
This year, Christians all over the world will be celebrating Easter Day on 4 April.
The Easter holidays of today barely resemble the quiet exchange of chocolate eggs and cards that they once did. Thanks to ruthless exploitation by all and sundry, Easter now encompasses a whole host of events and activities completely unrelated to the death and resurrection of Jesus Christ. Naturally, spammers wouldn’t miss such a golden opportunity to get in on the action too and have rather predictably come up with some ‘Easter themed’ mass mailings of their own.
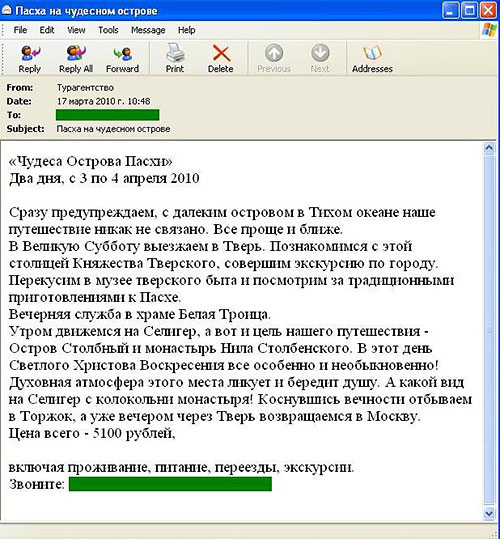
It has to be said that the spammers have been quite inventive in their exploitation of the Easter theme this time though. The most popular Russian messages contain an advert for a sightseeing tour supposedly taking place on the Easter weekend. Below is a screenshot of the spam mailing offering users the chance to visit a number of religious sites located in the regions surrounding Moscow:
English-language spammers have taken it one step further.
Shortly before Christmas many Internet users received messages offering personalized letters from Santa Claus. Now, in the run-up to Easter, spammers have switched authors and are offering personalized letters from none other than the Easter Bunny!
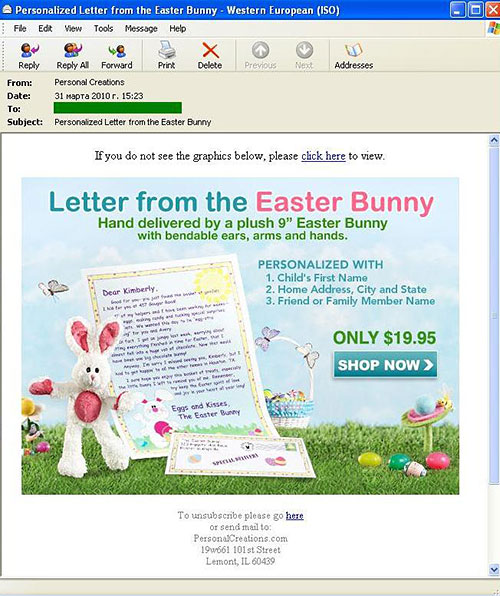
Looking at the price of the Easter Bunny letters, it’s almost a dead cert that it’s from the same source as the Christmas emails – remarkably, the ‘Bunny’ is charging exactly the same amount as ‘Santa’ did.
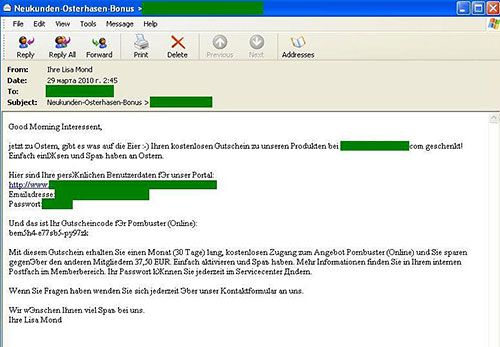
If you think the Russian and English spammers had stretched the Easter theme to the max, check out what the German spammers got up to! For the second year in a row they have used Easter to promote porn sites.
In the email above, this particular bunny’s idea of celebrating Easter is to offer the recipient a one-month free subscription to an adult content site.
Like many other holidays, Easter is open-season for the spammers, but no matter how attractive the offer seems you can bet your bottom dollar that the majority of goods and services touted by the spammers won’t live up to your expectations. Finally, it is worth mentioning that the porn sites that they relentlessly push virtually always contain malware.





















It’s an Easter Spam Eggs-traviganza!