
A year ago — everything changed. In an effort to stem the tide of a rapidly spreading pandemic, the world shut down. Shops were forced to shut their doors, and whole countries were placed on stringent lockdowns. Schools were closed around the world, with more than one billion children affected, and the vast majority of companies had to switch to remote work, sometimes with only a week’s notice. As life for large swaths of the population moved entirely online, the cybercriminals were ready.
In fact, not only did the way people lived and worked changed, but so did the methods and tactics used by criminals on the Internet looking to exploit the massive increase in online traffic.
With the approval of several vaccines against the coronavirus, a post-pandemic future is finally in sight. However, there is still a long way to go before life returns to normal, and some changes, such as remote work, look like they are here to stay — as do the new cyber threats that emerged alongside these shifts.
On the anniversary of the global shutdown, Kaspersky experts decided to take a look back at how the threat landscape has evolved since the beginning of the pandemic — and what that means for users in the years to come.
From targeted attacks to exploiting all things COVID-related, the biggest trends in spam and phishing
Phishing is still one of the most effective types of attacks because it exploits users’ emotions, particularly their fear and anxiety. With both of the former heightened thanks to the pandemic, phishing attacks proved to be a highly lucrative attack vector for cybercriminals.
In 2020, criminals launched a variety of scams that exploited the pandemic topic from just about every angle, from advertisements to masks when they were in short supply to special refunds from the government.
A fake landing page for a mask advertised in a phishing email. Users are prompted to put in their payment details for a mask that will most likely never arrive
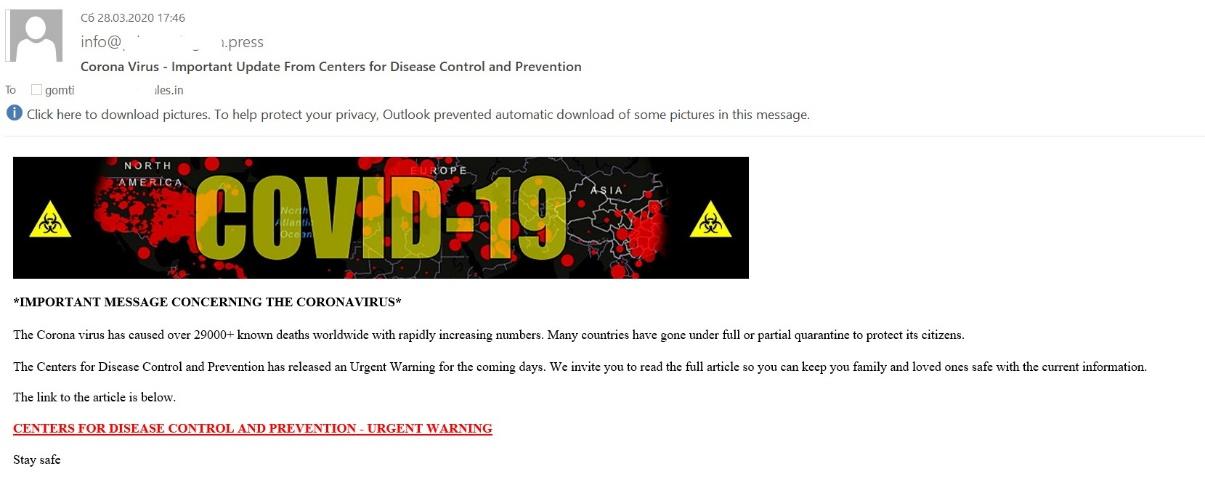
Scammers often imitated leading authority figures on the pandemic, like the CDC and the World Health Organization, to give their emails additional authority — and increase the chances that users would click a malicious link. Once clicked, users could end up inadvertently downloading a range of threats on their computer, from various Trojans (malicious files that allow cybercriminals to do everything, from deleting and blocking data to interrupting the performance of the computer) and worms (files that are capable of destroying, blocking, modifying or copying data). Of course, in other instances, such as those involving advertisements for masks, the primary goal is stealing money and/or payment information.
