
November in figures
- The amount of spam in email traffic fell by 0.6 percentage points compared to October’s figure and averaged 76.8%.
- Phishing emails accounted for 0.4% of all mail traffic, a decrease of 0.47 percentage points compared to the previous month.
- Malicious files were found in 1.6% of all emails, an increase of 0.13 percentage points compared to October’s figure.
Spam in the spotlight
Combating spam
There have been some noticeable events in the world of spam over the last few months. The Pushdo/Cutwail and Bredolab botnet command centers have been shut down; the SpamIt partner program went out of business; and a criminal case has been brought against Igor Gusev who is believed to be the world’s No.1 spammer.
Unfortunately, November was not as successful on the anti-spam front, but the events of recent months have had an impact on November’s spam trends.
Success in figures
In November, the share of spam in mail traffic fell once again. The changes may appear to be minimal (-0.6%), but this is against a backdrop of Bredolab command centers being closed over the previous two months. In the first few days following Bredolab’s closure the share of spam in mail traffic was surprisingly low and fluctuated around the 70-71% mark. If we ignore the figures for those days and compare the share of spam in mail traffic for November and October, we will find that the average for October (78.6%) would have been 1.1 percentage points higher than November’s average (77.5%).
This autumn’s downward trend is, to a large extent, the result of the global fight against botnets.
The anti-botnet campaign in the USA resulted in that country not even featuring in the Top 20 spam distributors for November – the first time it has not figured in the rating since monitoring began. In September, the Pushdo/Cutwail closure reduced the amount of spam originating from the USA from 15.5% to 6%. In October, it decreased by a factor of almost four – from 6% to 1.6%. In November, the reduction was not so considerable (-0.33 percentage points); however, it was enough for the USA to drop out of the Top 20 sources of spam.
Viagra’s banished
The situation surrounding pharmaceutical spam has been the focus of attention over the last few months. Not without reason: the closure of Spamlt and the arrest of Igor Gusev, whose name is attributed to the infamous partner program GlavMed, were notable events. It is possible that the spammers distributing pharmaceutical spam from the territory of the USA, Canada and Western Europe have realized that their activity will not go unpunished and switched to other partner programs. This is evident from the very small share of this type of spam registered throughout November.

Pharmaceutical spam in October-November 2010
As can be seen from the graph, the share of spam advertising medical-related goods was hovering around the 40% mark at the beginning of November and by the end of the month it accounted for less than a third of all spam traffic.
However, pharmaceutical spam remains a very profitable business which is why it was so widespread on the Internet until quite recently. Having lost part of their income from pharmaceutical spam, spammers are currently seeking out other opportunities to make money. This appears to be quite difficult because in October, and especially in November, there were noticeable fluctuations in the other spam categories.

Shifts in partner spam in October-November 2010
Spam advertising online casinos experienced the biggest change. In the beginning of November the share of this type of spam exceeded 30%, but by the end of the month it had dropped to just a few percentage points.
The amount of spam messages containing adverts for adult content and dating sites increased in the third week of November; at the beginning of the month they were virtually non-existent.
.РФ in spam
The first domain zone not using Roman characters recently appeared on the Internet – .рф, where “рф” is the Cyrillic abbreviation for the Russian Federation. Before registration of non-priority domain names in this zone we forecast that .рф would soon become one of the themes exploited by spammers. This has already come true.
Spam and cybersquatters
Registration of non-priority domain names in the .рф domain zone began in November, but spammers were quick to seize the opportunity, with users receiving offers to apply on 9-10 November before official registration actually started. This service was highly questionable since the early submission of an application would have violated the rules for registering in the new domain zone. In a bid to convince users, spammers touted the benefits of cybersquatting theme, i.e. the practice of buying up domain names that correspond to the names of organizations for the purpose of reselling or blackmail.
At the end of November cybersquatters appeared to be behind a major mass mailing offering recipients the chance to take part in closed bidding for the right to purchase several second level domain names in Cyrillic. Putting domain names up for sale is a typical cybersquatting technique.
Spam: links to .рф
In addition, domains with Cyrillic names have already appeared in spam messages as links to spammer sites advertising training programs, site optimization and spammer services.
Unfortunately, the lack of proper control over the content of sites in the .рф domain zone could lead to it being quickly spoiled. Of course, the links to domains in the Cyrillic zone will not be often used in messages targeting users in the USA or Europe: for users who do not know the Cyrillic alphabet the links will look like gobbledygook, which is unlikely to encourage them to visit the advertised sites.
Statistical summary
Spam in mail traffic
The amount of spam detected in mail traffic decreased by 0.6 percentage points and averaged 76.8% in November 2010. The first three days of the month were marked by a fall in spam traffic caused by the closure of the Bredolab botnet command centers. A low of 71% was recorded on 1 November with a peak of 85.6% on 7 November.
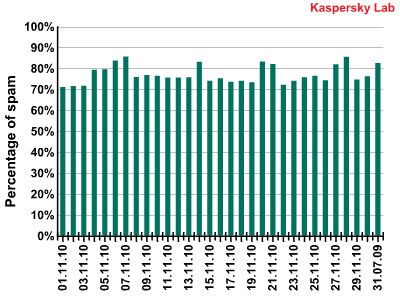
Spam in mail traffic in November 2010
Sources of spam
In November, the amount of spam originating from India increased by 2 percentage points, propelling it the top of the rating of most popular spam distributors.

