
Hackers are known to target inexperienced users. And hackers are known to work in teams, with each team member using his/her particular skills to make sure a task gets accomplished.
But what about hackers that don’t target the users directly? There are some out there, and they’re targeting inexperienced hackers to get them to unwittingly give away information that the first group of hackers can then use.
Today I’ve got an interesting example of how hackers steal from other hackers.
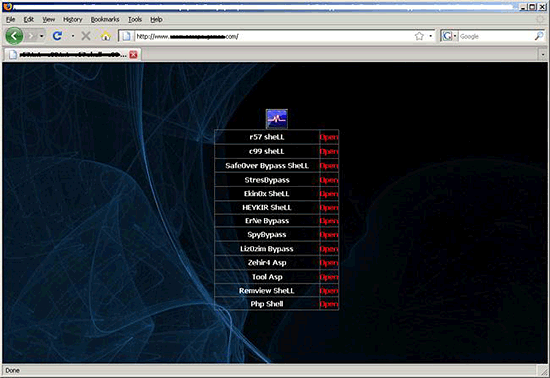
They create a website hosting PHP shells, backdoors used to break into vulnerable websites. There’s nothing extraordinary about this – it’s just one hacker helping another. But if the hackers are out to steal data from other hackers, there’s a catch with the PHP shells: they’re slightly modified, but an inexperienced hacker wouldn’t notice the modification.
Every shell has an obfuscated javascript included, usually at the end of the PHP shell code. Sometimes it’s also embedded several times in different places in the same file, just to make it even harder for an untrained eye to pick it out.
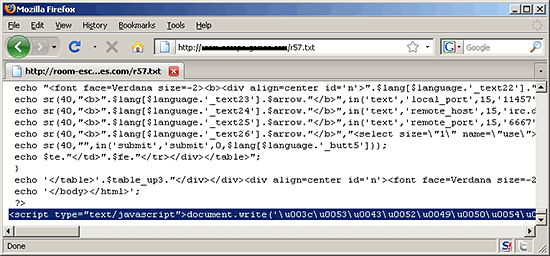
After deobfuscation, we can see clearly that the code executes an external script:
And this is what that external script looks like:
It uses the javascript object “location.href” to get the URL of the vulnerable website the inexperienced hacker is trying to exploit and calls the yaz.php file with a parameter indicating the URL of the page where the shell was used. The yaz.php file probably collects all the URLs given to it into a database. This means the hackers who created the website get a huge database of vulnerable websites – a database created by other hackers who weren’t experienced enough to notice the modifications in the PHP shell used.
This is an eye-opening illustration of “no honour among hackers” – they’re not just attacking unsuspecting users, but others of their own kind, all in the name of getting access to as many servers as possible. Incidentally, this also happens in the world of phishing – some phishers added a script to their phish-kits so that captured data would be sent to them as well as to the phisher that bought the kit. Are events like this rare exceptions, or is “hackers hacking hackers” (try saying that three times fast!) becoming a trend?






















Hackers hacking hackers