
1NewI-Worm.Mimail.c
34.57%
2NewI-Worm.Mimail.g
15.16%
3– 2I-Worm.Swen
13.01%
4+ 2 I-Worm.Sober
12.14%
5– 2I-Worm.Mimail.a
4.95%
6re-entry I-Worm.Klez.h
2.18%
7re-entryI-Worm.Lentin.m
1.91%
8re-entryI-Worm.Dumaru.a
1.25%
9re-entryI-Worm.Lentin.g
1.12%
10NewI-Worm.Mimail.h
0.97%
11– 3 I-Worm.Sobig.f
0.86%
12NewI-Worm.Hawawi.g
0.73%
13NewI-Worm.Mimail.e
0.67%
14– 12 I-Worm.Tanatos
0.53%
15NewI-Worm.Mimail.f
0.45%
16NewI-Worm.Mimail.j
0.42%
17re-entryI-Worm.Lovelorn.a
0.38%
18– 14 Worm.Win32.Lovesan
0.36%
19– 7Backdoor.Agobot.3.gen
0.33%
20– 14 Backdoor.SdBot.gen
0.18%
Other malicious programs*
7.84%
| Position | Change | Name | Percentage by Occurrance |
|---|---|---|---|
| * not included in the top 20 | |||
November’s list of the 20 most widespread viruses is marked by the appearance of several new variations of the Mimail network worm, most notable is I-Worm.Mimail.c which heads the chart with 34.57% of all registered incidences. Six new modifications of Mimail made the top twenty in November, and altogether accounted for nearly 62%. This dominating performance is the result of the code from the Mimail family’s first variant being published on the Internet.
Mimail managed to crowd the previous month’s leader, I-Worm.Swen, down to third place, while the undisputed leader for 2003, Sobig.f, slid down to 11th place. Making their return to the stage are ‘old friends’ Klez and Lentin.
Other worms making their return to the Top Twenty are Dumaru and Lovelorn, with Dumaru.a quickly taking 8th position.
Boldly moving up two spots is the German worm, Sober, which now maintains fourth place.
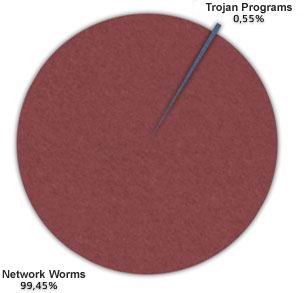
November saw Trojan programs lose considerable ground with only two malicious programs of this type (backdoor utilities used to gain unsanctioned access) – Agobot and Sdbot, filling the final two spots and dropping 7 and 14 places respectively from the previous month.
For November, Internet worms virtually monopolized the virus statistics, allowing Trojan programs a bit more than one half of one percentage point, while computer viruses were knocked completely off the list.
Malicious Program Types
Summary:
- Making their debuts on the list are: Mimail worm family – c,e,f,g,h,j, and Hawawi.g
- The only virus improving its position is Sober
- Dropping are Swen, Mimail.a, Sobig.f, Tanatos.b, Lovesan, Agobot, SdBot
- Returning to the hit parade are: Klez.h, Lentin.g and Lentin.m, Dumaru.a and Lovelorn


















Virus Top Twenty for November 2003