
In our practice, we often encounter cases where messages with a malicious attachment are mass-mailed to many addresses at the same time. Recently, though, we saw a series of messages persistently sent to the same email address. Apparently, the attacker’s main goal was to infect that computer – all emails, no matter what their headers were, contained Email-Worm.Win32.NetSky.q. This worm’s characteristic feature is that it spreads via email attachments. After infecting a computer, the worm finds all the email addresses in it and copies itself to them, using specific short phrases and avoiding any email addresses that may be directly associated with IT security providers, such as antivirus companies.
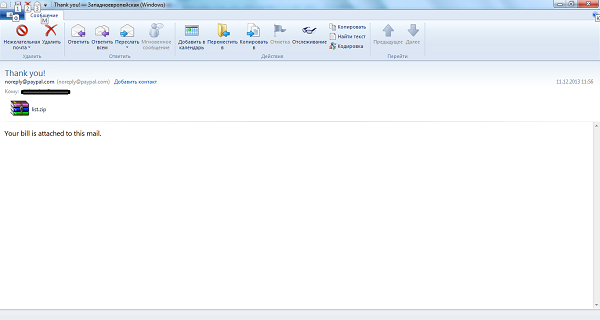
The first message we detected purportedly came from the PayPal payment system. The text in the body of the letter said that there was a bill for the user in the attachment.
However, alert users might recall that PayPal typically includes billing information in the body text, and not in an attached file.
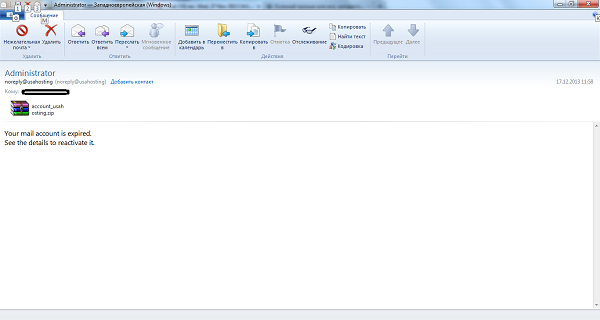
Another email came in the name of USA Hosting administration. To entice the user into opening the attachment, the attackers say that the user’s “mail account has expired”, and suggest that the user reactivates it with the “details” in the attachment.
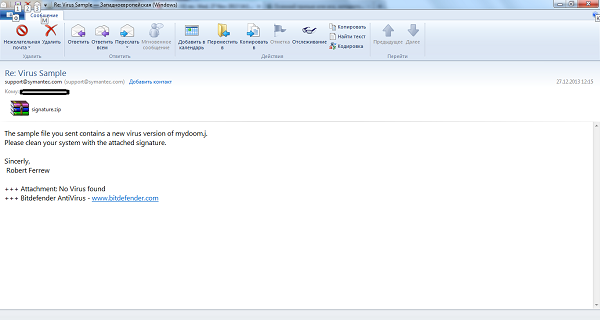
The third email allegedly came from the antivirus vendor Symantec. The message said that the user’s computer was infected with a new virus. To delete it, the user should download the attached antivirus signatures. Again, an alert user might be suspicious of the fact that the signature was from a rival antivirus company, Bitdefender.
All these letters arrived during the same month, and, although they had different subjects, they shared the same goal of infecting the user’s computer and spreading malware across the network. Therefore, we would like to remind the user that extra caution is needed when dealing with any email that arrives with attachments. It’s important to remember that any official letter should have the appropriate design – and authentic logos and signatures. If users are uncertain about the identity of the sender, it’s worth contacting the company’s technical support line for confirmation. Applying sensible precautions to incoming mail, combined with a reliable security product, helps to keep your computer safe from the perils of cyberspace.






















Worm Attack! Your Mailbox is Under Threat