
With the spread of COVID-19, organizations worldwide have introduced remote working, which is having a direct impact on cybersecurity and the threat landscape.
Alongside the higher volume of corporate traffic, the use of third-party services for data exchange, and employees working on home computers (and potentially insecure Wi-Fi networks), another headache for infosec teams is the increased number of people using remote-access tools.
One of the most popular application-level protocols for accessing Windows workstations or servers is Microsoft’s proprietary protocol — RDP. The lockdown has seen the appearance of a great many computers and servers able to be connected remotely, and right now we are witnessing an increase in cybercriminal activity with a view to exploiting the situation to attack corporate resources that have now been made available (sometimes in a hurry) to remote workers.
Since the beginning of March, the number of Bruteforce.Generic.RDP attacks has rocketed across almost the entire planet:
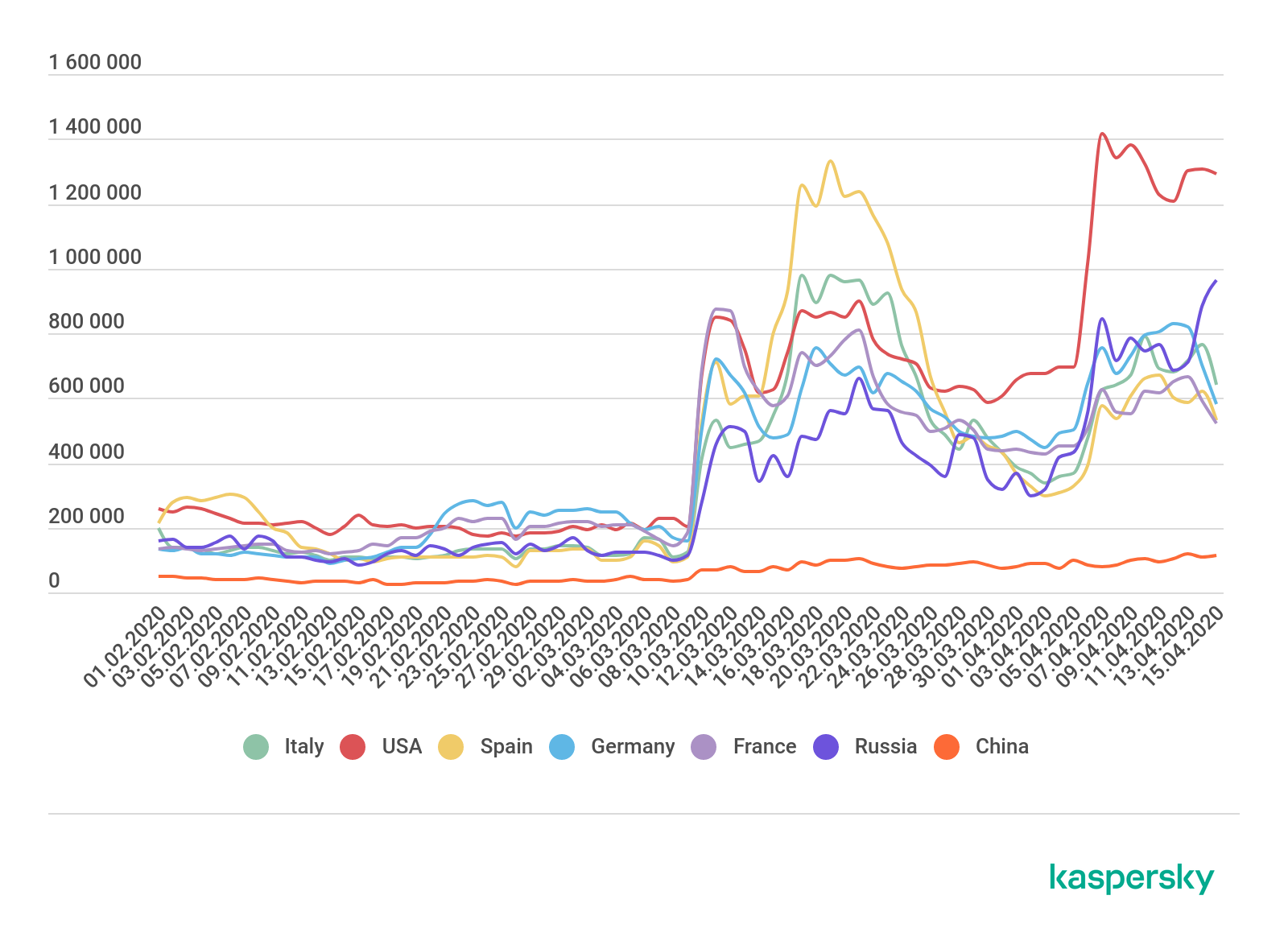
Growth in the number of attacks by the Bruteforce.Generic.RDP family, February–April 2019 (download)
Attacks of this type are attempts to brute-force a username and password for RDP by systematically trying all possible options until the correct one is found. The search can be based on combinations of random characters or a dictionary of popular or compromised passwords. A successful attack gives the cybercriminal remote access to the target computer in the network.
Brute-force attackers are not surgical in their approach, but operate by area. As far as we can tell, following the mass transition to home working, they logically concluded that the number of poorly configured RDP servers would increase, hence the rise in the number of attacks.
Attacks on remote-access infrastructure (as well as collaboration tools) are unlikely to stop any time soon. So if you use RDP in your work, be sure to take all possible protection measures:
- At the very least, use strong passwords.
- Make RDP available only through a corporate VPN.
- Use Network Level Authentication (NLA).
- If possible, enable two-factor authentication.
- If you don’t use RDP, disable it and close port 3389.
- Use a reliable security solution.
If you use a different remote-access protocol, you still cannot relax: at the end of last year, Kaspersky experts found 37 vulnerabilities in various clients that connected via the VNC protocol, which, like RDP, is used for remote access.
Companies need to closely monitor programs in use and update them on all corporate devices in a timely manner. This is no easy task for many companies at present, because the hasty transition to remote working has forced many to allow employees to work with or connect to company resources from their home computers, which often fall short of corporate cybersecurity standards. Our advice is as follows:
- Give employees training in the basics of digital security.
- Use different strong passwords to access different corporate resources.
- Update all software on employee devices to the latest version.
- Where possible, use encryption on devices used for work purposes.
- Make backup copies of critical data.
- Install security solutions on all employee devices, as well as solutions for tracking equipment in case of loss.
Remote spring: the rise of RDP bruteforce attacks




















Fabio Bertinelli
This article is very interesting, especially the graph depicting the increase in brute force attacks. Is it possible to view a more recent scenario?