
Every year, our anti-malware research team releases a series of reports on various cyberthreats: financial malware, web attacks, exploits, etc. As we monitor the increase, or decrease, in the number of certain threats, we do not usually associate these changes with concurrent world events – unless these events have a direct relation to the cyberthreats, that is: for example, the closure of a large botnet and arrest of its owners result in a decrease in web attacks.
However, the COVID-19 pandemic has affected us all in some way, so it would be surprising if cybercriminals were an exception. Spammers and phishers were naturally the trailblazers in this – look for details in the next quarterly report – but the entire cybercrime landscape has changed in the last few months. Before we discuss the subject, let us get something out of the way: it would be farfetched to attribute all of the changes mentioned below to the pandemic. However, certain connections can be traced.
Remote work
The first thing that caught our attention was remote work. From an information security standpoint, an employee within the office network and an employee connecting to the same network from home are two completely different users. It seems cybercriminals share this view, as the number of attacks on servers and remote access tools has increased as their usage has grown. In particular, the average daily number of bruteforce attacks on database servers in April 2020 was up by 23% from January.
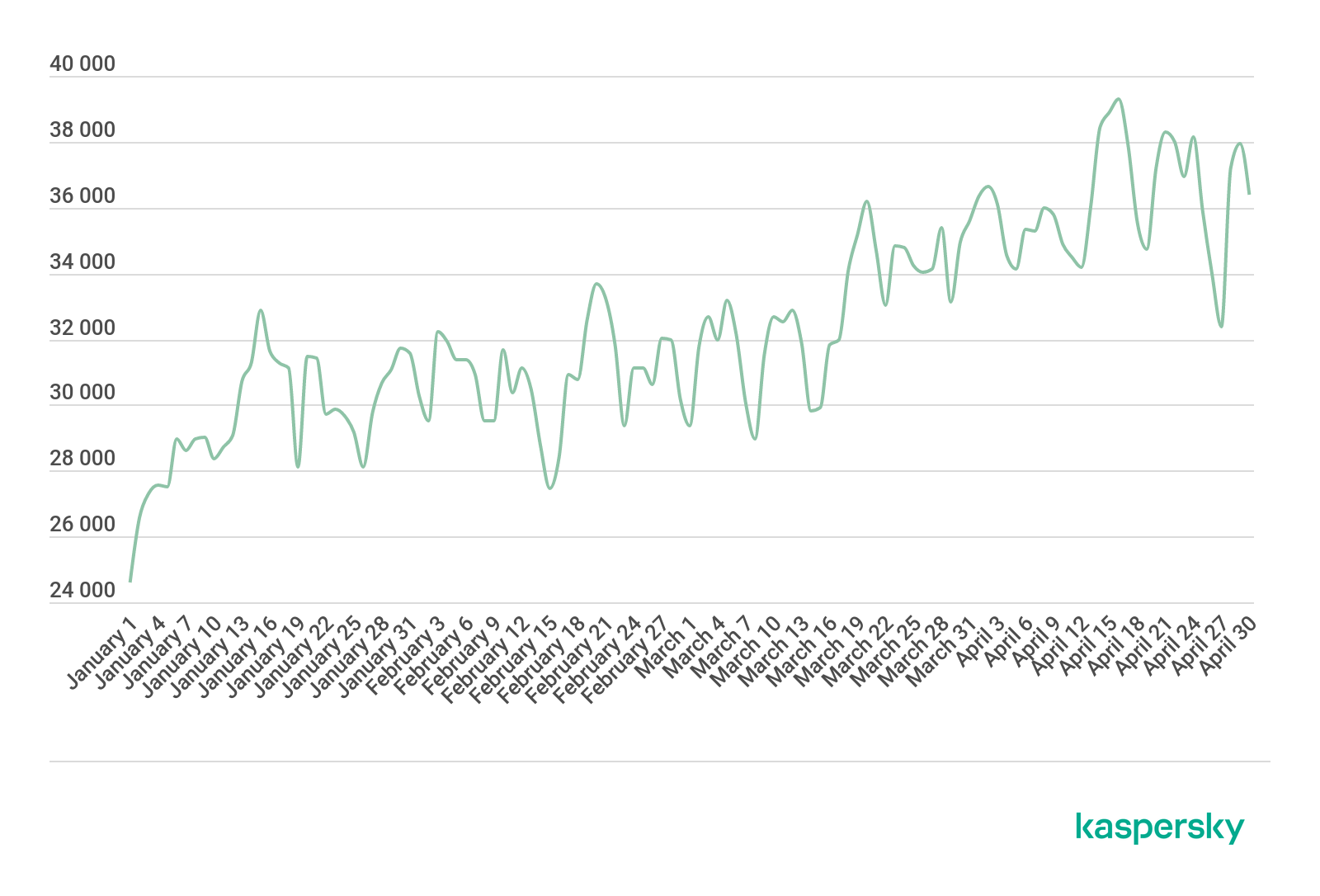
Unique computers subjected to bruteforce attacks, January through April 2020 (download)
Cybercriminals use brute force to penetrate a company’s network and subsequently launch malware inside its infrastructure. We are monitoring several cybercrime groups that rely on the scheme. The payload is usually ransomware, mostly from the Trojan-Ransom.Win32.Crusis, Trojan-Ransom.Win32.Phobos and Trojan-Ransom.Win32.Cryakl families.
RDP-attacks and ways to counter these were recently covered in detail by Dmitry Galov in his blog post, “Remote spring: the rise of RDP bruteforce attacks“.
Remote entertainment
Online entertainment activity increased as users transitioned to a “remote” lifestyle. The increase was so pronounced that some video streaming services, such as YouTube, announced that they were changing their default video quality to help with reducing traffic. The cybercriminal world responded by stepping up web threats: the average daily number of attacks blocked by Kaspersky Web Anti-Virus increased by 25% from January 2020.

Web-based attacks blocked, January through April 2020 (download)
It is hard to single out one specific web threat as the driver – all of the threats grew more or less proportionally. Most web attacks that were blocked originated with resources that redirected users to all kinds of malicious websites. Some of these were phishing resources and websites that subscribed visitors to unsolicited push notifications or tried to scare them with fake system error warnings.
We also noticed an increase in Trojan-PSW browser script modifications that could be found on various infected sites. Their main task was to capture bank card credentials entered by users while shopping online and transfer these to cybercriminals.
Websites capable of silently installing cookie files on users’ computers (cookie stuffing) and resources that injected advertising scripts into users’ traffic together accounted for a significant share of the web threats.
Cyberthreats on lockdown





















Cybersecurity Dubai
Good article, now wonder that attacks are going up during the lockdown