An email supposedly from the CDC claiming that there is an urgent update regarding the pandemic
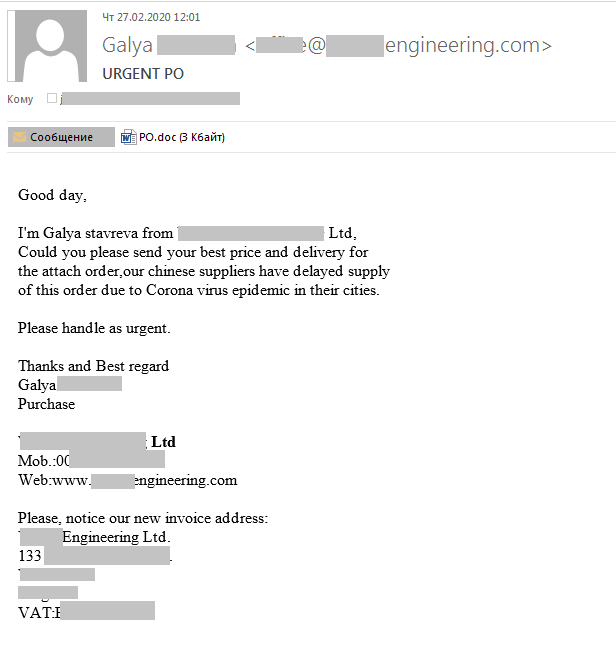
Surprisingly, one of the most common themes exploited revolved around delivery disruptions. A standard part of business operations is making various business orders, and criminals used the uncertainty surrounding mail services during the pandemic to trick users into downloading malware. They would send emails claiming that, due to COVID, an important delivery had been delayed and that the target must verify the new delivery information (a situation easy to believe in the middle of a pandemic) in order to receive it. However, upon clicking the attachment, the users would download Trojans ranging from spyware to backdoors.
A phishing email claiming that a delivery has been delayed and containing a malicious attachment
In fact, in 2020, delivery services became one of the top ten organization types targeted by phishers.
Remote work — and the rise of brute-force attacks
With many companies forced to close their doors with little notice, few had time to put the proper security measures in place. The result was that many became vulnerable to a host of new attacks as their employees began logging in to corporate resources from personal devices and on unsecured networks. Chief among them? Brute-force attacks against the RDP protocol, Microsoft’s proprietary protocol that enables users to access Windows workstations or servers. RDP is one of the most popular remote access protocols used by companies, making it a favorite target for attackers. In a brute-force attack, attackers attempt to randomly guess a username and password for the RDP connection by trying different combinations until they guess the correct one — and gain access to the confidential corporate resources.
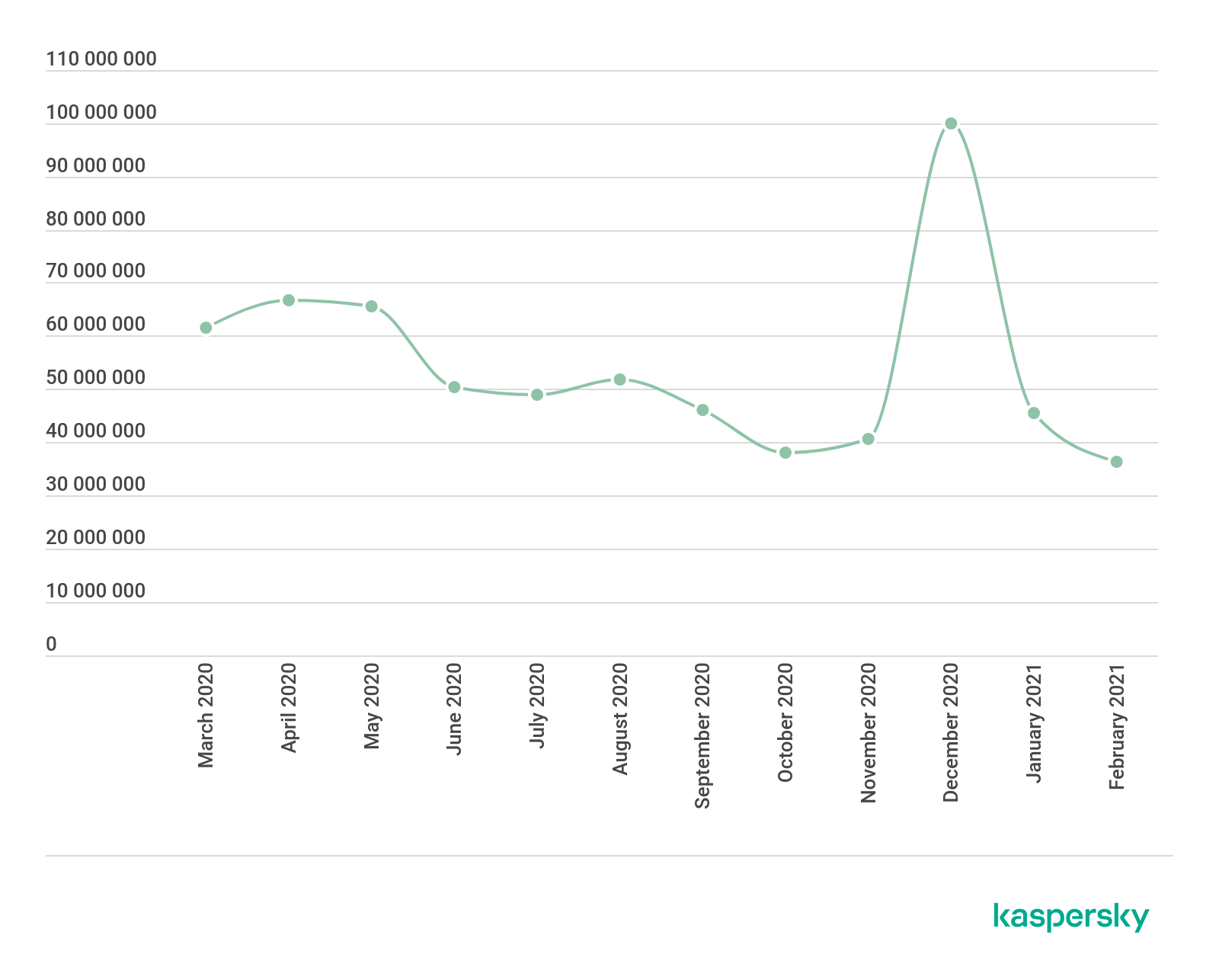
