
As we continue to investigate the Duqu targeted attack, there is new information that suggests the malware was created to spy on Iran’s nuclear program.
Some background and facts:
Back in April this year, Iran announced it was victim to a cyber-attack with a virus called “Stars.” This article offers some additional details on that attack.
We can now confirm that some of the targets of Duqu were hit on April 21, using the same method involving CVE-2011-3402, a kernel level exploit in win32k.sys via embedded True Type Font (TTF) file.
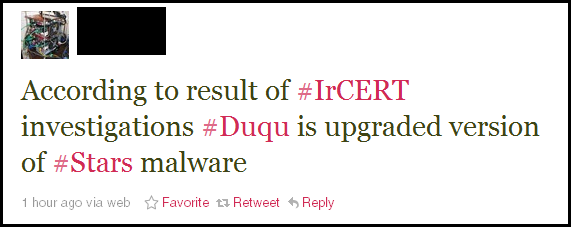
According to analysis by IrCERT (Iran’s Computer Emergency Response Team) Duqu is an upgraded version of “Stars”:
If we are to believe these reports, then it means that Duqu was created in order to spy on Iran’s nuclear program.
Just yesterday (November 4), the United Nations announced it was in possession of plans from Iran to make computer models of a nuclear warheads.
“The annex will also say that more than 10 nations have supplied intelligence suggesting Iran is secretly developing components of a nuclear arms program – among them an implosion-type.”
It would not be surprising that Stars and Duqu were used to collect such information.




















Duqu First Spotted as ‘Stars’ Malware in Iran