
Earlier this week, Dr.Web reported the discovery of a Mac OS X botnet Flashback (Flashfake). According to their information, the estimated size of this botnet is more than 500, 000 infected Mac machines.
We followed up with an analysis of the latest variant of this bot, Trojan-Downloader.OSX.Flashfake.ab.
It is being distributed via infected websites as a Java applet that pretends to be an update for the Adobe Flash Player. The Java applet then executes the first stage downloader that subsequently downloads and installs the main component of the Trojan. The main component is a Trojan-Downloader that continuously connects to one of its command-and-control (C&C) servers and waits for new components to download and execute.
The bot locates its C&C servers by domain names, and these names are generated using two algorithms. The first algorithm depends on the current date, and the second algorithm uses several variables that are stored in the Trojan’s body and encrypted with the computer’s hardware UUID using RC4 cipher.
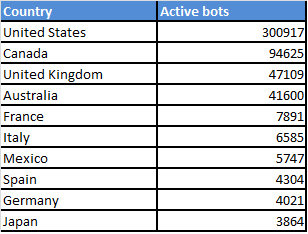
We reverse engineered the first domain generation algorithm and used the current date, 06.04.2012, to generate and register a domain name, “krymbrjasnof.com“. After domain registration, we were able to log requests from the bots. Since every request from the bot contains its unique hardware UUID, we were able to calculate the number of active bots. Our logs indicate that a total of 600 000+ unique bots connected to our server in less than 24 hours. They used a total of 620 000+ external IP addresses. More than 50% of the bots connected from the United States.
Geographical distribution of active Flashfake bots
We cannot confirm nor deny that all of the bots that connected to our server were running Mac OS X. The bots can be only identified by a unique variable in their User-Agent HTTP header named “id”, the rest of the User-Agent is statically controlled by the Trojan. See example below:
“Mozilla/5.0 (Windows NT 6.1; WOW64; rv:9.0.1; sv:2; id:9D66B9CD-0000-5BCF-0000-000004BD266A) Gecko/20100101 Firefox/9.0.1”
We have used passive OS fingerprinting techniques to get a rough estimation. More than 98% of incoming network packets were most likely sent from Mac OS X hosts. Although this technique is based on heuristics and can’t be completely trusted, it can be used for making order-of-magnitude estimates. So, it is very likely that most of the machines running the Flashfake bot are Macs.
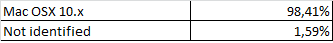
Approximate distribution of OSes used to connect to our server
Flashfake Mac OS X botnet confirmed






















Ed
I have been seeing indicators that Flashback.K Command and Control has been attempting to connect to Android devices. All the documentation I have seen points to this as being a MAC issue. Can anyone confirm that Android is now vulnerable to Flashback.K?