
Recently, we’ve been noticing ever more dubious advertising libraries in popular apps on Google Play. The monetization methods used in such SDKs can pose a threat to users, yet they pull in more revenue for developers than allowlisted ad modules due to the greater number of views. In this post we will look into a few examples of suspicious-looking ad modules that we discovered in popular apps earlier this year.
One of the applications we researched was a popular app that allows users to ask questions anonymously. Integrated into the code of an earlier version of the app was the module com.haskfm.h5mob. Its task was to show intrusive advertising (in breach of the Google Play rules) when the user unlocked the phone.
Code for displaying ads when the screen is unlocked
In other words, the module can show ads whether the app is running or not. The ad can simply pop up on the main screen all on its own, causing a nuisance for the user. We passed our findings to the app developers, who promptly removed com.haskfm.h5mob. However, this module remains interesting from technical point of view.
In this application to receive advertising offers, the module connects to the C&C servers, whose addresses are encrypted in the app code.
Decrypting the C&C addresses
The C&C response contains the display parameters and the platforms used to receive ads.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 |
{"status":1, "msg":"Success", "data":{"rqect":0, "ldfr":1, "tifr":1, "appintset":43200000, "swpa":1, "ssjp":1, "tcap":86400000, "ctoftime":3600000, "jtslist":[{"domain":"app.appsflyer.com","format":"&android_id={android_id}&advertising_id={gaid}"}, {"domain":"app.adjust.com","format":"&android_id={android_id}&gps_adid={gaid}"}, {"domain":"app.adjust.io","format":"&android_id={android_id}&gps_adid={gaid}"}, …… |
The most interesting parameter here is appintset, which specifies the delay before displaying the first ad after installation of the app. In our example, it was set to 43.2 million milliseconds, or 12 hours. This delay makes it much harder for the user to find the culprit for all the ads that suddenly appear on the screen. Also, this technique is frequently used by cybercriminals to trick automatic protection mechanisms, such as sandboxes in app stores. The main parameters are followed by an extensive list of addresses of advertising providers with request parameters for receiving offers.
Earlier we detected a similar ad module in apps without a payload. For example, the code in the app com.android.ggtoolkit_tw_xd, which we detect as not-a-virus:AdWare.AndroidOS.Magic.a, contains the same features and is managed from the same C&C as the com.haskfm.h5mob module. However, this adware app has no graphical interface to speak of, is not displayed in the device’s app menu, and serves only to display intrusive ads as described above. It looks something like this: adware_in-app_video.mp4
While, as previously mentioned, the creators of the application described in the first example, promptly removed the ad module, not all Android developers are so conscientious. For example, the Cut – CutOut & Photo Background Editor app does not hesitate to treat users to a half-screen ad as soon as the smartphone is unlocked, regardless of whether the app is running or not.
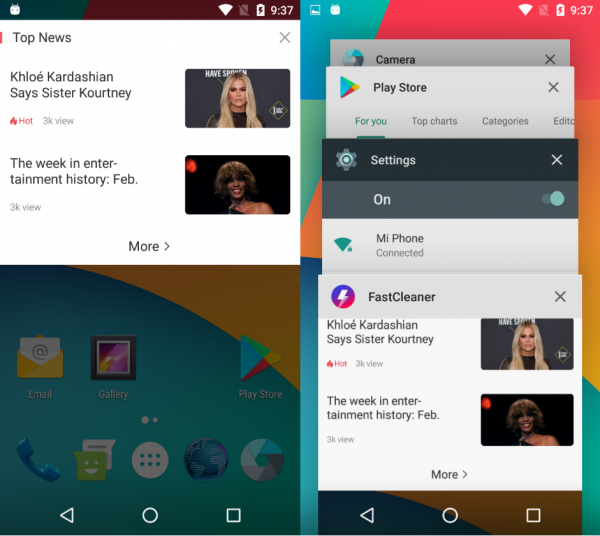
Likewise the Fast Cleaner — SpeedBooster & Cleaner app.
In both apps, the library com.vision.lib handles the display of advertising.
Display of advertising
At the time of writing this article, the developers of both apps had not responded to our requests.
Note, however, that adware is not always about greed. Often, app developers are not versed in advertising SDKs and lack the necessary skills to test an integrated advertising library, and therefore may not fully understand what they are adding to their code. The danger for users here is that a dubious library could unexpectedly make its way into an app as part of a rank-and-file update. And it becomes extremely difficult to figure out which of a dozen recently updated apps is the source of intrusive advertising.
IOCs
MD5
1eeda6306a2b12f78902a1bc0b7a7961 – com.android.ggtoolkit_tw_xd
134283b8efedc3d7244ba1b3a52e4a92 – com.xprodev.cutcam
3aba867b8b91c17531e58a9054657e10 – com.powerd.cleaner



























Aggressive in-app advertising in Android