalez, the TJX hacker who caused $171.5 million in losses, was sentenced to 20 years in prison, I came across an interesting black SEO campaign that distributes fake AVs through Google.
Here’s how the Google SERP looked like after my innocent search for this hot topic:
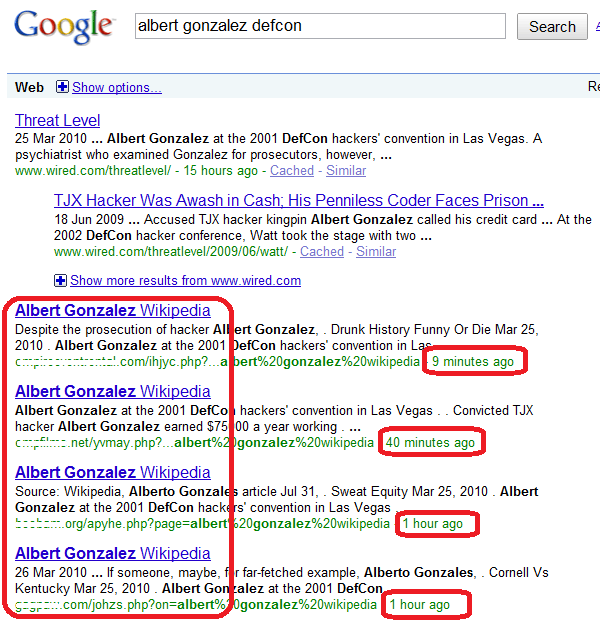
As you can see, some odd looking links are among the first results. And those links appeared very recently in the Google results page, within the last hour to be more specific. Still, the link that showed up just “9 minutes ago” is actually the second result in the Google ranking, right after the Wired article. Makes you think of how hard the cybercriminals are working to bypass Google’s algorithms, eh?But what’s with these links? Well, they might look like legitimate Wikipedia articles to the untrained eye, but they’re not. These randomly named PHP scripts were uploaded to compromised legitimate websites and then spammed using black SEO techniques right to the top of the Google results page.
The URLs look like this:
h**p://*****ms.net/yvmay.php
h**p://***************ring.com/cedxz.php
h**p://*****m.org/apyhe.php
h**p://*****w.com/johzs.php
h**p://*****pod.com/oagnz.php
h**p://**********arm.com/lekgz.php
etc
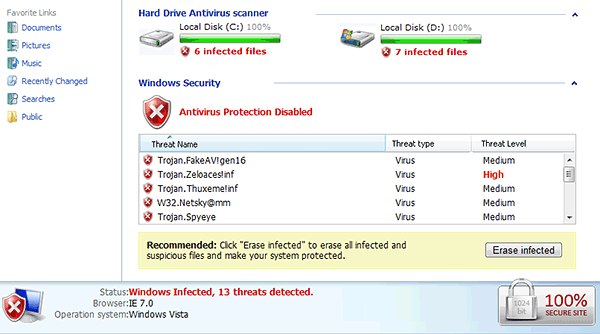
All these links are not malicious by themselves, but they serve as redirectors – sending all the traffic towards one main malicious website hosted on h**p://************.**rg.pl/ which is distributing fake antivirus software (or rogue AVs) that looks like this:
We were able to reproduce the attack on almost all of the hot searches on Google at that time.
Of course, this is simply yet another example of how cybercriminals are using good or bad
news happening around the world to try and push out their malware.
A lot of cyber security depends on each and every one of us – be careful out there and, if in doubt, don’t click! 🙂






















The TJX Hacker Black SEO Campaign