
Social networks are one of the hottest things on the Internet at the moment, so it’s not surprising that spammers and malware writers love them.
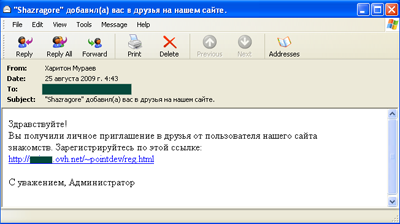
And a recent spam message confirms just how sexy they are! Lots of Russians have found this in their inbox:
The mail looks like an invite to join a social networking site – the sender has allegedly added you to his list of friends. The message comes complete with a link where you can register. If you’re not up on security issues, you might well click on the link – sure, you don’t know who sent the message, but the Internet is a great way to meet new people.
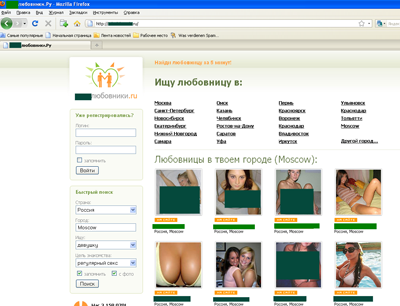
Click – and you end up here, on a site which is designed as a clone of the Russian Odnoklassniki, the equivalent of Classmates or Friends Reunited. Except that the content is rather more adult – if you’re lost in cyberspace without a lover, you can use this site to find a lover/ partner/ one-night stand.
The pictures are pretty enticing, so why not register? The site promises it only takes 5 minutes, and once you’ve filled in your details, you just have to send an SMS to a short number to get an activation code.
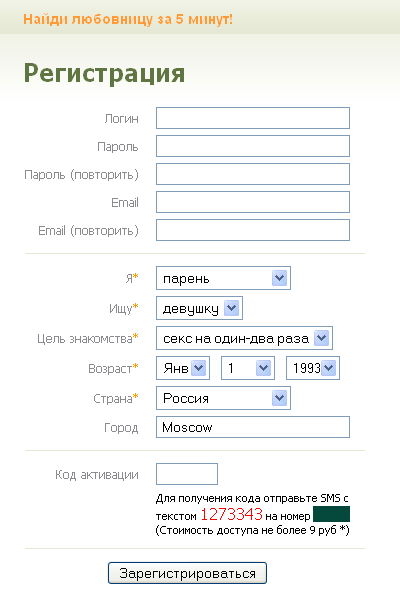
Whether or not the men and girls pictured here are genuine, we can’t say. They might be. But the site’s been set up to make money in an underhand way – send the SMS to get your activation code, and you’ll get a nasty shock: you’ll be charged not 9 roubles (around 30c), as promised on the registration form, but around 300 roubles ($10 or so).
We’ve seen quite a bit of malware which makes money by getting infected devices to send SMS messages to short numbers. This scam is a bit different. Maybe $10 isn’t that much to pay for sex, but when the price you see isn’t the price you actually pay, you have to wonder what else isn’t quite what it seems.





















Social networking is sexy!