
Fostering knowledge exchange among different generations of security researchers is maybe one of the best traits of a good security conference. Judging by its attendance, NoSuchCon can easily claim to be one of these. It’s rare to see such a mix of young researchers and old gurus exchanging ideas and getting to know each other. Organized this year in Paris, NoSuchCon takes place in the premises of the Espace Oscar Niemeyer; admittedly, indeed a nice move putting a security conference within an art exposition center (congrats to the organizers :)) .

Espace Oscar Niemeyer
As security professionals, however, our attention rightly lies in the quality of the talks. Fear not, NoSuchCon has been offering quite an impressive lineup. The first day has passed, and until now I have been appreciating both keynote and technical talks. The former heavily focused on presenting (sometimes strong) opinions on current matters, while the latter showing impressive (very) technical insights and hacks. Let’s go through some examples of both categories (for more interested readers, note that each pack of slides is made available here right before the talk commencing)

Keynote
The conference bootstrapped with the keynote by Andrea Barisani. The talk revolved around a rather simple concept: security research has now become a sensitive topic. What Andrea meant is that researchers should feel the responsibility of properly disseminating the hard-gained results of their researches. Stating why a research has been conducted, for example, might be prominent so to avoid any possible misunderstanding with the public. Likewise, failed research attempts should be published somehow, so to spread among fellow researchers the lessons that have been learned in the process. Unfortunately, as pointed out, this hardly happens.
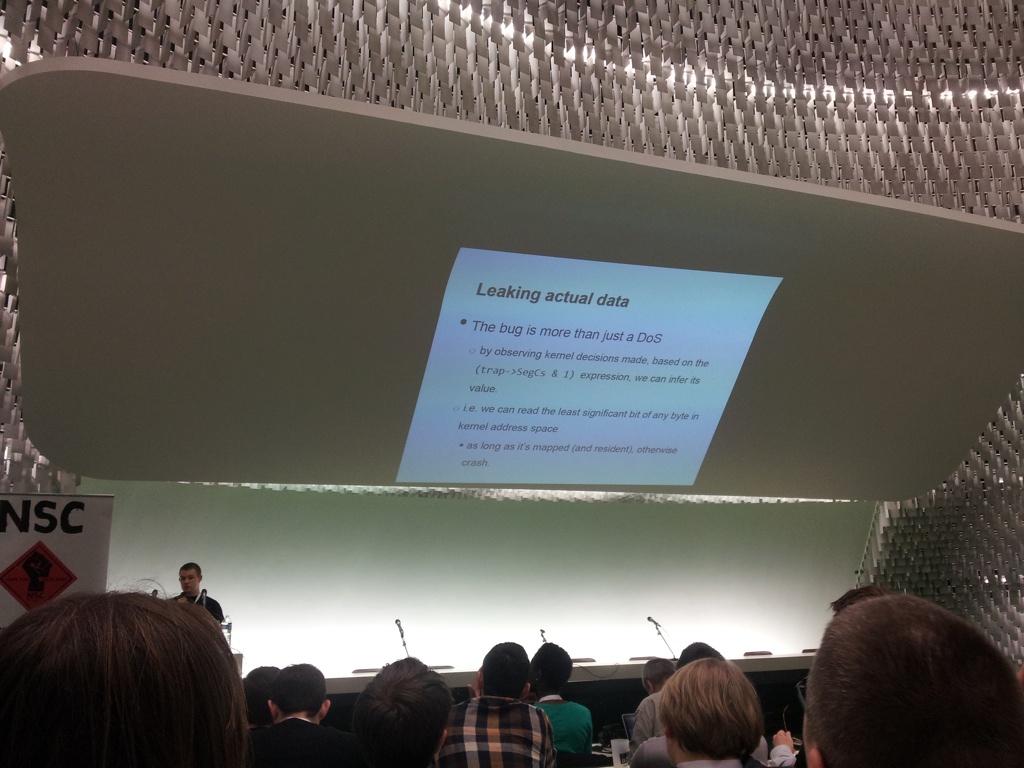
The technical talks morning lineup had Mateusz “j00ru” Jurczyk as first speaker. The talk’s title Abusing the Windows Kernel: How to Crash an Operating System With Two Instructions is quite self-explanatory (for who’s curious here they are: xor ebp, ebp; jmp 0x8327d1b7; basically the page fault handler is easily tricked into believing the ebp trap-framed register to be a pointer to the kernel stack when the eip register is set to some magic values; note that any invalid memory access in kernel mode inevitably leads to a bug check). What the title does not sufficiently dispel is that this was just an example of the many corner-cases (like the actual implementation of memcpy as pointed out by the speaker) that often go untested by security professionals because considered already well-studied and properly checked for bugs.
Abusing the Windows Kernel
The afternoon was the time of Alex Ionescu, well known co-author of OS-bibles such as Windows Internals. His talk was a tale down the rabbit hole of the SMC (System Management Controller), a standard component of our beloved MACs. That chip is used to manage all kind of things such as light sensor, accelerometer, voltages, etc. However, like any other controller it has its logic stored somewhere, a ROM, which reversing would surely lead to interesting discoveries (remember that the SMC is also used to store your FileVault password for instance). Interesting enough, the ROM can be updated, but not read as easily. The talk kept unveiling many details of the underlying architecture and logic (the SMC also includes a nifty programmable timer that can be configured to execute specific actions, such as reboots, at specific times). Funny fact: some code paths are executed only when Specialis Revelio is used as input string (clear reference to the Harry Potter saga; no wonder why the title of the talk was “Ninjas and Harry Potter”). Unfortunately the whole firmware remains largely a mystery, as only 30% have been reversed (maybe more at the next conference?).
As far as I can tell the second day looks as promising as the first, but that is all from Paris for now. Stay tuned for more updates, and in the meanwhile, stay safe!





















NoSuchCon 2013