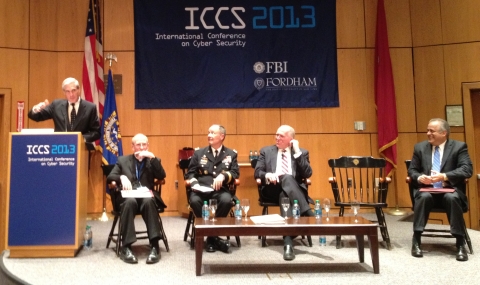
Last week, I attended the International Conference on Cyber Security at Fordham University in NYC. This event brought together participants from government, the private sector and academia. The closing session was a panel featuring the directors of the CIA, FBI and NSA which drew a lot of attention.
Throughout the conference, there was a strong push for more cooperation internationally and between different sectors. While cooperation has come a long way, we still have a long way to go.
The topic of cyber-espionage didn’t come up as much as I’ve been used to in recent times. Instead, there was more talk on cyber-sabotage with several presentations talking about this problem.
Some talks centered on disruptive attacks – i.e. DDoS. However both General Alexander and Sean Kanuck, National Intelligence Officer for Cyber Issues, also touched on destructive attacks. Their main concern was around data-wiping/altering malware such as Shamoon. We’ve been vocal about the potential of this type of attack and I’m glad this is being recognized by government.
General Alexander also announced that 90% of his network admins will be replaced by automation of some sort. It’s a move that makes a lot of sense. However, the more important part of the announcement is getting improved access controls to classified information to better prevent data leakage.
Data integrity and access controls are on the minds of the US government. It should be on yours too.



















NSAccess Control Lists