Earlier today, Softpedia reported that an Algerian hacker using the nickname MCA-CRB has managed to deface the Romanian sites of Google (google.ro) and Yahoo! (yahoo.ro).
Screenshot of the defaced Google.ro domainWhen we found out about this incident we were pretty skeptical of these websites being hacked. A website as large as Google can be hacked, in theory, but it’s highly unlikely. We then noticed that both domains resolve to an IP address located in the Netherlands: 95.128.3.172 (server1.joomlapartner.nl) – so it rather looks like a DNS poisoning attack.
The question which remains unanswered up until now is where exactly the DNS spoofing/poisoning attack has happened.There are several possible scenarios here:
- RoTLD (the Romanian Top Level Domain Registrar) was hacked, allowing the attacker access to all .ro domains DNS settings. Not all .ro domains were affected, so this scenario is highly unlikely to have happened.
- Google and Yahoo’s RoTLD accounts were compromised, allowing the attacker to just change their DNS settings. This scenario is also unlikely to have happened, as we’ve discovered that it’s not just Google and Yahoo websites, but also Paypal, Microsoft and others.
- At the moment, our best guess is that an ISP-level DNS poisoning attack is happening in Romania. Some domains are redirected, others are not.
All this could have been much worse if the attacker had other goals in his mind than just becoming famous by defacing famous websites. Imagine how many accounts could have been compromised this morning if these websites were redirected to a phishing page, instead of a defacement page.
At the moment, we are performing a wide zone scan for all .RO domains to determine the extent of this attack.
We will update the blogpost with new information as it becomes available.
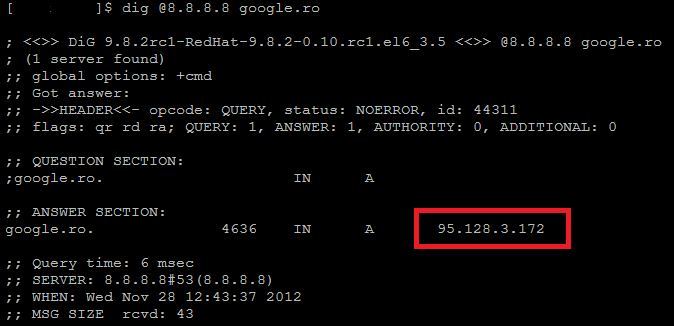
UPDATE We have tested various DNS servers for the poisoning attack, and for the moment, the only ones which reply with the hijacked entry are 8.8.8.8 and 8.8.4.4 (Google’s public DNS servers). We couldn’t identify any other Romanian DNS server which exhibits this behavior.
UPDATE 2 You can test the DNS poisoning attack by yourself using dig: dig @8.8.8.8 google.ro or dig @8.8.4.4 google.ro
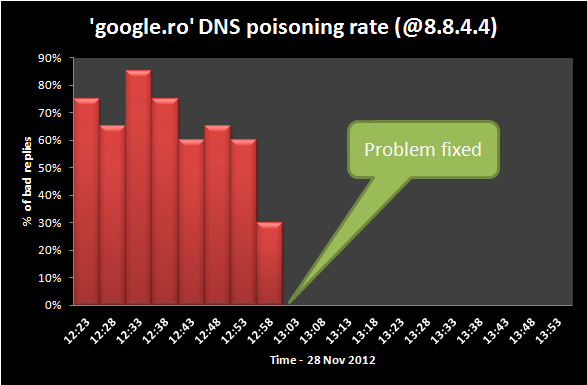
UPDATE 3 According to our monitoring, the Google DNS server(s) at 8.8.8.8 are no longer serving poisoned answers. The other Google DNS server(s) at 8.8.4.4 appear to still redirect users to the attacker’s IP address. We are assuming that Google might be fixing the hijacked records as we are writing this.
UPDATE 4 It appears the problem with the Google.ro domain has been fixed around 13:00 GMT +2 (Romanian time) on both DNS servers (8.8.8.8 and 8.8.4.4). Other domains such as Paypal.ro are still not fixed.
UPDATE 5 After analyzing the latest evidence, it seems the most probable scenario for today’s DNS hijacking/poisoning incident is a compromise at RoTLD – The Romanian Top Level Domain Registry. Earlier this month, a similar incident took place at the Irish Domain Registry – IEDR. You can see IEDR’s statement here. RoTLD has not come out with a statement yet.
The full list of .RO domains affected by today’s incident:
- google.ro
- yahoo.ro
- microsoft.ro
- paypal.ro
- kaspersky.ro
- windows.ro
- hotmail.ro
We will continue to monitor the situation.
Google.ro and RO domains Victims of Possible DNS Hijacking





















Mohammad
Today, 2016/Apr/08, when I want to go to http://www.google.com I face up with this:
https://www.google.ro/?gws_rd=cr&ei=5v0HV4DsJcKe6ATjvbeQDQ
what is it? why I have to direct to this site? I’d not experienced this two or three ago. Is it secure? Meanwhile, I’m from Iran.