
Microsoft recently announced the shutdown of its popular IM client MSN Messenger, which will be replaced by Skype, but its end represents the beginning of malicious attacks posing as the installer of the software. Cybercriminals already started to use this fact in their attacks, registering malicious domains, buying sponsored links on search engines, tricking users to download and install a malware masquerade as the MSN installer.
MSN Messenger is still very popular in several countries; Microsoft informed that the service has more than 100 million users worldwide, approximately 30.5 million of them in Brazil. As an escalated migration of all users is planned, it’s getting harder to find the installer of the program and this is the window of opportunity exploited by Brazilian cybercriminals aiming to infect users looking for the software.
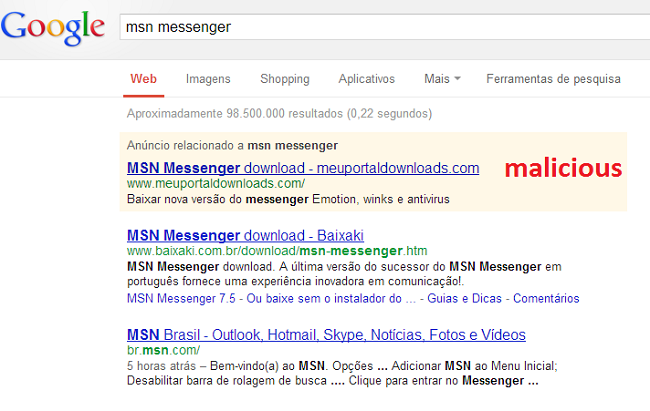
In a simple search on Google for “MSN messenger” the first result displayed is sponsored link of a malicious domain aiming to distribute the fake installer, which is actually a Trojan banker:
The domain was registered with fake data:
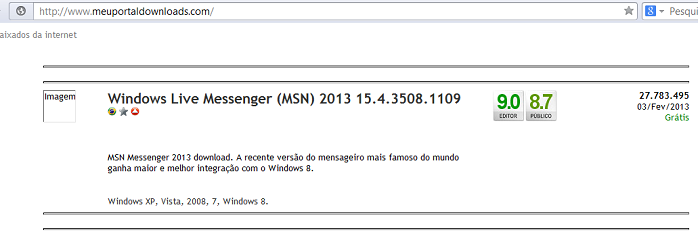
If you visit the site, this is the content displayed:
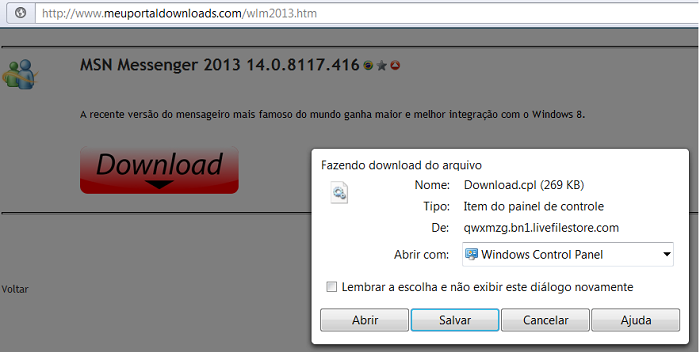
And here the download of the fake MSN installer:
Other malicious domains created with the same purpose, some of them already deactivated, are as follows:
|
1 2 3 |
baixarmsndownload.com.br downloadmsnbaixar.com.br msnmessengerlive.com.br |
We believe this is the first of several expected attacks that use the end of MSN Messenger as bait.
As we approach April 8, the day chosen by Microsoft to permanently shutdown the service (April 30th in Brazil), we advise all users to avoid looking for the MSN installer and migrate their account(s) to Skype. And the sooner the better to avoid becoming victims of attacks like this.






















The end of MSN Messenger, the beginning of attacks