
After intercepting one of the domain names used by the Flashback/Flashfake Mac Trojan and setting up a special sinkhole server last Friday, we managed to gather stats on the scale and geographic distribution of the related botnet. We published information on this in our previous blog entry.
We continued to intercept domain names after setting up the sinkhole server and we are currently still monitoring how big the botnet is. We have now recorded a total of 670,000 unique bots. Over the weekend (7-8 April) we saw a significant fall in the number of connected bots:
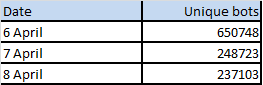
This doesn’t mean, however, that the botnet is shrinking rapidly – these are merely the numbers for the weekend.
Over the last few days our server has registered all the data sent by bots from the infected computers and recorded their UUIDs in a dedicated database. Based on this information we have set up an online resource where all users of Mac OS X can check if their computer has been infected by Flashback.
To find out if your computer is infected and what to do if it is, visit: flashbackcheck.com
Also users can check if they’re infected with Flashfake by using Kaspersky Lab’s free removal tool.
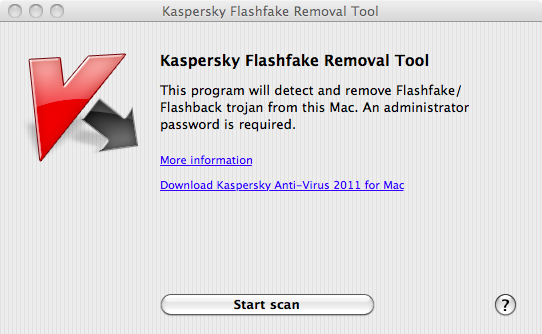
Flashfake Removal Tool and online-checking site






















chamara
Thank youAlexander! Keep up the good work.
Tammy
When I go to the flashbackcheck.com page it says nothing is there. Can’t find it. ?
s.r.sethuraj
No exe file for windows