
Microsoft has released a beta version of its antispyware program. Response from the IT community has been mixed so far, not surprisingly.
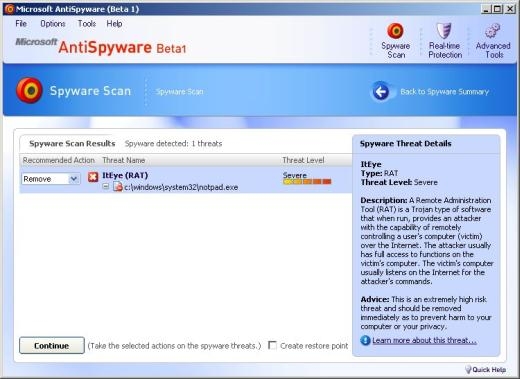
For instance, today we received a report about MS AntiSpyware flagging a suspicious file:
“c:winntsystem32notpad.exe” was detected as a Remote Administration Tool.
This file – which was a French version of notepad – would normally be called notepad.exe. For some reason, we don’t know why, the file was renamed as notpad.exe.
When we looked closely, it was clear what this file was. So we figured that MS AS had a faulty signature meaning this particular French version of notepad is detected as ItEye RAT.
Not every version (language, build) of every (Windows) file gets tested to check for false alarms, so this might have slipped by.
However we quickly realized that it was the combination of file name/location that made MS AntiSpyware go off.
In fact, the beta version of MS AntiSpyware detects any file with the name “notpad.exe” – even a completely empty one – residing in %sysdir% as being this particular RAT.
So at least a part of the “ItEye RAT” detection is strictly based on filename/location, which can result in situations like these.
Because of this, we think it’s best to detect files by file signatures, not location.





















MS AntiSpyware and file locations