In spring of 2020, the number of brute-force attacks against the RDP protocol skyrocketed across almost the entire planet.

The number of brute-force attacks against the RDP protocol (download)
As shown in the graph, as soon as lockdowns were announced, the number of brute-force RDP attacks radically increased — from 93.1 mln worldwide in February to 277.4 mln in March — a 197 percent increase. While the number of attacks has ebbed and flowed as the pandemic continued, the number of attacks has not returned to pre-pandemic levels. In fact, after new lockdowns were announced in the winter, RDP attacks once again displayed an upward trend. In February 2021, there were 377.5 mln brute-force attacks — a far cry from the 93.1 mln witnessed at the beginning of 2020.
Virtual communication platforms under attack
With the world on lockdown, Internet demand reached unprecedented levels. Large companies from Facebook to Netflix to YouTube, were forced to reduce their video quality in order to keep up with demand. And all those extra users meant a host of new targets for criminals. By the May of 2020, the average daily number of attacks blocked by Kaspersky Web Anti-Virus had increased by 25%. In fact, the number of web attacks, after displaying a decline in the summer of 2020, reached a new peak in the December as much of the world was facing a second wave of the pandemic.
Number of web-based attacked blocked by Kaspersky Web Anti-Virus from March 2020 through February 2021 (download)
A large portion of users’ time spent online was dedicated to meeting and collaborating virtually. That is why meeting and messenger apps, like Zoom and Teams, became a popular lure for distributing cyberthreats.
Upon examining popular meeting and videoconferencing apps, including Zoom, Webex, and MS Teams, Kaspersky researchers noticed a growing number of malicious files spread under the guise of these apps’ names.
