
Yesterday Arbor Networks reported that malware (which we detect as Trojan-Banker.Win32.Banker.alwa and Trojan-Banker.Win32.Banker.alwe) was using Twitter as a control system to command infected machines.
But it’s not just Twitter being used by this malware, but Jaiku as well.
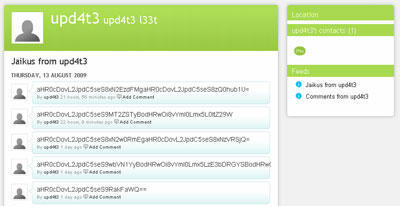
You might never have heard of Jaiku, but it’s very similar to Twitter. And it’s being used in the same way, with someone sending commands encrypted in Base64 to an account:
Decrypting some lines we can see two links:
http://bit.ly/******
http://bit.ly/******
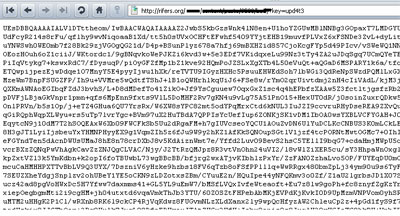
that lead to a page with more Base64 code:
This code gets downloaded by the malware, decrypted and saved as an infection component, updating the malware sitting on compromised machines.
So Brazilian cybercriminals are right on the money when it comes to finding new attack vectors; although Jaiku isn’t anywhere near as popular as Twitter, this attack shows they’re out to find as many victims as they can.






















Not just Twitter, Jaiku too