
This weekend we monitored three attacks of Brazilian cybercriminals on Twitter, all with the same goal: spreading malware bankers using Direct Messages and compromised accounts, targeting Brazilian users.
This can be considered new in Brazil especially because around 90% of all Brazilian malware are spread through e-mail, using spam techniques and many social engineering tricks. The malicious scheme started when users receive a direct message from another user:
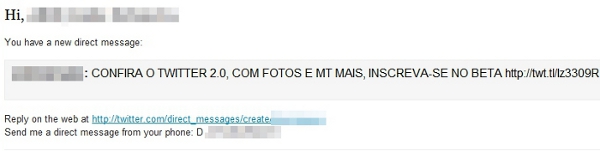
“Check out Twitter 2.0 with pictures and more, sign up now in the Beta”
The direct message is sent automatically by a user who has had his account compromised or his login stolen. These notifications of direct messages use the twt.tl service, a shortener URL of Twitter. The malicious scheme uses a lot of redirections to finally arrive at a .com providing an executable file, a banker Trojan:

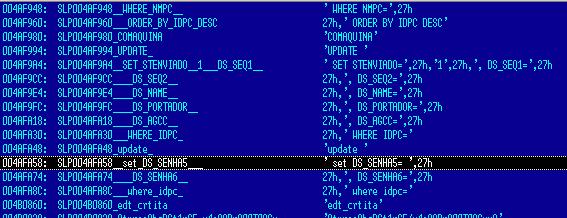
If executed, the malware creates a file called hash.dll in the folder C:WindowsHASH and register a BHO in the browser with random CLSID. This DLL has a really low rate of detection. After it is activated, the Trojan banker monitors all the user’s connections and steals credentials of Internet banking services of Brazilian banks.
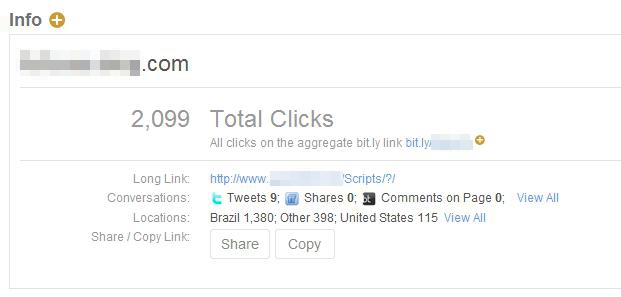
What’s more interesting in this attack was the quick spread. In less than one hour the malicious link used on the message was visited more than 2,000 times, almost all by Brazilian users:
This malware is detected by Kaspersky as Trojan-Downloader.Win32.Homa.cgc.






















Social disaster and trojan bankers on the rise