Thanks to my colleague Christian for providing the info for this post
Today, 24th January, the famous Macintosh celebrates its anniversary – it was 25 years ago to the day that Steve Jobs introduced the first Macintosh Computer, the 128K, at Apple’s AGM. It was the first commercially successful personal computer to feature a mouse and a graphical user interface rather than a command line interface – a big step at the time. With devoted Mac followers guessing and gossiping about what the future holds, let’s take a quick look back at malware and security for Mac over the last few years.
Traditionally, malware writers have overlooked Mac in favor of targeting Windows with its bigger market share. But the proof-of-concept samples which appear periodically show that Macs aren’t invincible.
We wrote about two such examples in 2006 – IM-Worm.OSX.Leap.a, which tricked users by pretending to be screenshots of Leopard, the latest version of OS X, and spread via iChat; and Worm.OSX.Inqtana.a, which exploited a Bluetooth vulnerability and attempted to infect other Bluetooth devices within range.Apple’s switch in 2006 to x86 architecture opened up new horizons; the ability to run Windows natively, and lower prices attracted new users. The result: a steadily rising market share, from 2.88% at the end of 2004 to more than 10% by the end of 2008. The downside: increased popularity lead to an increase in the number of malicious programs targeting Macs.
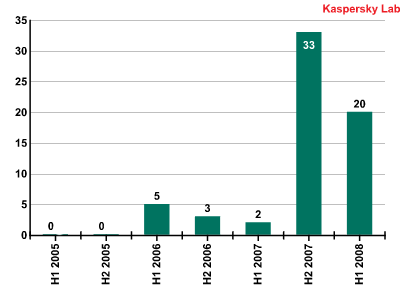
Although the numbers shown above are low – especially in comparison with Windows based malware – the abrupt rise in 2007 is a bit scary. We’ve all seen that once market share of any device achieves a certain critical mass, malware writers start targeting it. And these days, it’s going to be cyber criminals who are looking for serious profits from the attacks they conduct. Incidentally, as I write, there’s a new Trojan making the rounds, Backdoor.Mac.iWorm.a. While it could be said that this malicious program is written in order to teach software pirates a lesson – it disguises itself as a free version of iWork 09 – malware is always malware.
It’s not just computers that are at risk. Apple’s other products such as the iPod and the iPhone, with their ever evolving functionality and networking capabilities, also offer new opportunities for malware attacks.
So Mac users have to learn to take care of their systems in the same way that Windows users do by updating their OS and applications regularly. The iTunes media player and Safari are particularly well known for containing vulnerabilities. Although Mac is currently one of the least attacked systems, security has to be taken seriously in order to maintain this happy situation.
Happy Birthday Macintosh! Here’s to the next happy – and healthy! – 25 years.





















Happy birthday, Mac!