
Cryptolockers have become more and more sophisticated, bypassing system protections and terrifying anyone in their path. TeslaCrypt, CryptoWall, TorrentLocker, Locky and CTB-Locker are only some of the malware we have protected from for the past two years. We have seen many shapes and colors of cryptolockers, but the new CTB-Locker variant says it all. The world of cybercriminals is investing in how to reinvent cryptolockers.
Before, CTB-Locker, or Onion Ransomware, differed from other ransomware in the usage of the Tor Project’s anonymity network to shield itself from takedown efforts that rely largely on static malware command and control servers. Its use of Tor also helped evading detection and blocking. Another thing that protected CTB-Locker controllers was accepting as payment only Bitcoins, the decentralized and largely anonymous crypto-currency known.
A new variant of the CTB-Locker targets web servers only, and to our knowledge it has already successfully encrypted web-root files in more than 70 servers located in 10 countries.
In this blogpost I will take you into the “lion’s den”, after victims were kind enough to share the cryptors that had been deployed into their web servers.
Step 1: defacement
This new variant aims to encrypt web servers and demand less than half a bitcoin as a ransom (~150 USD). If payment isn’t sent on time the ransom is doubled to approximately 300 USD. When paid, the decryption key is generated and is used to decrypt the web server’s files.
It has become clear that the web servers infected with this variant were targeted due to a security hole in their web server. Once exploited, the website is defaced. Defacement is a well-known method for hacking groups to show their victims they mean business. The most recent cases we’ve witnessed are not random, but mostly about political affiliations and cultural perspectives.
In this case, the defacement, which contains a replacement of the main php/html page, is used as the message carrier and contains all the means necessary for the attack to leave the right impression on the victim. We will deep-dive into it in the next steps.
It is important to mention that the original code is not deleted. It is stored safely in the web root with a different name in an encrypted state.
The message
As variants of malware of this kind are based on the simple fact that a victim cares more about his content than about paying a ransom, the authors usually leave a very detailed message for everyone to see.
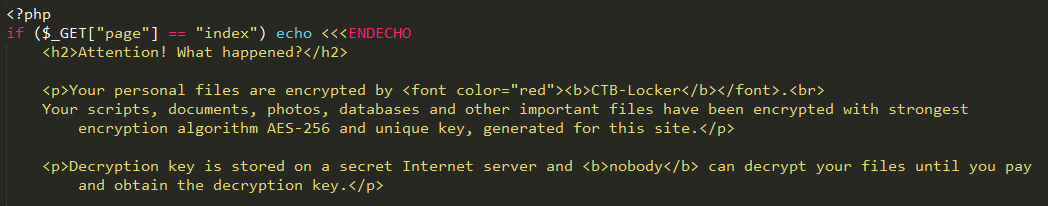
The following quote is a part of the information that is left on the main page:
The decryption key is stored on a remote server, but the attackers were “kind enough” to allow the victim to decrypt two files free, as a sign of authenticity.
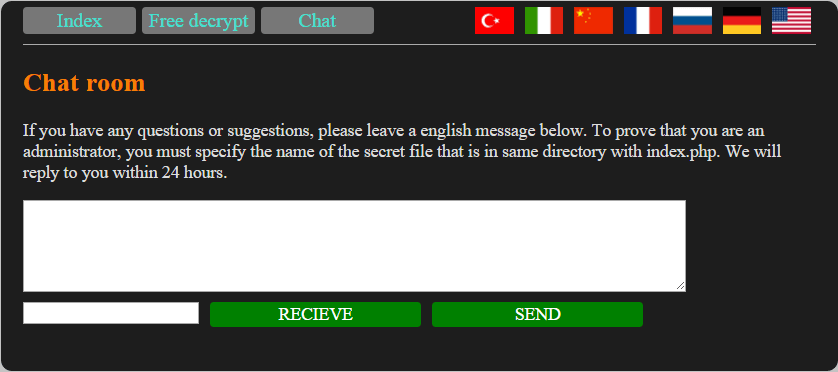
The other function that exists on the attacked website allows the victim to communicate with the attacker via chat: it requires a personal signature/code which is available for victims only.
