
September in figures
- The percentage of spam in email traffic grew by 2.3 percentage points from August and averaged 72.5%
- The percentage of phishing emails increased threefold compared to August and amounted to 0.03%
- In September, malicious files were found in 3.4% of all emails, a decrease of 0.5 percentage points from the previous month.
Spam in the spotlight
Fraudulent spam
There were less malicious and fraudulent mailings compared to August’s spam, though fraudulent messages were recorded that used new social engineering techniques.
Fraud with an oil and gas theme
The traditional fraudulent emails promising bogus lottery wins began exploiting the name of Russian gas giant Gazprom (sample 1). The plain text of the message congratulates the recipients on winning $920 000 and invites them to call a number to claim their prize. It’s common practice for lottery fraudsters to ask for a commission to cover the costs of a money transfer which never actually takes place. Interestingly, although it refers to a Russian company, the message is in English.
Gazprom was not the only Russian company mentioned in fraudulent spam in September. Lukoil was also deemed attractive enough by the fraudsters to use as bait, with a typical message offering remote, well-paid work for Lukoil. No doubt, the company’s name was used to make the offer sound more realistic. However, the name of the major oil company was merely a screen. The spammers were really aiming to embroil users in illegal money-making schemes, often without their knowledge. The ‘work’ usually involves money transfers from the “employers” to users’ accounts and on to the accounts of third parties. Users are generally led to believe that these are Internet store transactions, when in fact they are aiding the transfer of cash from stolen or compromised bank cards.
Interestingly, both emails had the domain mail.com in the “From” field which suggests that the source of the mailings may have been the same. It also suggests that the spammer is from the former Soviet Union because in both messages he used the names of Russian companies.
As a rule, spammers like to mask their emails with famous brands or names in order to get the best possible response to their mailings. However, this kind of name-dropping does not make the spam message less dangerous.
Michelle Obama vs. Asma al-Assad
Illustration 4 confirms once again that spammers will also exploit the names and reputations of famous people to achieve their fraudulent aims. This email was supposedly written on behalf of Michelle Obama, the US President’s wife, who notified the recipient of a payment from the White House Fund.
This run-of-the-mill ‘lottery’ email attracted our attention due to use of Michelle Obama’s name. It is interesting to see how spammers gauge public opinion about different high-profile figures. For example, from early April spam traffic has included emails from Asma al-Assad, the wife of the Syrian leader Bashar al-Assad. However, in this case users were offered incredible sums of money which had to be urgently stashed abroad. The spammers understand that it would be strange to assume a family member of the US President was trying to smuggle away suspicious money, but the payments from a fund administered by the first lady would not surprise anyone. As for the wife of the Syrian President, users might suspect a trap if they are offered charity from the embattled regime, but would be unsurprised by plots to flee with stolen money.
The message itself has a very impressive sender: World Wide Web Owner. Yes, that mythical being, the owner of the entire Internet, is sending us emails, and from a .ru mailbox domain. The email explains that this owner is writing on behalf of Michelle Obama. ‘Michelle’s’ mailbox in the Sender field is also noticeable: first of all, it begins with the name ‘missnadia’ which can be expanded to Miss Nadia. It is hard to imagine that Michelle Obama would have such a strange nickname for her mailbox. It is also difficult to explain why this mailbox is registered on Yahoo in China. And surely, just about everyone would find it incredible that the first lady of the USA would send official emails from such an unlikely email address.
The coupon story continues
As expected, coupons are becoming even more popular with cybercriminals. In September, we recorded mass mailings containing links to infected coupon sites (sample 5). The messages were a good imitation of legitimate Groupon mailings. The only weak point was the ‘sender’ field, which had nothing to do with the coupon service.
Holidays are coming…already?
Christmas-related mailings traditionally begin in October. The first emails are usually in English, German and other European languages. However, this year we saw an exception to this rule. In September, we received our first New Year mailing and it was in Russian. The message, sent from an address in Kiev, contained an invitation to a children’s New Year party in Moscow.
Hot spam topics
In September, the film ‘The Innocence of Muslims’ on YouTube gave rise to intense controversy. The film even led to the closure of YouTube in some regions of Russia.
The film itself was actively distributed, including via spam mailings. We expected to see links to infected sites masked as a link to the film. Oddly enough, contrary to our expectations there was no malicious code or dangerous link in the registered mass mailings.
It should also be noted that all the emails were in English.
Statistical summary
Sources of spam by country
Below are the Top 20 ratings for the countries that sent most spam to Europe in September.
Top 20 sources of spam sent to European users in September 2012
August’s second and third biggest distributors of spam to European users switched places in September – the USA moved up one place (+1.8 percentage points), while India dropped to third place (-1.1 percentage points). South Korea and Vietnam also lost ground: last month they were among the top six spam senders; however, in September they dropped to 12th and 14th places respectively. The most significant increases in spam distribution came from Spain (+2.9 percentage points) and the UK (+1.8 percentage points).
In terms of worldwide spam distribution, China maintained its lead with 26.4% of all distributed spam. It is followed by the USA (12.5%) and India (10.1%).
Top 20 sources of spam in terms of worldwide spam distribution in September 2012
Unlike Europe, the worldwide spam top 10 included both Vietnam and South Korea. In general, distribution between spam sources is more evenly spread in the worldwide table, although China remains the clear leader in both ratings.
Malware in mail traffic
In September, malicious files were found in 3.4% of all emails, a decrease of 0.5 percentage points compared to the previous month.
