
Technical Tactics
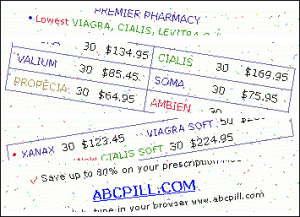
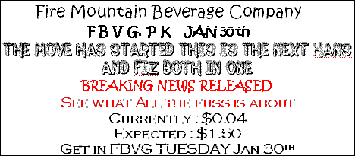
Spammers once again made several attempts to modernize the technology used in creating graphical attachments in spam emails (“image spam”) during the first six months of 2007. For example, in February 2007, renewed attempts were made to use with animated graphics, which spammers had all but abandoned by the end of November 2006. This new type of animation differs from the previous type in that the source image is broken into fragments, and each fragment is skewed at a different angle. As a result, the user will see something like this:
Below are two separate animated frames from the very same spam mailing:
Spammers tried their hand at other approaches as well, such as using a variety of rare fonts:
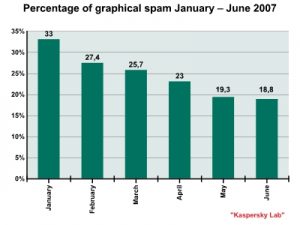
Nevertheless, these attempts were not very successful and the share of spam with graphical attachments (.gif, .jpeg, etc) began to decrease. In January, the share of graphical spam amounted to 33% of all spam, but in March numbers were down to 25.7%. The decline continued with graphical spam registering a mere 18.8% of all spam in June:
The main reason behind the decline of graphical spam is that it has become less and less effective. A number of manufacturers are now producing spam filters which do a decent job detecting graphical file attachments and blocking graphical spam. All the same, spammers aren’t going to abandon graphical spam completely. This is why they are searching for new ways of delivering graphical files to end users, in addition to .gif and .jpeg formats. The first half of 2007 saw several new techniques for delivering and showing spam graphics to end users:
- Placing graphical files on free hosting websites (such as imageshack.us, imagenerd.com, imgnation.net, hostpic.biz, imgplace.com, etc.). The text of these spam emails includes a link to an address that hosts an image. When a user opens the email, most popular email clients will automatically download the image from the URL.
- Using graphics as a background image. Graphics files are not included in the email, but are instead – again – published on a separate website. The message text only contains a URL inside a ‘body’ tag with the attribute ‘background’. As a result, the image may be automatically downloaded by some mail clients, as well as by the web interface of some mail services.
- Spam in PDF attachments. This kind of attachment will not open automatically, nor will it be downloaded automatically. In order to see the spam content, a user has to open the attachment manually.
- Spam in FDF attachments. In some ways this is the same as using PDF attachments, especially since users are only able to open and view the attachment using Adobe Acrobat Reader.
In the first two cases, spammers make sure the spam image was not visible in the body of the message. Using these approaches ensures there is nothing for spam filters to analyze.
In the third case, the image is attached, but the format of the attachment was such that many filtration systems ignore it. As a result, a full analysis of spam content is not carried out.
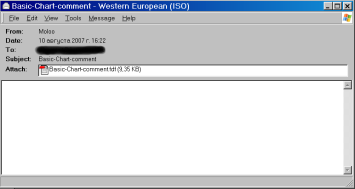
When they first appear, these new developments tend to be quite effective. However several months (or sometimes just weeks) down the road, spam filters will be reconfigured to counter new spammer tactics. But even new spammer tricks usually do not pose any kind of challenge to more advanced filters. For example, Kaspersky Anti-Spam is capable of combating spam in PDF and FDF attachments and of countering new kinds of spam without the need to make changes to the software:
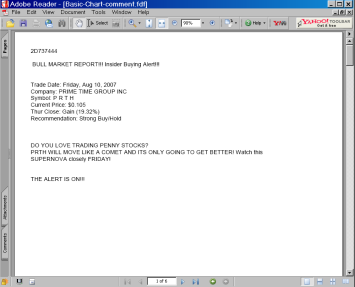
Below is one example of PDF spam:
Here is the spam email (the message is empty and there is no text) …
…and here is what’s in the attachment:
Spam by category
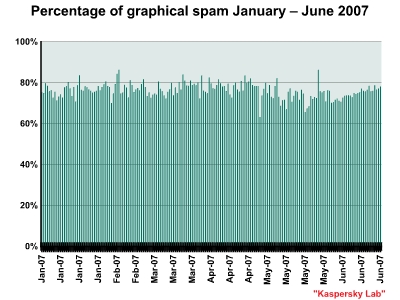
During the first six months of 2007, spam levels remained within the usual range of 70% – 80% of all mail traffic. The reason for the high level of stability lies with the changing nature of spam. More and more spam is becoming criminalized and is slowly moving away from traditional advertising. Criminal spam is not subject to the laws governing the advertising market and is not very susceptible to fluctuations linked to seasonal supply and demand.
The six-month low reached 62.9% and was recorded by Kaspersky Lab on 27th April. The six-month high was 86%, recorded on 11th February and on 28th May.
The shares of the leading spam categories in the first half of the year are:
- Medications: health-related goods and services (17.3% of all spam).