At the moment, no decryption tool exists in the wild, thus there is no way to decrypt the files encrypted by the new CTB-Locker. The only way to remove this threat in a matter of seconds is to keep file backups in a separate location.
Although this seems like a big concern, we tend to believe that it is not. Large websites tend to have multiple versions of their content, spreading over a number of webservers. In many other cases, they are supervised and tested by professional security penetration testing firms and so are constantly under the magnifier.
Step 2: encryption process
We still don’t know how the CTB-Locker is being deployed on web servers, but there is one common thing among many of the attacked servers – they use the WordPress platform as a content management tool. WordPress contains many vulnerabilities in its non-updated versions and we already seen critical vulnerabilities presented last year. In addition, WordPress also has another weak spot – plugins. Those tiny enhancement features helps WordPress become what it is – a leader in the world of CMS. However, having third party plugins also makes the server more vulnerable to attacks, as plugin authors are not committed to any type of security measurements.
Once the malware author is inside WordPress system, he is able to replace the main website file and execute the encryption routine. The main file is renamed and saved in an encrypted state.
Two different AES-256 keys are deployed to the victim server:
- create_aes_cipher($keytest) – encrypts the two files which can be decrypted free.
- create_aes_cipher($keypass) – encrypts the rest of the files hosted on the server web root.
The two files are chosen by the authors and their names are saved in a text file.
The create_aes_cipher() accepts one parameter as the key and sends it to the standard Crypt_AES() function:
|
1 2 3 4 5 6 |
function create_aes_cipher($key) { $aes = new Crypt_AES(); $aes->setKeyLength(256); $aes->setKey($key); return $aes; } |
When encrypting the site, the script first uses the test key to encrypt the two files that will be used for free decryption. It will then generate a list of files that match specific file extensions and encrypt them using AES-256 encryption. The extensions that will be encrypted are read from the ./extensions.txt file and are currently:
Files that contain the following strings will be excluded from the encryption process:
- “/crypt/”
- “secret_”
In addition, files which are populated with data that will later assist the user with the decryption process would obviously be excluded as well.
- ./index.php – as described above, this file is the main door for the victim to analyze the attack and contains PHP code of the encryption/decryption routine.
- ./allenc.txt – contains a list of all encrypted files.
- ./test.txt – contains the files which are freely available for decryption.
- ./victims.txt – contains a list of all the files that are being encrypted or have already been encrypted.
- ./extensions.txt – contains the list of file extensions (see above).
- ./secret_ – as said, the victim is required to identify himself before the free decryption or chat is even possible.
On the main page of the CTB-Locker, attackers are using JQUERY to query proxy servers and verify payments. The following code was found in the page source code and the servers listed on the top are proxies which are used as another layer of protection, instead of the main server of the attackers:
Proxy servers which are part of the decryption process:
| http://erdeni.ru/access.php |
| http://studiogreystar.com/access.php |
| http://a1hose.com/access.php |
The ransomware servers are not permanent and are being replaced by new ones every certain period of time. We have identified the threat actor inspecting the server logs and analytics, as sometimes different checks resulted in the server shutting down and turned back on.
Step 3: proxy to C&C
The attackers are utilizing servers which were already attacked to traffic through another layer of protection. On a victim server’s source code, a JavaScript code reveals how the decryption process is sent through three different servers randomly, however those are not the C&C.
The above screenshot was taken from the access.php page, supposedly located in each one of the bot servers used as a proxy for the decryption process.
In white block is the actual C&C which has been hardcoded on each of the PHP pages (access.php).
When POST request is being sent with the right parameters, a socket instance is being created and sends a connect beam to the attacker’s C&C server. Later it is being determined if the decryption process succeeded.
Free decrypt
The ransomware allows the victim to freely decrypt not more than two files. It is not for the victim to choose, since the files are pre-chosen and can be found in the malware’s designated file as listed above. The two files are randomly picked during the course of the encryption process.