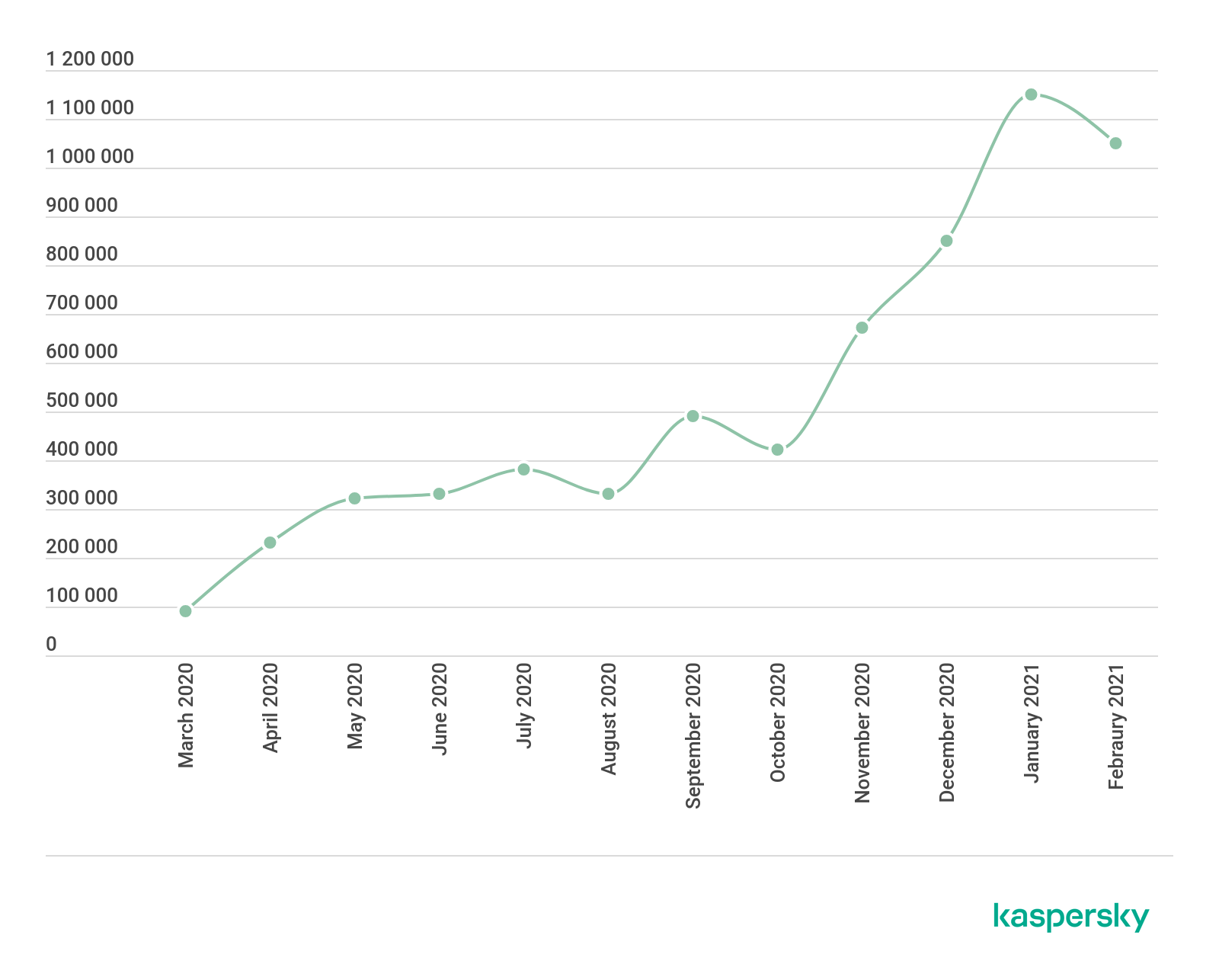
The number of malicious files spread under the guise of popular meeting apps (Webex, Zoom, MS Teams, HighFive, Lifesize, Join.me, Slack, Flock, Gotomeeting) (download)
In the January of this year, there were 1.15 mln such files detected — the highest number since the lockdown began. These files are often bundled as part of seemingly legitimate application installers, which can be encountered in several ways: through phishing emails claiming to have notifications or special offers from their platforms or through phishing web pages.
Lessons learned
Peoples’ lives have become increasingly digital for years, and this is a trend that is likely to continue. It is still unclear when travel will get back to normal and with remote work staying in the picture, videoconferencing and meeting apps will continue to be in high demand. Of course, the more time users spend online, the more vulnerable they are to security risks.
While the pandemic may be heading into its final phases, there are still new topics for phishers and scammers to exploit, like health passports for travel or vaccine distribution, and chances are they will exploit them. It is important that users view any email or website referencing the pandemic with a skeptical eye. What is more, recent events have shown how willing criminals are to take advantage of crisis, and, while this pandemic will subside, it certainly will not be the last crisis.
With many organizations already stating that they will continue to make remote work an option and/or adopt a hybrid model, RDP is not going anywhere — and neither are attacks against the protocol. That means businesses need to reevaluate their usage of RDP and learn how to secure remote access.
If there is has ever been a time for companies to reevaluate and bolster their security strategy, that time is now.





















COVID-19: Examining the threat landscape a year later