
Brazilian cybercriminals have always been very active in the creation and dissemination of banking Trojans among their compatriots. But now they are redirecting their attacks beyond the borders of Brazil to target banks in Europe. In recent months we have seen several Trojans developed in Brazil attempting to attack financial institutions in Europe, especially in Spain and Portugal.
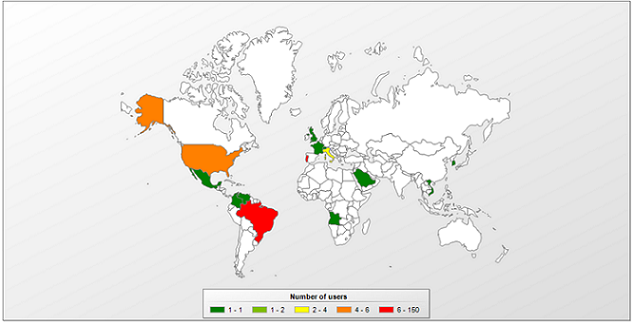
As a rule, European banks were attacked by sophisticated Trojan bankers like SpyEye and by Zeus gangs, but now they face an onslaught from Brazilian Trojans. Our statistics show the dissemination of a specific variant affecting customers in Brazil and Portugal:
Trojan-Banker.Win32.Banbra.akzy
Inside the code of this Trojan we can see the name of some of the Brazilian and Portuguese banks targeted in the attack:
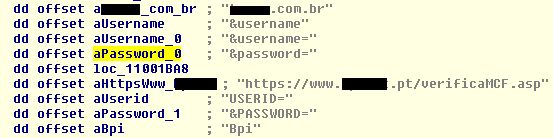
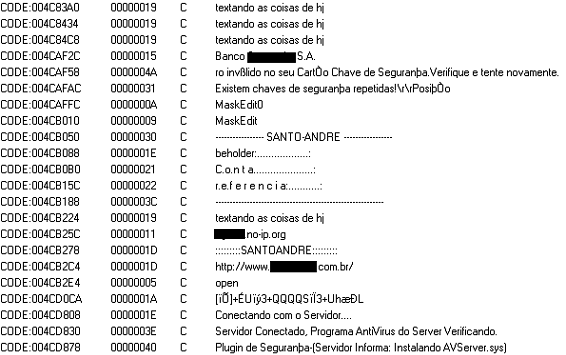
In other similar Trojans we found a function capable of stealing credentials from Brazilian customers:
As well as customers of banks in Cape Verde and Spain:
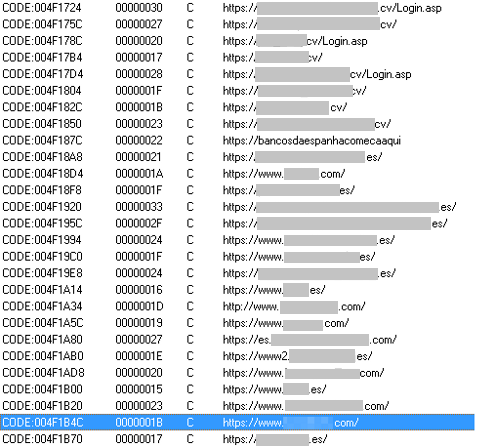
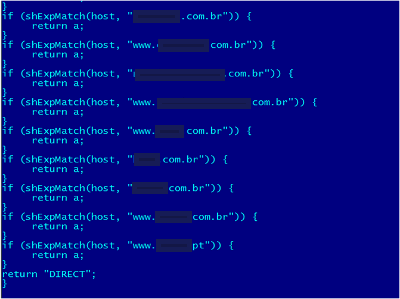
In a malicious proxy script commonly used in MitB attacks detected by our heuristic engine, we can see a list of Brazilian banks redirected to a malicious host – and surprisingly, a bank from Portugal is also targeted in the attack:
All these Brazilian Trojans demonstrate that cybercrime has no borders!






















Brazilian Trojans beyond borders