
As we published last year, the first Internationalized domain names (IDN) using non-Latin characters appeared on the internet; these contain characters from Cyrillic, Arabic and other languages. We also started to see some news domains using diacritics such as “, , , , , , , , , , , , , “ in their names, or accents, for instance as seen in http://amarylliscomunicao.com.br.
It’s also important to point that some browsers and mail readers aren’t prepared to show these characters correctly. A domain in Arabic such as http://وزارة-الأتصالات.مصر/ might be shown as http://xn--4gbrim.xn—-ymcbaaajlc6dj7bxne2c.xn--wgbh1c in your mailbox. We call this alternate way to show non-latin characters punycode.
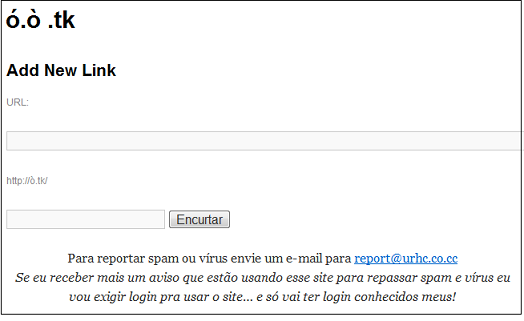
During our regular monitoring of malicious activities in Brazil, we discovered an interesting and legitimate URL shortener service which is using the diacritics “.” in his name:
And everybody knows that cybercriminals love to use URL shortener services. In this case, there’s no exception – various Brazilian bad guys started to use this service to decrease the size of URLs in phishing messages and also to rise the curiosity of users, presenting a URL with accents:
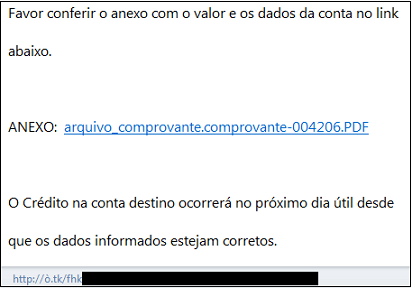
The message above shows a link pointing to a very common Brazilian trojan banker detected as Trojan-Downloader.Win32.Delf.bbwp.
So, when receiving e-mail messages, be careful with short links, even those showing odd accents and non-latin characters!





















Internationalized Domain Names used to spread malware