
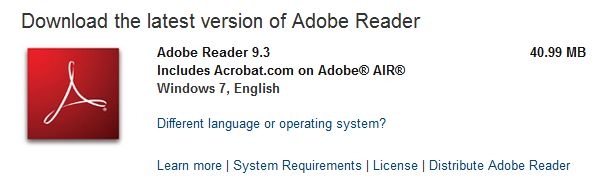
If you’re familiar with installing Adobe Reader, you probably know that often, the version available for download from the Adobe site is out of date and needs immediate patching. For instance, if you tried to download Adobe Reader yesterday, the release on the site was 9.3. The most current version is actually 9.3.3.
Today Adobe is introducing something new. They’re introducing what they call “chained installers”, which include all available patches. While it’s been possible to (manually) create chained installers for corporate environments, a ready-made chained installer is new.
This latest effort by Adobe is designed to ensure a higher penetration rate for its latest releases. Although I’d still much rather see Adobe enabling automatic updates in its products, this latest move is definitely welcome.





















Adobe chained installers increase security