
- October in figures
- Spam in the spotlight
- The geographical distribution of spam sources
- Malware in mail traffic
- Phishing
- Conclusion
October in figures
- The percentage of spam in email traffic was down 4.5 percentage points from September and averaged 68%.
- The percentage of phishing emails remained unchanged from September and amounted to 0.03%.
- In October, malicious files were found in 3.25% of all emails, a decrease of 0.15 percentage points.
Spam in the spotlight
Malicious attachments. The story continues
The percentage of spam continues to decrease but the proportion of emails with malicious attachments and links to malicious resources remains quite high. Junk traffic also includes many fraudulent messages.
In October, spammers continued to use a wide range of tricks to distribute malicious zip files. This month they spread emails imitating official notifications of speeding fines as well as fake hotel reservations and offers of fake airline e-tickets which we have seen in previous mass mailings.
In October, fraudsters introduced a new variation on the fake hotel booking theme. Earlier they sent English-language messages, allegedly from booking.com. Now fake emails in English and German have started imitating notifications from the online booking service hotel.de. The email, which contains an attachment with a malicious zip archive, asks the user to confirm a booking at the 5-star Brenner’s Park-Hotel & Spa in Baden-Baden. The .exe file enclosed in the archive is detected by Kaspersky Lab as Trojan-Ransom.Win32.Gimemo.atjk.
In addition to fake notifications, spammers tried to add a personal touch to infiltrate computers. For example, they spread fake wedding invitations which contained a malicious attachment.
Political spam
This autumn the whole world was awaiting the outcome of the US Presidential Election. In the run-up to Election Day, at the height of the campaign, spammers invited users to share their views on who would win – and claim a free $250 Visa gift card.
Any email address that is entered, however, is destined to end up in spammer databases and will most likely find itself on the receiving end of even more junk mail.
We also registered other mass mailings related to the election theme. Among them were calls to support one of the candidates and the notorious adverts for a watch “like the President’s”.
The election was also used to lure people onto various sites.
Clicking the link in the email above led users to a fraudulent site where they were shown a video about making allegedly easy money on the Internet. Of course, the video had nothing to do with Obama.
Holiday-themed spam
Halloween, which is widely celebrated in Europe and the USA, also attracted plenty of attention from spammers. English-language emails offered lots of holiday-related goodies such as designer bags, door mats, photo frames and fluorescent T-shirts.
The holiday theme was actively exploited to advertise various offers and discounts. This time, in honor of Halloween, spammers offered new and used discount cars from manufacturers. Jack-o’-Lanterns and bats conveyed the holiday theme in these adverts.
As is usually the case in October spammers started reminding people about the coming winter holidays. We’ve already registered lots of Christmas and New Year-related mailings offering candies, gifts, tickets for New Year excursions, and much more.
New Year spam advertises market-specific goods. For example, emails in Russian offered decorative miniature handmade felt boots – valenki – which are fixed to surfaces with the help of a magnet or a hook.
Russian users were also offered made-to-order artificial indoor and outdoor Christmas trees while English-speaking users were offered the chance to buy a tin and grow a Christmas tree at home by just following some easy instructions.
The geographical distribution of spam sources
As was the case in the previous month, China (30.7%) and the USA (27.3%) topped the rating of the most active spam distributors in October. These two countries contributed almost 58% of the world’s junk email flow. The Top 5 also includes India (5.8%), Vietnam (4.3%) and Brazil (2.6%), which have long attracted spammers with their poor antivirus protection.
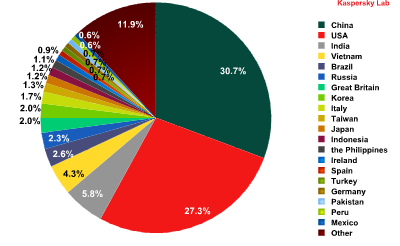
Sources of spam in October 2012
China is even more prolific in terms of sending spam to European users, with a 53.3% return representing an 11.8 percentage point increase on September’s figure. The USA came second with 13.4% (+2.7 percentage points). Italy increased its contribution to European spam flows by 3.9 percentage points to move up to third place. At the same time India’s share declined considerably (-6 percentage points).
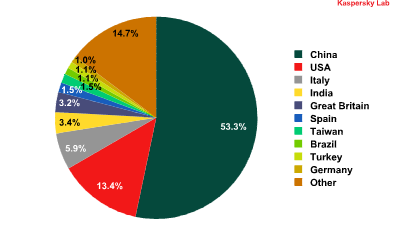
Top 10 sources of spam sent to European users in October 2012
Malware in mail traffic
In October, malicious files were found in 3.25% of all emails, a decrease of 0.15 percentage points compared to the previous month.
