
“Nigerian” spammers are extremely quick to react to the world’s hottest news stories. News of the death of former Libyan leader Muammar Gaddafi had barely even broken before a string of emails from the “relatives of the deceased” began to appear.
Gaddafi’s inconsolable relatives would be amazed if they knew how many emails had been sent in their name to Internet users around the world.
Instead of joining in the funeral rites, it looks like Gaddaffi’s sons and daughters, or his wife, his brothers or even friends, have rushed straight to their PCs to write to people all over the world asking for help in spiriting uncountable millions of dollars out of the country.
According to the “Nigerians”, the family of the Libyan leader is worth hundreds of millions of dollars. The emails which fell into my hands cited a minimum figure of $300 million.
Most of these emails purport to come from “Gaddafi’s wife”. The spammers seem to think their heart-rending stories about her hard life in her husband’s family could explain her sudden desire to share his money with her close friends. Or even with distant strangers, depending on the recipient of the email.
She’s not alone, though: an unlikely coalition of “opposition forces”, “lawyers” and “bank clerks who have access to Gaddafi’s accounts” also share the general desire to transfer the Colonel’s money abroad.
“Nigerian” spam is, of course, pure fraud. None of Gaddafi’s wives or even his lawyers will ever send emails to someone they do not know asking for help in getting millions of dollars out of the country and offering an unknown agent the commission for doing so. If a user takes the bait the fraudsters will extort money from him to allegedly cover different “expenses” until no more money is left. One should be realistic about the many offers received via the Internet from an unverified source calling himself Colonel Gaddafi’s son (ALL OF A SUDDEN!).
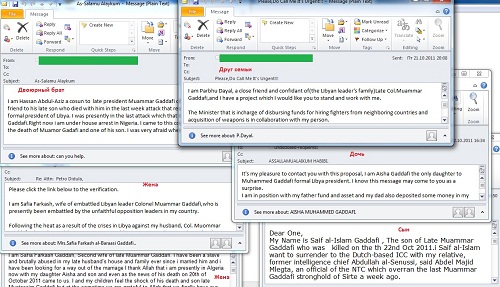
Below are the screenshots of several “Nigerian letters” sent on behalf of Gaddafi’s family:






















Gaddafi’s death in spam