
It’s nothing new for malware authors to use big news to promote their executables – social engineering tactics are used to trick users into downloading and running malicious programs.
These tactics take advantage of the interest created around certain mainstream news subjects, such as 9/11, Hurricane Katrina or the US Elections. It’s now the turn of the Large Hadron Collider, the biggest particle accelerator on Earth, to unwittingly help malware authors spread their creations.
While following the latest news on the LHC experiment on digg.com, I came upon an apparently ordinary comment left, of course, by an apparently ordinary user called “Edwawils1976”.
By the way, you can watch “Large Hadron Collider” start video report at
http://***sed.com/clip/?id=Large_Hadron_Collider
Pretty interesting, isn’t it?”
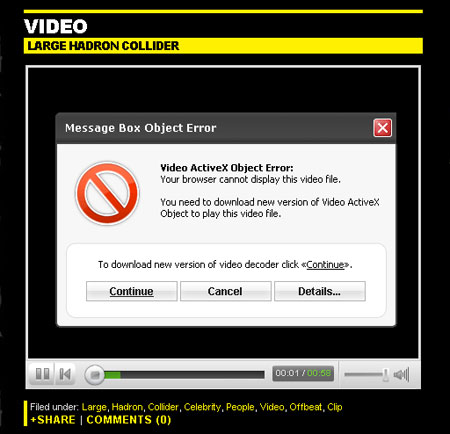
The link takes the curious visitor to a page containing a fake video player, which requires the user to download some special codec or plug-in in order to play the video. This is the moment when the user is tricked into downloading and running the malicious software.
The malware served to the unknowing user varies – so far, we’ve captured a number of Trojan downloaders with different payloads, such as Trojan-Downloader.Win32.FraudLoad.vbzg and Trojan.Win32.FraudPack.fd. Of course, programs like these could be used to spread any piece of bad software, ranging from bots that transform users’ computers into zombies to rogue AV products such as XP Antivirus 2008.
So you can see that in between keeping an eye on the end of the world, we’re also constantly on the watch for new malware, and working to get this site shut down.






















Large Hadron Collider spreads malware