
I just came across a suspicious PDF file, so I decided to take a deeper look. Once the file was unpacked, I got an xml file with TIFF image. However, the whole thing looked very strange. The whole thing looked very fishy, and ultimately, it turned out that the xml file contained an exploit for CVE-2010-0188.
I thought it was a bit odd that we hadn’t come across files like this before, so I decided to tak a look at stats for this vulnerability:
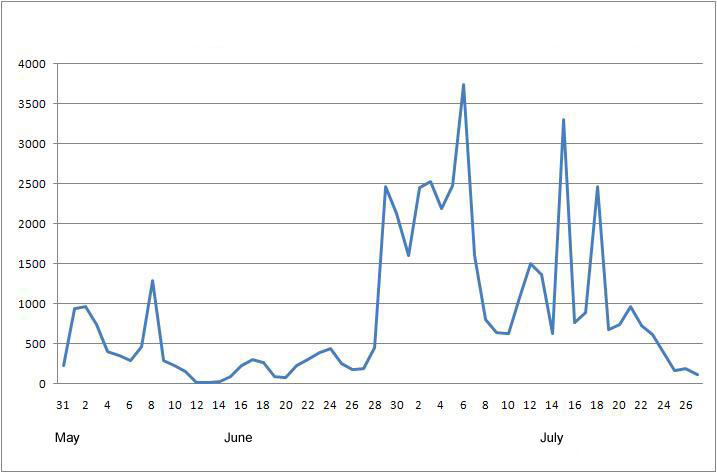
CVE-2010-0188 exploit statistics 2010
The graph shows that malware exploiting CVE=2010-0188 started spreading actively at the end of June. It was pretty much a rarity until then. Maybe the virus writers needed a few months to catch up with creating exploits for the new hole in Adobe – who knows?
When I took a closer look, it turned out that the PDF was mainly designed to download and launch another file, Trojan-Dropper.Win32.Zbot.cm. Which, in its turn, is mainly designed to secretly install Zbot (ZeuS) to the system and to combat antivirus software.
I was able to get a final example of Zbot, but it turned out to be encrypted and obfuscated. I then got its dump and decrypted strings, which included a clear link to the banking site under attack, the bot’s http requests and some of the commands used by the botnet C&C:

Part of the decrypted Zbot file
This is the first example of an encrypted Zbot variant spreading via CVE-2010-0188. Clearly, the guys behind this program aren’t sitting on their hands, but working on the most up-to-date methods of delivering their malware to end users.






















Zbot and CVE2010-0188