
At the end of last week we came across a curious method of distributing links to a phishing page that collects users’ personal data.
The FIFA World Cup in Brazil is attracting not only football fans in all parts of the world, but cybercriminals too. The phishing page is designed to imitate the FIFA website. Visitors are asked to sign a petition in defense of Luis Alberto Suárez, a forward for the Uruguayan national team. (On June 24, in a last group stage match between Uruguay and Italy, Suarez bit Italy defender Giorgio Chiellini on the shoulder. As a result, Suarez was disqualified for nine official matches for the national team and banned from all football-related activity for four months. He was also slapped with a fine).
To sign the petition, the user needs to fill out a form, entering his or her name, country of residence, mobile phone number and email address:
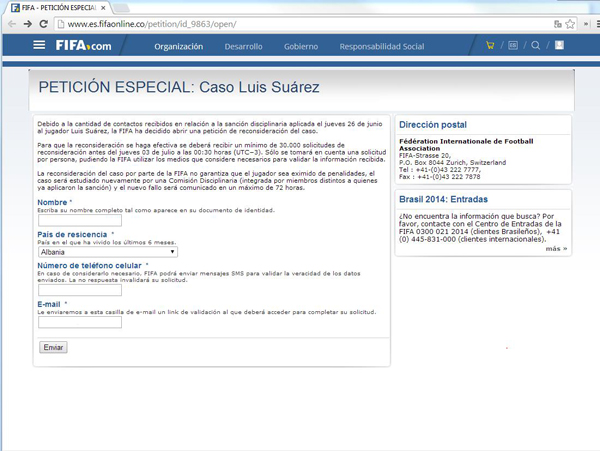
Phishing page asking football fans to sign a petition
The phishing page matches the design of the official website and all links on it redirect users to FIFA’s official site, fifa.com. The phishing domain was created on June 27, 2014. According to the whois database, it was registered in the name of a person residing in London. The data collection form was developed by the phishers using Google.Docs. Personal data obtained from the form can be used to send spam, phishing and SMS messages, as well as malicious apps. In addition, armed with users’ email addresses and telephone numbers the cybercriminals can conduct targeted attacks involving banking Trojans for computers and mobile devices. This technique is used to get round two-factor authentication in online banking systems in cases when a one-time password is sent via SMS.
After filling out the ‘petition’ form, victims were encouraged to share a link to the page with their friends on Facebook:
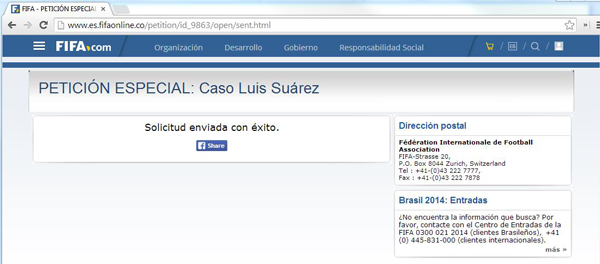
Window prompting users to share the link to the ‘petition’ with friends
Unsuspecting fans shared links to the fake petition on their Facebook pages. This enabled the phishing link to spread widely across Facebook in a matter of days.

Example of an unsuspecting user sharing a link to the phishing page on a social network
Messages with links to the phishing page were also seen on dedicated forums, from which users probably reached the phishing page originally.






















Suarez phishing ‘petition’ dupes users and their friends