
Google Chrome users are being targeted these days by a wave of attacks that uses malicious extensions hosted in the official Chrome Web Store. The attack appears to be of Turkish origin and is using Facebook to spread. We saw users of different nationalities infected with the malicious extensions, which the cybercriminals are sending to the official store regularly, in a cat-and-mouse game.
As we already reported in March 2012, Brazilian cybercriminals were able at that time to host a malicious extension in the Chrome Web Store. Since then in June 2012 Google has changed the way users can add third party browser extensions i.e. not allowing the installation that are not hosted on the official Web Store. More recently Google removed the possibility of silent installations, which has been widely abused by third parties.
Maybe for these reasons bad guys started to concentrate their efforts to upload bad extensions to the official store. Now its the turn of Turkish cybercriminals; they were able to host several extensions there in the last few days.
In one of the attacks monitored by us, some infected user profiles on Facebook started to disseminate this message, which contains some names of contacts from the victim and a link:
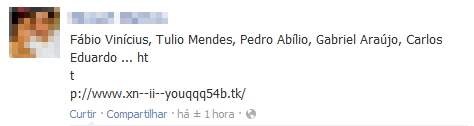
Profiles spreading a link to .tk page
We collected several links, all pointing to a .tk page:
|
1 2 3 4 5 |
http://www.facebookhiledunyasix.tk http://facebookdayi.tk/ http://superhilemerkezi.tk/ http://facebooklikerr.tk/ http://facebooksuperhile.tk/ |
The links directs to a page written in Turkish, offering a supposed update of Google Chrome:
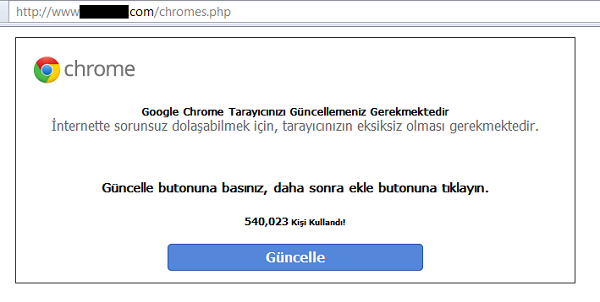
“You should update your Google Chrome”
The page also guides the user to install an extension
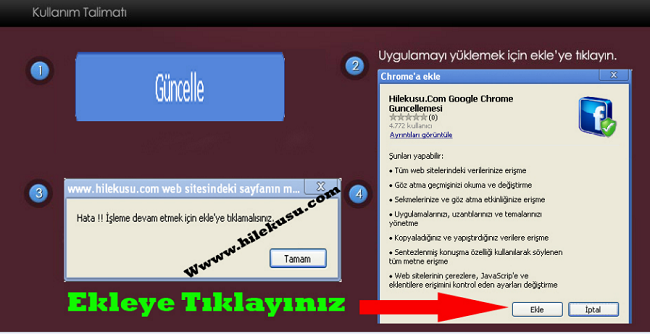
called “Chrome Guncellemesi” or “Chrome Update”. In other attacks they used the name “Flash Player 12.1”, all of these cases were hosted on the official Web Store:
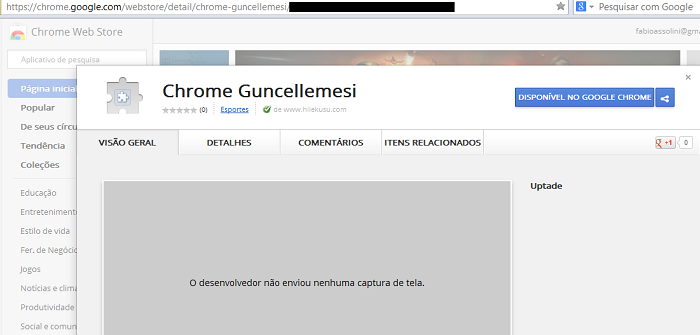
Checking the permissions asked for, the extension we can see asks to access all your data on all websites, manipulate settings, cookies, plugins and more:
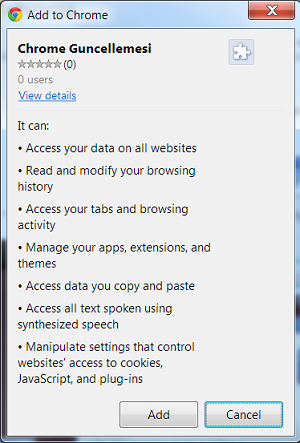
“I want your permission to do all I want in your browser”
It’s not a problem if you are a Firefox user; they also have a version for you:
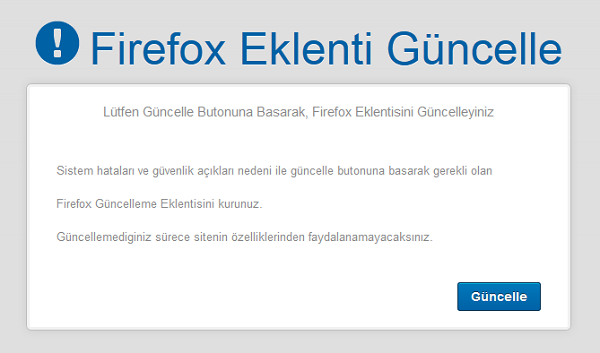
“Install a Firefox plugin extension”
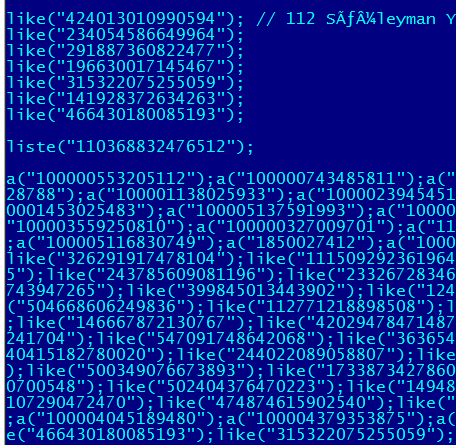
After installation on a user’s computer the extension does a number of malicious things; such as doing the action “like” on several profiles of users and company pages, as part of a scheme to sell “likes”. It can also control your Facebook profile entirely, collect cookies, post in your wall, etc.
We reported all the malicious extensions we found to Google and they are removing it quickly but the cybercriminals are constantly uploading more and more.
We detect the malicious extensions as Trojan.JS.Agent.bzv, and all the malicious URLs are blocked. If you are a Google Chrome user, be aware; avoid installing unknown extensions, even if it comes from the official Web Store.
Malicious Chrome extensions: a cat and mouse game




















Daniele Tetlow
I made the mistake of putting Chrome as search engine and I think it is a copy cat website. I cannot get rid of it.
I received a notification from microsoft saying I had a virus but I do not know if I should trust it.
I keep receiving flashing adds when I am looking for something and when I try to close the tab it actually opens it!
Please help
Thanks