Distribution of email antivirus detections by country
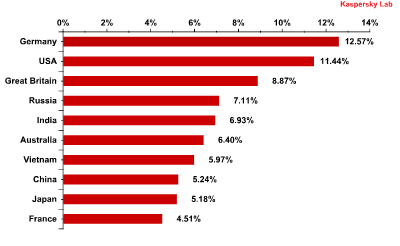
Distribution of email antivirus detections by country
For the second month running there were significant changes in the levels of Kaspersky Mail Antivirus detections. Germany remained on top, despite a fall of 1.25 percentage points compared to September. However, there were significant shifts lower down the list. The USA returned to the Top 10 (+5.82 percentage points) just behind Germany. The UK also regained third place having increased its contribution by 4.2 percentage points from the previous month. Spain, which was second in September’s rating, dropped out of the Top 10 altogether with a dramatic decline of 3.94 percentage points. Russia moved down to 4th position though its share remained practically unchanged (+0.26 percentage points).
Top 10 malicious programs spread via email in October 2012
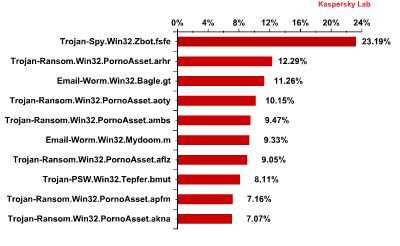
Top 10 malicious programs spread via email in October 2012
In October, Trojan-Spy.Win32.Zbot.fsfe, a modification of the well-known spyware ZueS/Zbot designed to steal users’ credentials for different e-payment services, was the most popular malicious program being spread in email traffic. Zbot is a universal Trojan program targeting the accounts of numerous banks. The virus writers behind it are constantly improving the code and this particular variant had a different packing method.
Although Zbot has not appeared in the TOP 10 malicious programs spread via email for a long time, cybercriminals haven’t forgotten about it. We often see malicious spam which contains a link to a malicious resource rather than an attachment. If the exploits located on this resource manage to find a software-based vulnerability on the user’s computer, they download and run the executable malicious file which in turn downloads a member of the Zbot family onto the infected machine.
Six programs in October’s chart belong to the Trojan-Ransom.Win32.PornoAsset family, which represented 55.2% of all malicious programs spread via email. Trojan-Ransom.Win32.PornoAsset is ransomware which blocks the operating system and demands payment before unblocking it. The first four representatives of this family appeared in the Top 10 in September. We have already warned the victims of PornoAsset that their systems will not be unblocked even if the “ransom” is paid. In case of infection it makes sense to ask for specialist help rather than hand over any money.
Neither Backdoor.Win32.Androm.kv, last month’s leader, nor Trojan-Spy.HTML.Fraud.gen, the previous leader, feature in October’s Top 10. Both Trojan-Spy.HTML.Fraud.gen and Trojan-Spy.Win32.Zbot.fsfe target the same things – online banking and e-payment systems. It seems that the fraudsters are rotating their “tools” in a bid to get at users’ money.
Phishing
The percentage of phishing emails remained unchanged compared with September and amounted to 0.03%.
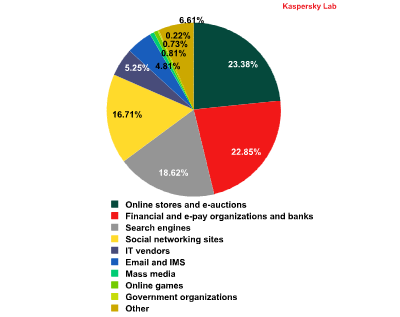
Top 100 organizations, by sphere of activity, targeted by phishers in October 2012 (based on anti-phishing component detections*)
This rating is based on our anti-phishing component detections activated every time a user attempts to click on a phishing link, regardless of whether the link is in a spam email or on a web page.
After the summer lull, October saw considerable growth in the number of attacks on financial organizations (+2.85 percentage points) and online stores and e-auctions (+5.42 percentage points). If the attacks are successful, the fraudsters behind them can get access to users’ online banking and e-payment accounts and steal their money.
The amount of attacks on social networking sites decreased by 10.23 percentage points in October, which meant this category fell from first place to fourth, behind even the Search engines category. We expected this drop to occur earlier, in September. The fact is that in summer phishers mostly attack schoolchildren and students who spend lots of time surfing the Internet during their holidays. As business activity starts to resume at the end of summer, fraudsters return their attention to financial organizations.
Conclusion
As expected, the presidential election in the USA attracted a lot of spammer attention. It is unlikely that after the election Obama’s name will appear so often in spam. In order to lure users to a malicious site or to extort money from them, the spammers will no doubt find other hot topics, such as the hurricane in New York.
Overall, most of the world’s spam is sent from the USA and China. Several years ago these countries topped the rating of the sources of spam. Now their share is once again increasing as the large number of Internet users in those countries create favorable conditions for spam distribution from infected machines.
October saw more malicious and phishing emails targeting users’ money. This will probably continue in future. Users should be especially watchful making e-payments and entering confidential data on the Internet. Do not click links in spam emails and do not open attachments from unknown senders. Apply software updates as soon as they appear.




























Spam in October 2012