Distribution of email antivirus detections by country
Distribution of email antivirus detections by country, September 2012
September saw big changes in the patterns of email antivirus detections. The USA, which had topped the rating for eight months in a row, unexpectedly dropped to eighth place: the share of Kaspersky Mail Antivirus detections in the country decreased by 6.9 percentage points compared to August. At the same time Germany saw growth of 6 percentage points in the number of its antivirus detections, rocketing it into the lead. Spain, which came second in September’s rating, increased its contribution by more than 4 percentage points. Russia occupied 3rd place with the considerable increase of 5.4 percentage points in the number of email antivirus detections. In India the share of Kaspersky Mail Antivirus detections grew by nearly 2 percentage points while in the UK it dropped.
The other countries fluctuated within a range of 1.5 percentage points compared to August.
Top 10 malicious programs spread via email in September 2012
Top 10 malicious programs spread via email in September 2012
In September, the long-term leader Trojan-Spy.HTML.Fraud.gen finally left its pedestal, dropping so drastically that it even fell from the Top 10 most popular malicious programs spread via email.
Top spot was taken by Backdoor.Win32.Androm.kv. The Top 10 also included another program from this family – the Androm.ib modification was in sixth place. Malicious programs from this family also made the Top 10 in June, and have remained popular throughout the summer. These programs, once installed on a user’s computer, start downloading other malicious programs including spam bots.
Email-Worm.Win32.Bagle.gt, Email-Worm.Mydoom.m and Mydoom.l came second, third and fourth respectively. To recap, the latter two mail worms have only two functions – to harvest email addresses and send copies of themselves to those addresses. Only Bagle.gt has extra functionality enabling it to download other malicious programs.
Four programs in this rating belong to the Trojan-Ransom family. Win32.PornoAsset is ransomware which blocks the operating system and demands payment to unblock it. It should be kept in mind, however, that even after the ‘ransom’ is paid the system will not be unblocked: this is why the user should not be conned by spammers. It is better to ask for specialist help. They will explain how to re-enable the system.
Phishing
The percentage of phishing emails increased threefold compared with August and amounted to 0.03%.
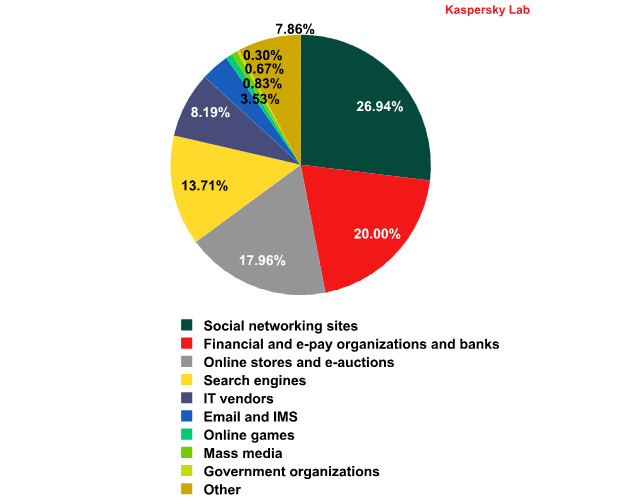
Top 100 organizations, by sphere of activity, targeted by phishers in September 2012
(based on anti-phishing component detections*)
*This rating is based on our anti-phishing component detections activated every time a user attempts to click on a phishing link, regardless of whether the link is in a spam email or on a web page.
Contrary to our expectation the amount of attacks on social networking sites did not decrease in September. This category was still popular with the phishers and the share of attacks on it grew, albeit by just 0.1 percentage points. Financial organizations were attacked less often (-3.6 percentage points) – also not in line with our forecasts. Most likely, this decrease was caused partly by the efforts of banks and financial organizations to protect their clients and introduce additional protection and authorization technologies.
Spam by category
Spam by category in September 2012
In September, the share of the personal finance category shed a further 20 percentage points, dropping to second place overall. Most emails in this sector contain offers of dubious money-making schemes.
Topping the list in September were fraudulent emails whose share increased by 36 percentage points. At the same time the contribution of pharmaceutical spam dropped by 14 percentage points.
Conclusion
In September, as forecast, the number of malicious and fraudulent mass mailings in spam traffic decreased with the end of the holiday season, while business activity started to grow and spammers received more orders from small and medium-size businesses. Malicious files were found in 3.4% of all emails, a drop of 0.5 percentage points from the previous month. At the same time, spam traffic was recorded containing fraudulent mailings that made use of new social engineering techniques.
In September, we registered the first New Year related mass mailing. Generally, they appear in October but this year seems to be an exception. In the coming months the share of such emails will grow and Christmas and New Year offers will become more varied.
September saw considerable shifts in the rating of email antivirus detections. The USA, which had topped the rating for the eight months in a row, experienced an unexpected and rather sharp fall: the share of Kaspersky Mail Anti-Virus detections in the country decreased by 6.9 percentage points compared to August. There were significant changes in the programs most often detected by mail antivirus: the long-term leader Trojan-Spy.HTML.Fraud.gen was not only replaced at the top but completely dropped out of the Top 10 most popular malicious programs spread via email.
In September, the distribution of phishing attacks by category produced some surprises: the share of attacks on social networking sites did not show any sign of decreasing while financial organizations were attacked less often. This is at least partly due to increased efforts by banks and financial organizations to introduce enhanced protection and authorization technologies for their clients. However, this decline could well be short-lived, since successful phishing attacks on bank accounts are the most lucrative source of revenue for cybercriminals.





























Spam in September 2012