
As always, when big news appear in the press the bad guys start blackhat SEO campaigns in popular search engines trying to lure users to install Rogueware.
It’s not different this time, with the top news about Osama’s Bin Laden death being everywhere. The bad guys were quite fast and started to poison searches results in Google Images.
Some of the search results are now leading users to malicious pages:
When clicking an image in the results page, the user will be redirected to one of the malicious domains:
***-antivirus.cz.cc/fast-scan/
***pe-antivirus.cz.cc/fast-scan/
Both domains are offering a copy of the rogueware known as “Best Antivirus 2011”:
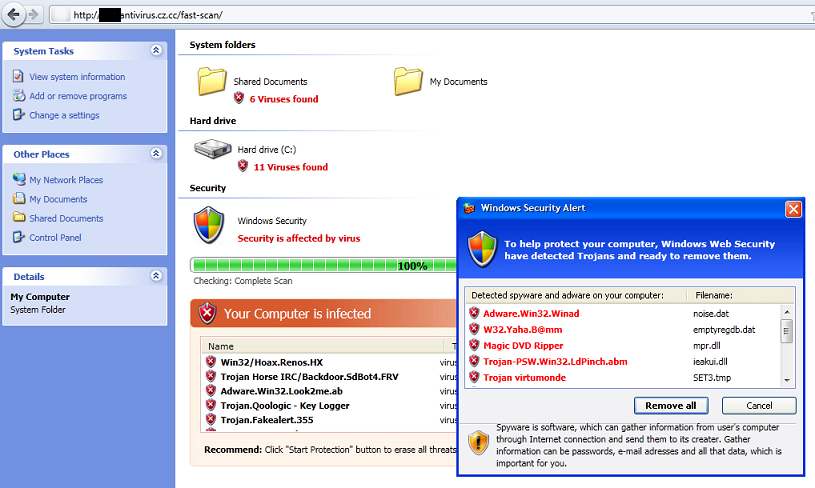
This rogueware is already detected by Kaspersky as Trojan.Win32.FakeAV.cvoo
When searching, even for images, be careful!





















Blackhat SEO and Osama Bin Laden’s death