
Yesterday, I blogged about the older version of Adobe Flash Player on my recently purchased Google Chromebook. On Tuesday, the day before, I’d sent out a note to Adobe’s PSIRT asking if they knew what was up with this earlier version.
Today, Adobe got back to me today saying that Flash Player version 10.2.158.27 is the latest version of Flash for Chromebooks. This patch was pushed out yesterday after my blog post went live. (You may notice my screenshot shows 10.2.158.26)
Currently we don’t know what’s fixed with the latest build. Some sources are claiming at version 10.2.158.26 already contained all the security fixes. We’re waiting for final confirmation from Adobe on this matter.
This brings us to another question though – Why is ChromeOS being updated in the Flash 10.2 branch? Going by Adobe’s own documentation 10.2.x.x should still contain certain unpatched vulnerabilities.
The answer is Pepper. Chrome Flash Player Pepper is a custom version of Flash which is the default Flash renderer in ChromeOS. As far as I can tell, Google is only using Pepper Flash with Chromebooks but there’s not a whole lot of publicly available documentation on Pepper Flash.
A standard version of Flash is also present on ChromeOS. It’s simply not the default renderer.
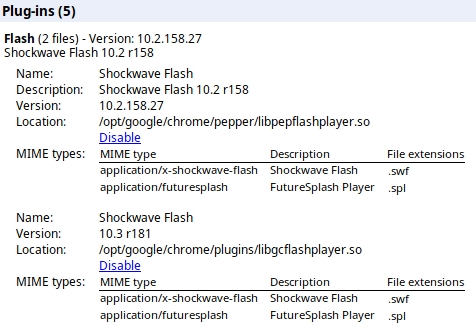
Here’s what things look like right now on a Chromebook:
As I said, we’re still awaiting final word from either Adobe or Google with regards to the security status of Pepper Flash 10.2.158.26. We’ll update this blog post accordingly.
Either way, now that Chromebooks have officially hit the market, better documentation is needed. With Adobe Flash being a very high-profile target, consumers should be able to easily figure out if they’re running the latest version or not.





















Pepper Flash for Google Chromebooks — What’s Going On?