The following image is an illustration of the free decrypt module:
In order to decrypt the two free files, the victim is required to enter the secret_ file name. Once you click the DECRYPT IT FREE button, the client-side script builds a POST request and sends it to one of the C&C servers. We were able to imitate the PHP calculation and run the exit() function of the free decryption routine:
The following is the PHP code at the back-end. The function secret_ok() verifies the identity of the victim, based on his domain name and other indicators:
|
1 2 3 4 |
if (isset($_GET['dectest']) && secret_ok()) { decrypt_files('test.txt', $_GET['dectest']); exit('Congratulations! TEST FILES WAS DECRYPTED!!'); } |
Threat actor’s chat room
The ransomware also includes functionality to communicate with the malware authors. As already said, the victim is required to use the secret_ key in order to open the chat. Without it, the chat will remain unresponsive.
We have come to the conclusion that ransomware is the new-generation malware for an attacker interested in financial gain. They are very effective, there is no solid solution against this threat thus far, and they are flexible to attack not only desktop operating systems, but now web servers as well.
We strongly recommend updating software regularly. In addition, third party software must not be trusted automatically by its hash. This identifier can be changed by an attacker once a server has been compromised. Be sure to use other routine checks to ensure that the software is legitimate. We urge anyone to backup all important data; and to be cautious about emails which are not specifically meant for the user, or attractive ads that appear online.
CTB-Locker is back: the web server edition





























Jomar
what solution for this problem ?
Ido Naor
Hi Jomar,
Thank you for your question. Defending against CTB-Locker for web servers is not an easy task and it requires special steps to be done on a weekly/monthly basis:
1) Backup all your code and releases on a separate machine.
2) Consult a security firm to conduct penetration testings and close potential web/network vulnerabilities
3) Update all 3rd party software such as CMS
4) Keep track of any anomaly using security monitoring tools
Attackers are after the payment, hence as long as you can load all the data from backup you can restore your website without going through the decryption process which includes the payment.
Hope that clears stuff,
Ido
Hendra yoga
i see CTB locker source code on github , but it doesn’t work anymore on my server ?? is my server use antivirus ??
Ido Naor
Hi Hendra,
You’re correct. The code can now be found in many places around the web. It was leaked and spread via kernelmode forums.
It’s hard to answer the question as I am not aware of which code you have been running and on which environment.
Regards,
Ido
Daniele
Hello, thanks for the heads up. Does this involve Linux servers too?
Ido Naor
Hi Daniele,
My pleasure.
The CTB-Locker is not limited to an operating system, but to the web-server instance its running on. It is a PHP-based ransomware, which means it requires a PHP interpreter to execute the code. Once the code is executed, it will rewrite (encrypt) files using the AES standard library.
I hope that answers your question.
Ido
Daniele
Thanks. So it will infect a particular website only? I mean, it shouldn’t be able to infect all files inside the var/www/html folder if it’s php based.
Ido Naor
It will encrypt only file extensions with the extensions listed in the text file “extensions.txt”.
Daniele
I know, but I meant something else. Let’s say it infects the whatchamacallit.com website. This website’s files reside in a /var/www/html subdirectory. Will the malware be able to see other directories with other websites too? It shouldn’t, it would need root access to do that.
Ido Naor
Good question @Daniele,
The answer is simple: In this type of attack, the author is looking for web/network vulnerabilities and exploit them to inject his ransomware. If the exploit he found gains him with the access to all the /var/www/html subdirectory, the ransomware code will encrypt all the files which reside under that tree. I advise you to properly segment web directories with unique permissions for each group and/or user.
Ido
Daniele
Thanks. Everything is segmented, all database users and cms users have access only to their directories. The only way the ransomware would be able to infect the whole tree would be if it obtained root access, which I think is impossible.
Anyway I have a very thorough backup policy, the server is backed up to different locations many times a day.
W.A.Weathers
Ido Thanks for the great job you do, its easy to be critical but nobody says thanks these days