- Education (13.8%)
- Computers and the Internet (9.2%)
- Computer fraud (8.9%)
- Electronic advertising services (8.3%)
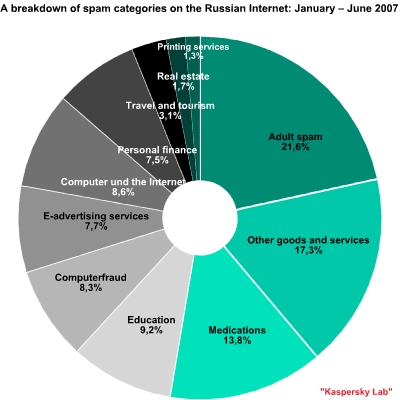
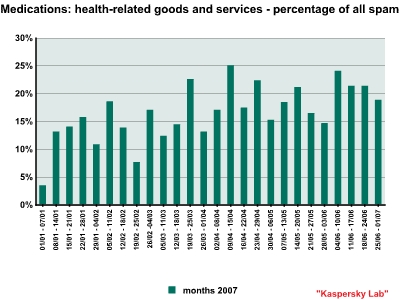
The medications: health-related goods and services category remains at the top. Most of this category of spam consists of English-language advertising for inexpensive medications (Viagra, Cialis, etc.). In addition to the regular English-language offers for Viagra and antidepressants, spam in this category now also includes some Russian-language offers for health-related goods and services, such as massaging glasses, self-help books on how to quit smoking, and gym memberships.
This category of spam has been rising steadily since the start of the year and nearly doubled over the first six months of 2007, rising from 11.5% in January to 21.4% in June:
The education category took second place. This category primarily consists of Russian-language offers for training courses and seminars, as well as English-language messages offering a variety of academic qualification. This category represents 13.8% of all spam.
The computers and the Internet category ended up in third place. This category is mostly made up of English-language offers for unlicensed software.
Two other categories are almost neck and neck: computer fraud (8.6%) and electronic advertising services (8.3%). As usual, electronic advertising services accounted for a relatively large share of all spam, an indication that spammers are continuing to search for new clients.
The personal finance category has dropped steadily over the first six months of 2007. In January this category was in first place and represented 13.3% of all spam, but in February this year financial spam was squeezed out of first place by the medications category.
In June the percentage of personal finance spam fell to 3.7%. The record low for this category was recorded at 1.1% of all spam during the first ten days of June.
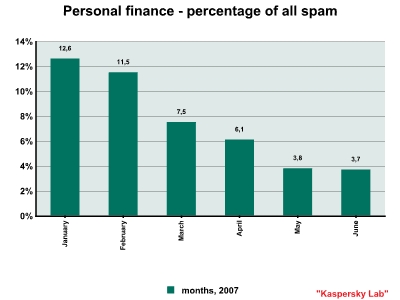
This decline took place for a number of reasons:
- demand was saturated – even gullible Internet users lost interest in this type of spam and stopped responding to it
- spam filters were reconfigured to recognize financial spam
- in the first quarter of 2007, US and Canadian authorities expressed concern about financial spam and promised to protect investors from this threat; this will no doubt put spammers under a certain amount of pressure.
Are Phishers Testing the Waters of the Russian Internet?
In the first half of 2007, there were several phishing attempts targeting services primarily intended for users of the Russian Internet.
A phishing attempt against a Russian bank was recorded in the first quarter of this year. This is a rarity, since phishers tend to target Western banks with developed online banking systems and a large number of clients using these systems. The target of this attack, which took place around February 20th 2007, was Alfa Bank. The phishers used a classic tactic: the spam sent – allegedly on behalf of Alfa Bank – was disguised as an email from the bank’s administration and contained a link to a phishing website disguised as Alfa Bank’s official website. The counterfeit website used the same style, bank details, text and other features of the real Alfa Bank website. The fake website asked users to enter their account login and password in a web form and this data was subsequently sent to the phishers.
In May, a series of attacks on the Yandex.Dengi electronic payment system were detected. These attacks were typical: the spammers tried to persuade users to enter their personal data on a phishing site in order to obtain access to payment system accounts.
In both incidents, the users who didn’t suspect anything fishy took some major risks with their money, and possibly even lost some of it.
Attempts to attack Russian companies are still quite rare. In this case, it was probably a kind of reconnaissance, i.e. phishers were trying to work out if Russian Internet users would make good potential victims and just how popular online money services are among this demographic. The attacks did not continue immediately, probably because the phishers were not satisfied with their catch. However, there’s no reason to believe phishing attacks against Russian online services are over for good. After some time has passed, phishers are likely to cast their nets again.
Spammers are expected to experiment more with new graphical technologies in the second half of 2007. Spammers are also looking into and testing other technologies. We may see a return to “the good old days” with attempts to breathe new life into older tactics and technologies.
There is no reason to expect any serious threat from spam with PDF or FDF attachments, as this kind of spam is already headed for a decline, which will continue over time.
Spammers have already found ways to apply some minimal targeting for their mass mailings. This is especially true for all kinds of phishing attacks (such as the attack against Alfa Bank sent to Russian Internet users which demonstrated a kind of geo-targeting) and computer fraud. Some spam mailings may turn into targeted attacks (i.e. mailings aimed at a specific social, geographical, age, or language demographic.). However, this is a more time-consuming stage in the evolution of spam.
The share of spam in total email traffic won’t change radically over the next six months. The leading spam categories indicated above are likely to remain in the top five.
Overview
- New tactics in spam: spam sent as a background image within a mail, and spam using PDF and FDF files as attachments.
- The six-month low reached 62.9% and was recorded on 27th April. The six-month high was 86%, recorded on 11th February and on 28th May.
- Most spam consists of advertisements for Viagra and other medications (17.3% of all spam).
- Phishers are showing interest in the Russian Internet – there have been phishing attacks against Alfa Bank and Yandex.Dengi.
























Spam Evolution: January – June 2007