
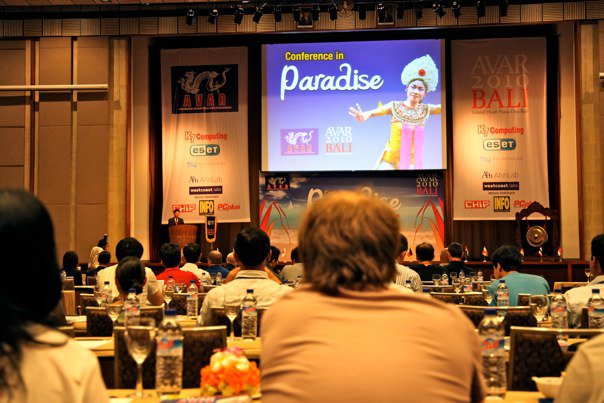
Apa kabar! AVAR 2010 has just finished. It took place on the beautiful Bali island of Indonesia.
AVAR is the biggest international anti-malware event in the Asia-Pacific region. It is one of the best opportunities for industry experts from around the world to get together in a relaxed environment and discuss the latest hot topics. The papers presented in the last two days cover subjects ranging from PDF exploits, targeted attacks and mobile malware, to AV testing and rogue software.
We are proud to announce that Kaspersky Lab was the most active presenter here, with exactly 4 speakers:
- Roel Schouwenberg – Adobe: The currently most exploited software in the world
- Denis Maslennikov – Getting rich with mobile malware: the how, the where, and the $$$
- Evgeny Smirnov – Image spam filtering by optical pattern matching
- Stefan Tanase – Surviving Targeted Attacks: Beyond Today and Tomorrow
And that’s not all: our own Stefan Tanase managed to win the Best Speaker Award, for the second year in a row. Congratulations!

We’re spending our last day here in paradise enjoying the beautiful places this island has to offer. Until next year, selamat tinggal and have a wonderful weekend!




















Greetings from AVAR 2010