Sources of spam in November 2010
Second place is occupied by another Asian country – Vietnam. The amount of spam distributed from the territory of this country increased by 5.8 percentage points. Indonesia also contributed to the quantity of “Asian” spam having doubled. However, despite this rise, Europe was still the source for a large amount of world spam (over 45%).
More spam was distributed from the UK (+1.35%) and Italy (+1%) whereas the share of Russian and Ukrainian spam decreased by 5.7 and 3 percentage points respectively. A large amount of European spam (20%) was sent from Eastern European countries.
Malware in mail traffic
In November, malicious files were found in 1.6% of all emails, a decrease of 0.13 percentage points compared with the previous month.
For the previous two months the USA was the country where most malware was detected in mail traffic, but it was replaced by Russia in November. The amount of malicious spam sent to the USA decreased by 4 percentage points while the share of emails with malicious attachments received by Russian users grew fourfold and exceeded 8%. India and Vietnam also overtook the USA: the quantity of malicious spam messages received by users in those countries doubled.
We presume the growth in the amount of malicious spam sent to the aforementioned countries is the result of attempts to create new, bigger botnets. Cybercriminals are doing this in regions where measures against cybercrime are either ineffective or not taken very seriously at the state level yet.
Developed countries such as the USA, Germany and the UK saw their positions fall considerably in the rating, while Japan dropped out of the Top 10 altogether.

Countries where mail antivirus detected malware most frequently in November 2010
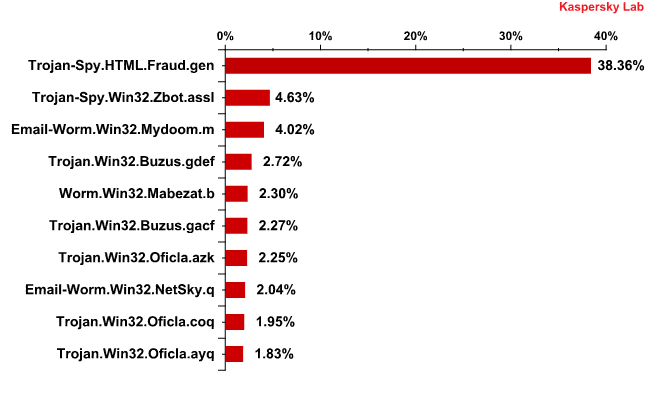
The Top 10 malicious programs distributed via mail traffic in November 2010
In November, Trojan-Spy.HTML.Fraud.gen maintained its leading position in the list of Top 10 malicious programs distributed via mail traffic. This malicious program comes with a phishing email containing a link to a fake site resembling that of a well-known bank or e-pay system where the user is asked to enter a login and a password.
Second comes Trojan-Spy.Win32.Zbot.assl. This Trojan program was designed to steal users’ credentials. In the beginning of November cybercriminals resumed Zbot distribution via mail traffic in the UK and the USA. In our October spam report we wrote that the distribution of this malicious program via email had almost ceased on the territory of these countries.
The programs from the Oficla family are still being actively distributed via email. These programs download other malicious programs and adware, or updates for them, from the Internet and launch them on the victim computer.
Less than 5% of all malicious programs found in mail traffic were new threats.
Phishing
In November, phishing emails accounted for 0.4% of all mail traffic, a decrease of 0.47 percentage points compared with the previous month.

Top 10 organizations targeted by phishing attacks in November 2010
The share of phishing attacks on PayPal decreased by 27.1 percentage points compared with the previous month. At the same time, PayPal’s nearest ‘rival’ Facebook was attacked twice as often: in October the amount of attacks on the social networking site averaged 8.4%; in November it rose to 17%. The interest shown by phishers in eBay increased threefold compared with October’s figure.
These facts as well as the growth in the number of attacks targeting organizations outside the Top 10 (+5%) lead us to believe that the focus of November’s phishing attacks was wider than the previous month. MasterCard and Visa cardholders were targeted more often in November. Attacks on Delta cardholders also resumed.
Conclusion
Despite the fact that November failed to see any notable events in the anti-spam war, the results of September’s and October’s measures were clearly seen in November’s spam traffic – both in the volume of spam and in the fluctuations of the various categories of spam.
The fight against botnets also bore fruit, with the volume of spam gradually decreasing. This is most likely a trend that will continue in the next few months. The USA, which used to be the leader in spam distribution, dropped out of the Top 20 most popular sources of spam in November thanks to measures taken by the law enforcement agencies against botnets. This resulted in cybercriminals switching to botnets located mostly in Asia and Europe. This attempt to extend zombie networks most probably caused the upsurge of malicious spam received by the users in Russia, India and Vietnam.
All the fuss about pharmaceutical partner programs led to noticeable shifts in the spam categories. Those spammers who have lost part of their income from pharmaceutical spam are trying to find other ways to make money, looking to cooperate with other partner programs.
It is difficult to say what the spammers will do in the current circumstances. Most probably, caution will give way to greed and they will start using medical-related adverts once again. However, in December they will be able to put their botnet resources to work in the run-up to the festive season, advertising holiday goods and services. In particular, partner programs that offer Christmas and the New Year presents are growing very fast.






















Spam report: November 2010