
We are seeing an increase in spam sent via the MS Windows Messenger service. Spammers are abusing a feature in the service to trigger fake error or warning messages from the messenger service.
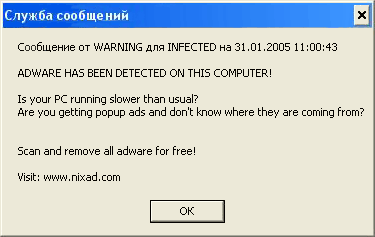
Very often, the message warns users that a significant number of spyware programs have been detected on their machine and recommends that users download an anti-spyware program.
Naturally, this is an attempt to trick users into downloading Trojans, in the worst case scenario, or in the best case scenario, useless utilities that imitate spyware detection. In any case, adware and spyware are neither detected nor removed.
What we are seeing is virus writers adapting the never-ending social engineering technique of picking up on a well-publicized security issue. This time the media attention and public awareness of the term spyware is being exploited.
We urge users to be aware that such messages are fake and to avoid downloading any programs advertised in this manner. This kind of spam can be prevented on PCs where you have admin rights by disabling the Messenger service C:WINDOWSSystem32svchost.exe -k netsvcs or Control Panel -> Administrative Tools -> Services -> Messenger.
Read more about MS Windows Messenger Service:






















Windows Messenger spam