
If you’ve ever looked at our monthly spam reports, you’ll know that Russian spammers put quite a lot of resources into advertising their services – and the amount of e-advertising spam has increased sharply over the past few months.
What with technology evolving so rapidly, you might think it’s only the most old-fashioned spammers who send their messages themselves. Far easier – and more effective – to hire a botnet to send messages.
But the economic situation is affecting spammers just as it’s affecting everyone else; we’ve seen a few mass mailings recently like the ones shown below:
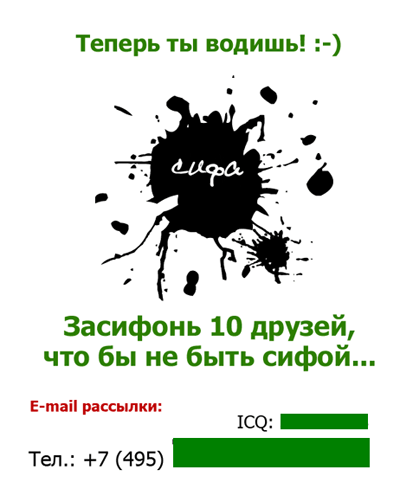
The email seems to be the high-tech equivalent of a playground game, telling the recipient “Tag, you’re it! :-)/ Tag 10 friends so you’re not it!” And it gives contact ICQ and phone numbers just in case you want to order a mass mailing.It’s one way of trying to save money – if you don’t read the message carefully, you’re going to send it on to your friends, who may send it to their friends etc.
Another similar message is the ‘Cat of Happiness’ below, which you’re told to send to five of your friends to gain prosperity. Those who aren’t into playground games, and who simply delete the message above, might be more tempted to forward this cute fluffball – all without realizing that they’re spreading spammers’ contact information.
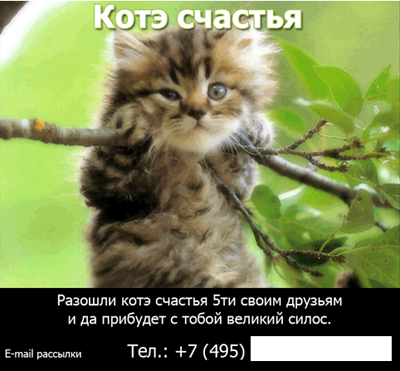
In contrast to some spam messages, the contact details aren’t hidden in any way. And although the amount of spam that can be spread like this doesn’t compare with the amount that a botnet can send, these days every little helps.






















Tag! You’re it!