
Lots of bad things happen every day on social networks. Most attacks rely on cross-site scripting or web application vulnerabilities but I recently stumbled upon one particular attack that uses nothing more complex than social engineering to fool the unsuspecting (and perhaps even the suspecting) public. It’s a case that simply proves the old axiom: if something seems too good to be true, it probably is. Here’s how things unfolded.
Recently a friend on Facebook had this post added to her wall:

I’m always skeptical of applications that offer profile tracking services that Facebook itself doesn’t provide. It also seems unlikely an application would be able to track this information. So I thought I’d do some digging. After logging into a throwaway Facebook account, I visited the app page and got this:

Once you click the “Like” button, you’re asked to share the page. I never want to spam anyone, so I declined. Only to find this:

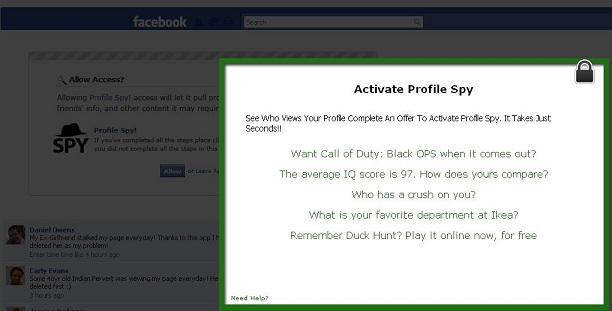
Well that doesn’t seem very friendly, does it? I wanted to know more about the app, so chose to share this app on my wall. I then got sent on to an Activate window which shows what appears to be a Facebook page in the background (more about that page later):
Even though I was pretty sure there was no official affiliation with Ikea, I’ve just moved, so I chose that option. After filling out some (fake) details on a sign-up page, I was told I had to give a valid cell number. Of course, I tried clicking “skip this step” but that just reloaded the page:
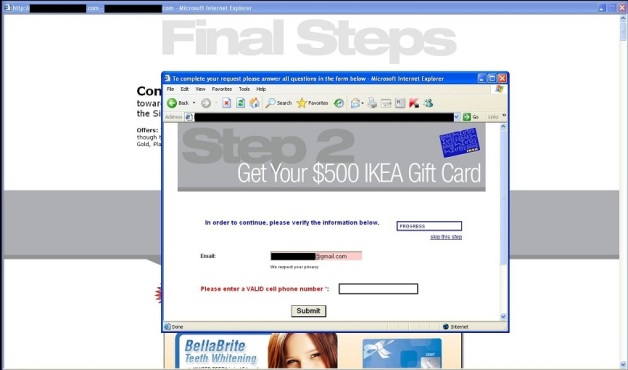
I chose to stop there, as whoever’s behind this is obviously up to no good. It’s highly likely that the personal information is being collected to be used for spam or other malicious purposes.
Once I was done, I revisited my wall to find the original post had been added, just as with my friend. So I decided to take a look at the application page to find out more. This is the page which got shown behind the Activate window – turns out it’s a page that’s not even on Facebook, and all the content is fake:

Nothing is clickable and all the testimonial profiles are bogus! The application page is designed to fool you into signing up for spam and providing personal information simply by using familiar Facebook colors and styles.
As I said at the beginning of my post, if it looks too good to be true, it probably is. And the flip side of this? Just because something looks trustworthy doesn’t mean that it is.



















Do You Know Who’s Really Viewing Your Facebook Profile?