The 2014 FIFA World Cup has already kicked off, at least for Brazilian bad guys. Next year’s big event in Brazil has become one of the most prominent tactics used by Latin American cybercriminals as they unleash a real avalanche of phishing messages, fraudulent prizes and giveaways, malicious domains, fake tickets, credit card cloning, banking Trojans and a lot of social engineering.
Indeed Brazil figured among the top five countries where users risk being caught ‘offside’ by phishing attacks, according to a recent study conducted by RSA and released in January. The country is in fourth place, along with the UK, USA, Canada and South Africa. So it’s no big surprise to find four Brazilian brands in the Top 10 most targeted on PhishTank stats.
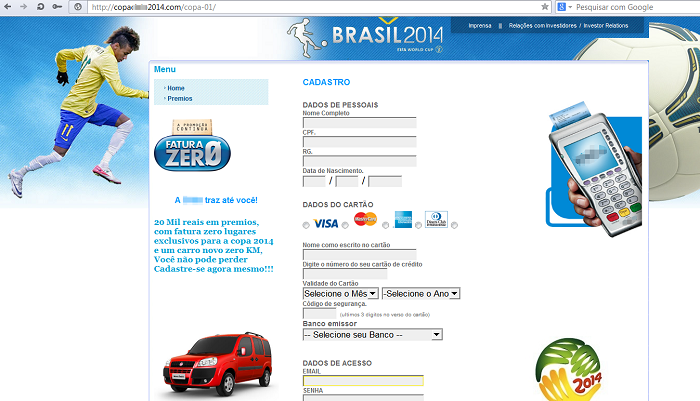
Offers range from alleged cash prizes, trips and tickets to watch the games, while the attacks involve massive phishing mailings, and, to add spurious credibility, stars of the national soccer team have been ‘signed up’ by the conmen. Here’s one example featuring Neymar, the latest Brazilian hero to be dubbed the new Pelé:

“Win a new car, cash prizes and tickets for the World Cup, just click and subscribe now”
Other messages use the image of famous TV host and actor Rodrigo Faro:

The official mascot of the event also makes the first team. Here a malicious message with Fuleco:
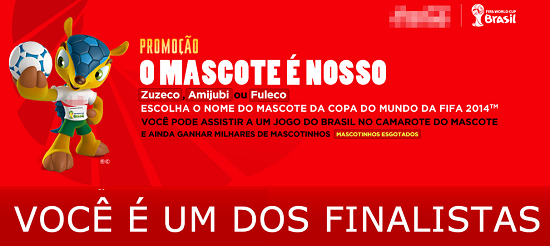
“You are a finalist to win our prize and watch Brazil’s games”
To deceive their victims, all the websites and domains used in these attacks have very professional designs. Here’s another example using Neymar’s image:
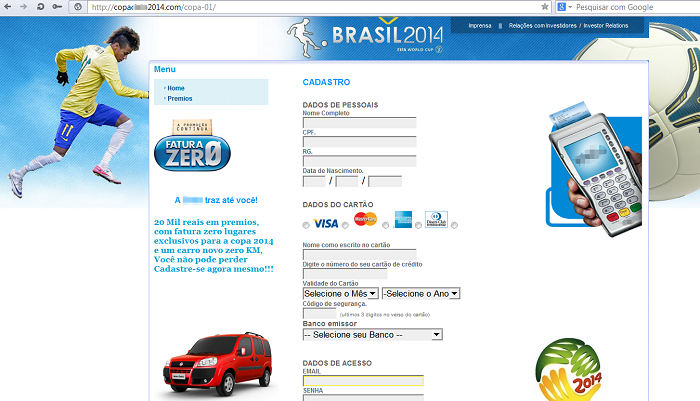
And this one, which is supposed to be a “World Cup Portal”:

These malicious websites all share a common goal – stealing credit card data. They ask for the full card number (including CVV), personal data and the CPF (the Brazilian social number). Several domains were registered recently, all of them using the words “Copa”, “Mundial” (World Cup) and “Promoção” (Giveaway). Some examples:
|
1 2 3 4 5 6 7 8 9 10 11 |
http://www.copa2014sorteios.com/ http://www.copacielo2014.com/ http://faturazerocopadomundocadastramento.com.br http://www.promocaodacopaamericabrasilfaturazro.com.br http://programacopafaturazero.com/ http://portalprogramafaturazero.com/credencie-se/ https://promocaosuperpremios.websiteseguro.com/ http://www.copa-2014cielo-brasil.com.br/ http://200.98.129.239/neymar/ http://187.109.161.24/COPA/index.php http:///www.promocaobrasil2014mundial.com.br/ |
But phishing isn’t the only game plan in use: several Trojan bankers distributed by the same bad guys are using football-inspired names to sell victims a fake and get them to open the files:
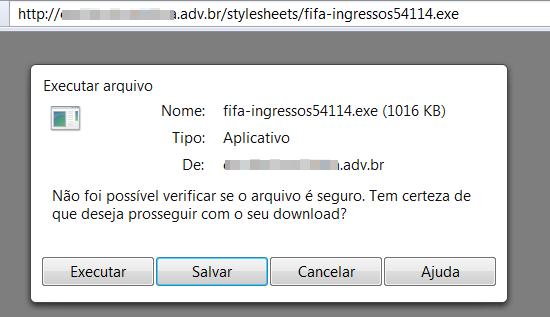
Did you open a file called “FIFA-tickets.exe”?
Even if you can’t wait for the World Cup itself, there’s a warm-up event to exploit. The Confederations Cup, which will be held next June and whose tickets are now on sale, is also spearheading cyberattacks. Neymar pops up again here, purportedly offering you a free ticket:

To marshal your defense against all these malicious websites, our anti-phishing module is trained to block any opponent – even if it comes with a picture of Neymar. And we urge all users to be ready to show these messages the red card.
For the Brazilian phishers, the World Cup has already started. But while most punters will be backing their favorite team at the bookies and hoping to make money that way, the bad guys couldn’t care less who wins the cup. They hope their ugly scams around the beautiful game will net them plenty of cash, regardless of the final score.
Update: The real tickets for World Cup matches go on sale in the 2nd half of 2013. More information here.





















The Brazilian Phishing World Cup